Sonicwall TZ205 Site to Site VPN
Hi Guys,
I am setting up a Site to Site VPN with 2 Sonicwall TZ205's and i cannot get them to work correctly. The Tunnel is connected, but the clients on either side cannot talk to each other. If i ssh in to the Sonicwall's i can ping the gateways and the clients from the Sonicwall's themselves, but no other traffic is going across the VPN.
I am setting up a Site to Site VPN with 2 Sonicwall TZ205's and i cannot get them to work correctly. The Tunnel is connected, but the clients on either side cannot talk to each other. If i ssh in to the Sonicwall's i can ping the gateways and the clients from the Sonicwall's themselves, but no other traffic is going across the VPN.
ASKER
I see the successful pings when pinging from the sonicwalls
09:40:50 Nov 02 171 VPN IPsec Dead Peer Detection xxx.xxx.118.1 50585 xxx.xxx.113.110 4500 RECEIVED<<< ISAKMP OAK INFO (InitCookie:0xb400790b9ab5
09:37:50 Nov 02 171 VPN IPsec Dead Peer Detection xxx.xxx.113.110 4500 xxx.xxx.118.1 50585 SENDING>>>> ISAKMP OAK INFO (InitCookie:0xb400790b9ab5
09:36:02 Nov 02 171 VPN IPsec Dead Peer Detection xxx.xxx.113.110 4500 xxx.xxx.118.1 50585 SENDING>>>> ISAKMP OAK INFO (InitCookie:0xb400790b9ab5
But I do not see anything else in the log. My remote sonicwall log is showing this though.
10:17:15 Nov 02 1233 Firewall Settings Link-Local/Mult
icast IPv6 Packet W0 X0 fe80::a6:b401: 86e6:4356 64531 ff02::1:3 5355 17 Unhandled link-local or multicast IPv6 packet dropped
10:17:10 Nov 02 1233 Firewall Settings Link-Local/Mult
icast IPv6 Packet W0 X0 fe80::a6:b401: 86e6:4356 65087 ff02::1:3 5355 17 Unhandled link-local or multicast IPv6 packet dropped
10:16:08 Nov 02 1233 Firewall Settings Link-Local/Mult
icast IPv6 Packet W0 X0 fe80::a6:b401: 86e6:4356 65219 ff02::c 1900 17 Unhandled link-local or multicast IPv6 packet dropped
10:16:05 Nov 02 1233 Firewall Settings Link-Local/Mult
icast IPv6 Packet W0 X0 fe80::a6:b401: 86e6:4356 65219 ff02::c 1900 17 Unhandled link-local or multicast IPv6 packet dropped
10:16:02 Nov 02 1233 Firewall Settings Link-Local/Mult
icast IPv6 Packet W0 X0 fe80::a6:b401: 86e6:4356 65219 ff02::c 1900 17 Unhandled link-local or multicast IPv6 packet dropped
10:15:15 Nov 02 1233 Firewall Settings Link-Local/Mult
icast IPv6 Packet W0 X0 fe80::a6:b401: 86e6:4356 50626 ff02::1:3 5355 17 Unhandled link-local or multicast IPv6 packet dropped
10:13:56 Nov 02 1233 Firewall Settings Link-Local/Mult
icast IPv6 Packet W0 X0 fe80::a6:b401: 86e6:4356 59188 ff02::1:3 5355 17 Unhandled link-local or multicast IPv6 packet dropped
10:13:22 Nov 02 1233 Firewall Settings Link-Local/Mult
icast IPv6 Packet W0 X0 fe80::a6:b401: 86e6:4356 65219 ff02::c 1900 17 Unhandled link-local or multicast IPv6 packet dropped
09:40:50 Nov 02 171 VPN IPsec Dead Peer Detection xxx.xxx.118.1 50585 xxx.xxx.113.110 4500 RECEIVED<<< ISAKMP OAK INFO (InitCookie:0xb400790b9ab5
09:37:50 Nov 02 171 VPN IPsec Dead Peer Detection xxx.xxx.113.110 4500 xxx.xxx.118.1 50585 SENDING>>>> ISAKMP OAK INFO (InitCookie:0xb400790b9ab5
09:36:02 Nov 02 171 VPN IPsec Dead Peer Detection xxx.xxx.113.110 4500 xxx.xxx.118.1 50585 SENDING>>>> ISAKMP OAK INFO (InitCookie:0xb400790b9ab5
But I do not see anything else in the log. My remote sonicwall log is showing this though.
10:17:15 Nov 02 1233 Firewall Settings Link-Local/Mult
icast IPv6 Packet W0 X0 fe80::a6:b401: 86e6:4356 64531 ff02::1:3 5355 17 Unhandled link-local or multicast IPv6 packet dropped
10:17:10 Nov 02 1233 Firewall Settings Link-Local/Mult
icast IPv6 Packet W0 X0 fe80::a6:b401: 86e6:4356 65087 ff02::1:3 5355 17 Unhandled link-local or multicast IPv6 packet dropped
10:16:08 Nov 02 1233 Firewall Settings Link-Local/Mult
icast IPv6 Packet W0 X0 fe80::a6:b401: 86e6:4356 65219 ff02::c 1900 17 Unhandled link-local or multicast IPv6 packet dropped
10:16:05 Nov 02 1233 Firewall Settings Link-Local/Mult
icast IPv6 Packet W0 X0 fe80::a6:b401: 86e6:4356 65219 ff02::c 1900 17 Unhandled link-local or multicast IPv6 packet dropped
10:16:02 Nov 02 1233 Firewall Settings Link-Local/Mult
icast IPv6 Packet W0 X0 fe80::a6:b401: 86e6:4356 65219 ff02::c 1900 17 Unhandled link-local or multicast IPv6 packet dropped
10:15:15 Nov 02 1233 Firewall Settings Link-Local/Mult
icast IPv6 Packet W0 X0 fe80::a6:b401: 86e6:4356 50626 ff02::1:3 5355 17 Unhandled link-local or multicast IPv6 packet dropped
10:13:56 Nov 02 1233 Firewall Settings Link-Local/Mult
icast IPv6 Packet W0 X0 fe80::a6:b401: 86e6:4356 59188 ff02::1:3 5355 17 Unhandled link-local or multicast IPv6 packet dropped
10:13:22 Nov 02 1233 Firewall Settings Link-Local/Mult
icast IPv6 Packet W0 X0 fe80::a6:b401: 86e6:4356 65219 ff02::c 1900 17 Unhandled link-local or multicast IPv6 packet dropped
Did you enable dhcp over VPN, then reboot the clients behind the sonicwall that is connecting to the other sonicwall?
Are you running IPv6?
Can you ping from PC to PC through the VPN?
Your logs indicate a NULL source IP address.
Can you ping from PC to PC through the VPN?
Your logs indicate a NULL source IP address.
ASKER
I am not using IPv6. I cannot ping PC to PC, that is the whole problem.
Well, your logs do reflect some IPv6 traffic. So if you're not using IPv6, then turn it off. But you still have not mentioned whether you turned on DHCP over VPN. You will need to at a minimum do that, so that machines on the remote Sonicwall can start receiving IP addresses from the main Sonicwall. Machines with static IP addresses will also need to be entered. I was just dealing with this kind of issue recently.
ASKER
Why would the machines need to receive a DHCP address from the main Sonicwall? I have a Sonicwall in another situation with DCHP enabled locally.
ASKER
So I took the static sonic wall from the site and brought it home. brought it back to defaults and set it up on my cable modem, I am still having the same issue. I can get the VPN to connect and see the correct stuff in the logs, but I cannot ping across the VPN. I tried enabling DHCP over VPN, but it doesn't work since the remote router cannot see the local ip of the static router.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
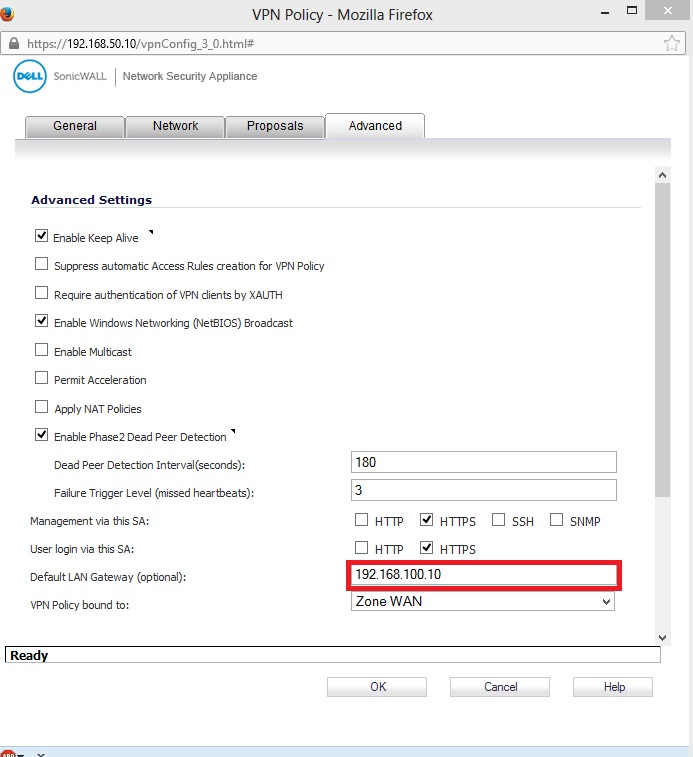
Thanks for the help, the issue with the VPN was i needed to enter the IP address of the remote router into the default gateway box on the advanced tab on both routers
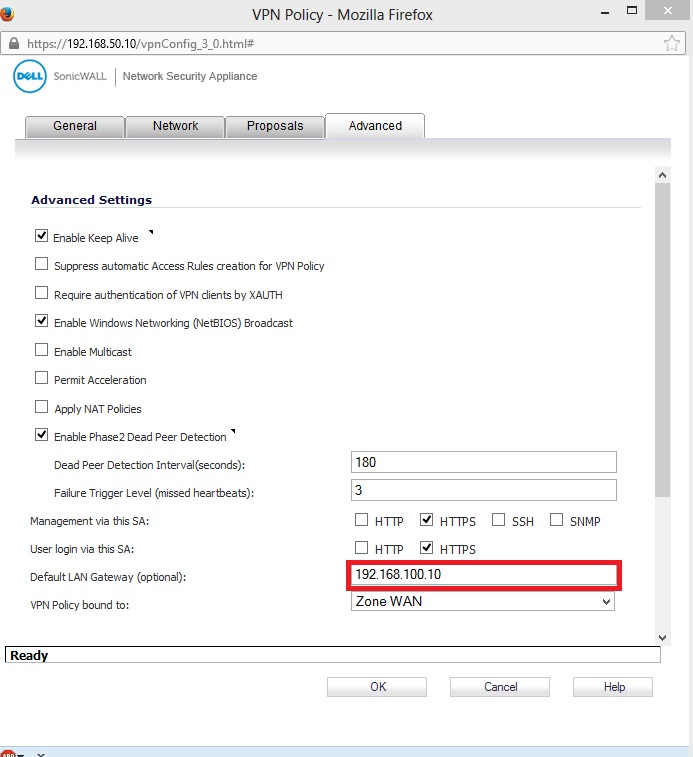
After that I was able to ping across the vpn fine.
I still am having one last issue. I need to use wireless as well as wired on one side, the other side will only have wired clients. I can ping wired clients from the wireless and vise versa on the local router, but only the wired clients can ping across the VPN the wireless clients time out.
After that I was able to ping across the vpn fine.
I still am having one last issue. I need to use wireless as well as wired on one side, the other side will only have wired clients. I can ping wired clients from the wireless and vise versa on the local router, but only the wired clients can ping across the VPN the wireless clients time out.
Yes, traffic not passing to or from a Wireless Type Zone is due to Access Rules NOT auto created (By Design).
After setting up a VPN policy in to tunnel interface mode, ensure a route has been created on both sides to route traffic to the appropriate network. Then proceed to check access rules on the side of the tunnel which has the wireless network.
When creating route policies in which the source is any and traffic is set to pass to a non-trusted zone, the access rules are not auto-created.
The rules will need to be added in two places. From VPN > WLAN and from WLAN > VPN.
They will be similar to rules that are created from VPN > LAN and LAN > VPN where the VPN network is the remote network.
After setting up a VPN policy in to tunnel interface mode, ensure a route has been created on both sides to route traffic to the appropriate network. Then proceed to check access rules on the side of the tunnel which has the wireless network.
When creating route policies in which the source is any and traffic is set to pass to a non-trusted zone, the access rules are not auto-created.
The rules will need to be added in two places. From VPN > WLAN and from WLAN > VPN.
They will be similar to rules that are created from VPN > LAN and LAN > VPN where the VPN network is the remote network.
Can you ping the firewalls from the clients?
Are you seeing anything in the logs when you try to ping from PC to PC (across the VPN)?
Make sure to enable all log categories...go to Log > Settings, make sure Logging is set to Debug and that all Categories are checked under log. Then test and post results.