AdminSDHolder - Inheritable Permissions
Hi Everyone,
I am having an issue where I cannot select the "Include Inheritable permissions from this objects parents" in active directory (Windows Server 2008 R2)
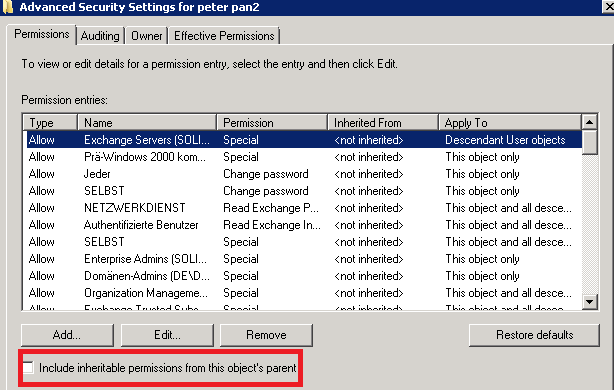
In fact I am able to select the box but within, 1 hour the box will become de-selected.
This causing our users having issues receiving emails on their Iphone's
After scratching my head for a while, I hit google and I believe I have narrowed down the problem to AdminSDHolder, Protected Groups and SDPROP. Which runs every hour and overwrites any changes I have made.
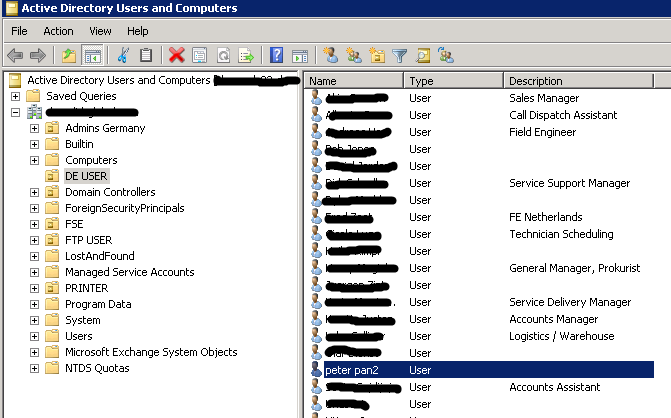
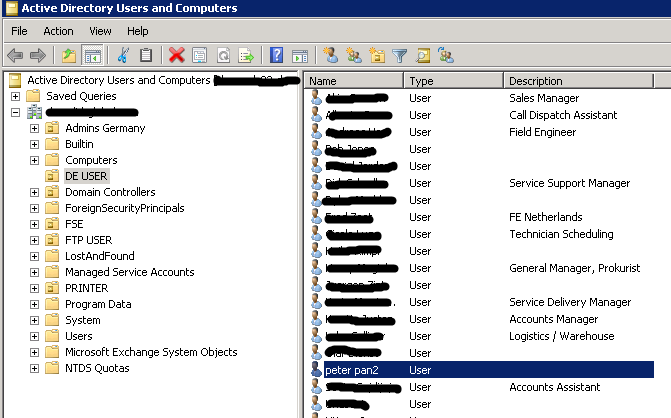
The Users are placed in an OU called "DE User" Thinking it may be a rpoblem with that OU, I took our test user "Peter Pan" and put him in the User OU. Unfortunately this made no difference and my permissions were still overwritten an hour later.
My question is, how can I stop, AdminSDHolder from overwriting these permissions short of totally killing it.
Any help would be greatly appreciated.
Regards
I am having an issue where I cannot select the "Include Inheritable permissions from this objects parents" in active directory (Windows Server 2008 R2)
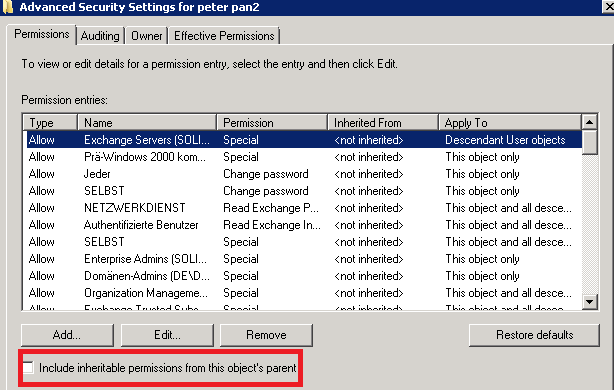
In fact I am able to select the box but within, 1 hour the box will become de-selected.
This causing our users having issues receiving emails on their Iphone's
After scratching my head for a while, I hit google and I believe I have narrowed down the problem to AdminSDHolder, Protected Groups and SDPROP. Which runs every hour and overwrites any changes I have made.
The Users are placed in an OU called "DE User" Thinking it may be a rpoblem with that OU, I took our test user "Peter Pan" and put him in the User OU. Unfortunately this made no difference and my permissions were still overwritten an hour later.
My question is, how can I stop, AdminSDHolder from overwriting these permissions short of totally killing it.
Any help would be greatly appreciated.
Regards
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Thanks for your help il be trying method 2 on that article ASAP, I would just like to add that the users I'm having problems with should all be standard users. Not admin rights etc.
Not sure exactly what has made the user accounts "privileged" and thus including in sdholder
Not sure exactly what has made the user accounts "privileged" and thus including in sdholder
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Thankyou
For some reason Domain Users group was among the protected groups, I followed method 2 as per Navdeep and all is well.
But thanks Rancy for making me double check the groups, although I didn't expect domain user to be one of these protected groups.
But a Get-ADUser -LDAPFilter powershell script help me see the groups that were protected.
For some reason Domain Users group was among the protected groups, I followed method 2 as per Navdeep and all is well.
But thanks Rancy for making me double check the groups, although I didn't expect domain user to be one of these protected groups.
But a Get-ADUser -LDAPFilter powershell script help me see the groups that were protected.
- Rancy