Trying out Windows 10 Tech Preview
Veteran in computer systems, malware removal and ransomware topics. I have been working in the field since 1985.
Published:
Browse All Articles > Trying out Windows 10 Tech Preview
I've been a Windows Secrets subscriber for over a decade (probably closer to 2). I recently saw this article on how to safely try out Windows 10 technical preview within a virtual machine. The article itself is an easy read and the instructions are excellent. I followed them and made a video of my experience located here. I am now in the process of trying out Windows 10. So far it looks a lot like Windows 8.1, but I will see.
Feel free to check out the video. There is a basic assumption that you already either have or know how to setup Oracle VirtualBox (you can use Hyper-V instead if you wish - I tried it with Hyper-V and found the networking in 10 a bit wanting).
One of the first things that struck me about Windows 10, after reconciling to the fact that it wasn't a lot different than 8.1, was that you could easily set it up to login with a 4 digit pin number. In fact, this seems to be encouraged. The only reason I could think why Microsoft would want to do this is to be more like Apple. A 4 digit pin is in no way secure. Yes it is more secure than no password/phrase/pin, but that isn't saying much. I hope that Microsoft revamps the security settings before releasing this. It looks like everything is on by default, and I don't mean the good things. For instance, in Privacy Settings the default is all on.
![Privacy---General.jpg]()
And that is just the General Privacy options...
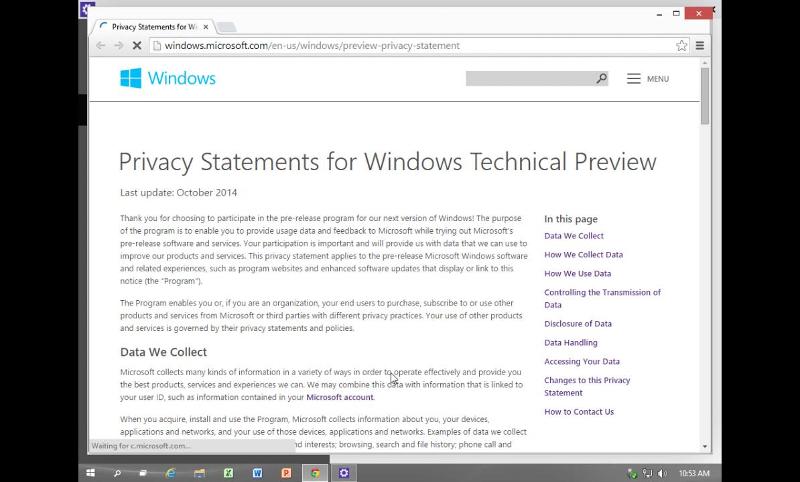
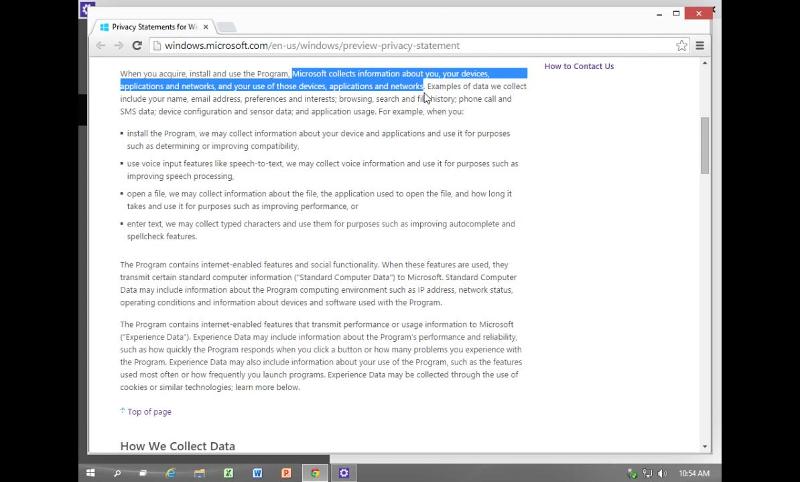
Read the Privacy Statement carefully. It says that Microsoft will collect all kinds of information from the user.
![Privacy---statement.jpg]()
![privacy---statement---collects-info.jpg]()
![privacy---statement---collects-info---2.]() and that is just the tip of the iceberg. So be aware of what is being shared.
and that is just the tip of the iceberg. So be aware of what is being shared.
Feel free to check out the video. There is a basic assumption that you already either have or know how to setup Oracle VirtualBox (you can use Hyper-V instead if you wish - I tried it with Hyper-V and found the networking in 10 a bit wanting).
One of the first things that struck me about Windows 10, after reconciling to the fact that it wasn't a lot different than 8.1, was that you could easily set it up to login with a 4 digit pin number. In fact, this seems to be encouraged. The only reason I could think why Microsoft would want to do this is to be more like Apple. A 4 digit pin is in no way secure. Yes it is more secure than no password/phrase/pin, but that isn't saying much. I hope that Microsoft revamps the security settings before releasing this. It looks like everything is on by default, and I don't mean the good things. For instance, in Privacy Settings the default is all on.
- applications can access
- your name
- picture
- account info
- Applications can use your advertising ID
- Microsoft watches your web content while the store is active
- Text suggestions (a nice feature) is on by default, but his also means that "somewhere" a file exists with your preferences
- Websites can access your language list
- Other personal information may be revealed
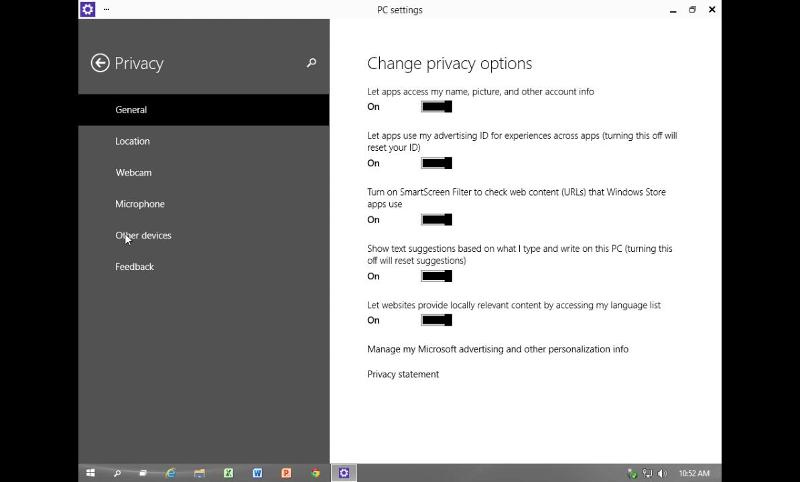
And that is just the General Privacy options...
Read the Privacy Statement carefully. It says that Microsoft will collect all kinds of information from the user.
Have a question about something in this article? You can receive help directly from the article author. Sign up for a free trial to get started.


Comments (5)
Commented:
So really they can collect away..
I had it installed for about 3 weeks before putting XP back on that machine.
I will run Windows Xp or Windows 7, but if i am forced to move to 10, i will go to Ubuntu..
Author
Commented:Commented:
My only problem with 8, 8.1 and now 10 is that MS is assuming I use my desktop like I use my phone or tablet, I don't. I use it like a powerful PC (i7-4690K) with two 24" monitors, 32GB of RAM and TBs of permanent storage and often have 6 or 8 windows (plural) opened at once. I don't want MS to assume I want to use their store - ever. When I explore (Firefox) the net, I don't want MS to pass along my private information. As a desktop platform Windows 10 is impressive - I wish I knew how to put their Notepad 10 on my Windows 7 PC. If wish my Win7 PCs could boot as quickly and turn off as quickly.
As far as using a virtual PC to load windows 10, consider instead a new hard drive. At less than $50, a 120 GB SSD is more than up to the task (Win 10 requires about 10 GB to load). There are disappointments (can't install ram disk, nor cloning software - well you can but it messes up both the source and target drives - lesson learned and a work around is available). But I assume Windows 10 will eventually get chiseled in stone and developers will have their turns to update their S/W to work in 10. Even then, 95% of what I do on a PC, cannot be done on a tablet or phone. So MS targeting a one-size-fits-all OS is my worst nightmare. Do they put their store on servers?
One last point, I'd like to get all the windows XP color schemes back. I don't want a desktop that looks like a wall flower. I don't like metro or aero. I want to use my hardware and I prefer my OS not use my CPU's cycles to paint pretty pictures. As a minimum, that should be my choice, not some graphics rock-star at MS. Despite the flaws that will surely remain, I will go to Windows 10 and learn and avoid everything I don't like about it because what remains is well worth while.
Commented:
I hate the Gui on.. Honestly Vista forward, but i can tolerate it on 7. The UAC is annoying, the colors as Ed pointed out.. also super annoying.. You can modify the start menu, but can't put back the things that everyone used on it.. the default should have remained with items or buttons that the windows 7 OS came with, as did XP, so that an IT person can walk you through things.. I hate the search, why do i want to search online? why can't i search local.. how do i launch CMD as an administrator? do i now have to navigate to the system32 location? or create a shortcut? It's a crap OS, built by a company who just can't pull it together.. If it fails, like i imagine it will, Ubuntu might be your only choice.. or Mac..
Author
Commented:Just an aside, I always check out new software and especially new OSes in virtual machines. It is just a safer way to go about the process.
What has been said about the interface, applies to everything after XP. Yes it would be easier to have the old defaults, but in truth they are not that hard to either put back or use slightly different ones. CMD in admin mode, for instance, is just [Win Logo] + X, then a (there are several other ways to do this, that's just the one I got used to).
All in all, Windows 10 is better because it is a combination of windows 8.1 and windows 7 (at least better than windows 8 or 8.1 alone). There are some definite pros to any windows above windows xp. One of these is the ease with which one can map network drives, this became even easier in windows 8 and that functionality was carried through (assuming that they don't change that when they finalize windows 10).