INTRODUCTION TO EU GDPR – GENERAL DATA PROTECTION REGULATION | Muneeb Imran Shaikh
-
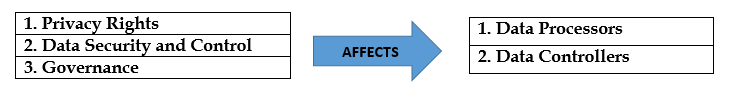
Key Areas of EU-GDPR Legislation
This requires:
1. Documented inventories of personal data.
2. Workflows.
3. Policies for updating or retiring data stores.
4. Processes to support the right to erasure.
Two Major Pain Points:
1. Requirement to notify EU authorities within 72 hours of a breach.
2. Proving your security approach is state of the art.
Geographical Scope of GDPR:
- Any company that does business with EU residents will be subject to GDPR, even if they operate outside the EU and do not have any premises or equipment in the EU.
Barriers to Compliance:
1. Inability to get projects off the ground due to lack of engagement from business stakeholders.
2. Maintaining Data Processing registry is mandatory under Article 30 (1) and such record must be available to relevant DPA upon request. This is applicable to Data controllers as well as Data processors.
3. If the above requirements are not met then an administrative fine of €10M or 2% of the annual worldwide turnover of the preceding year (whichever is higher) is imposed.
Policies for User Rights:
1. Data Retention Policy
2. How Individuals will be able to withdraw their consent.
3. How to deal with user requests when they object to the processing of personal data.
4. Server and device logging which can capture a substantial amount of personal data by itself will likely be a target for erasure requests.
NOTE: Removal/Erasure of data requested by PII Principals will be a big challenge given the fact that it will require to be removed from Enterprise archived data as well.
New User Rights to be Implemented:
1. Right to be informed.
2. Right of Access
3. Right to rectification.
4. Right to erasure.
5. Right to restrict processing.
6. Right to Data portability.
8. Rights related to automated decision making and profiling.
Have a question about something in this article? You can receive help directly from the article author. Sign up for a free trial to get started.



Comments (0)