Browse All Articles > Stop the Bleeding: First Aid for Malware!
The intent of this Article is to provide the basic First Aid steps for working through most malware infections. The target audience includes experienced IT professionals and the casual user who just wants to make the infection go away.
****************
For those familiar with basic “First Aid” principles, one of the first steps in a medical emergency is to “stop the bleeding”.
If you come upon an injured person, you don’t splint a broken leg first, right? You make sure air is flowing into the lungs, stop the bleeding, and then treat for shock.
After getting the basics out of the way you can then move on to address any other problems that exist.
*******************
Fighting Malware (http://en.wikipedia.org/wiki/Malware) must start with:
Most variants of malware will make your computer do something that you don’t want it doing. It might be a simple ‘re-direct’ problem; where you type in www.abc.com and your browser goes to www.xyz.com – not a big deal, right?
Well, maybe it is a very big deal. You didn’t end up at the web site you intended, and who knows what is waiting for you when to get to that re-directed site. It's not uncommon for malware to direct users to sites where they can pick up other "drive-by downloads" or even to install additional malware directly.
You might click on one of your favorite applications, but instead of “MS Word” opening up, totally different functions start happening.
Worse than annoying, some of these rogue processes/applications can be stealing information from your computer or allowing your computer to be used for improper/illegal acts.
Many of the current malware infections will prevent even the best scanner programs from running properly. Some can even recognize the executable name of these scanners when you try to install them on an infected computer - then prevent the installation or alter the results of the scan.
“The Rogue Stoppers”
Three known effective tools are:
1. RogueKiller - http://www.geekstogo.com/forum/files/file/413-roguekiller/
2. RKill - http://www.bleepingcomputer.com/download/anti-virus/rkill
3. TheKiller - http://maliprog.geekstogo.com/explorer.exe
At each of those links are additional instructions that you need to review carefully before using the tools. REMEMBER: it's best to access these via another computer, copy the file(s) to a CD (or - not preferred - a USB drive), and transport them for installation on the infected computer.
RogueKiller is discussed at the link given above and for more information about RKill, read the information here: http://www.bleepingcomputer.com/forums/topic308364.html
Of the three, I prefer RogueKiller because of the additional functions/fixes it provides after stopping the processes. "TheKiller" has had great reviews from some very high level anti-malware experts and has some automated functions that make cleaning up even easier.
**************
Once the rogue processes are stopped (DO NOT re-boot your computer), you can scan for malware with your favorite scanners.
My first scanner of choice is always Malwarebytes (MBAM) (http://www.malwarebytes.org/mbam.php)
The team of developers at Malwarebytes is among the most dedicated in the business and they update the scan (DAT) files several times a day.
When I download MBAM from the link above, I always use the Internet Explorer “Save As” function to rename the executable from “mbam-setup-xxxx.exe” to something like “mb.exe”. Some malware variants can recognize the actual executable file name and prevent it from installing or functioning correctly.
After you have installed Malwarebytes, be sure to update it from this tab:
![MBAM_Update]()
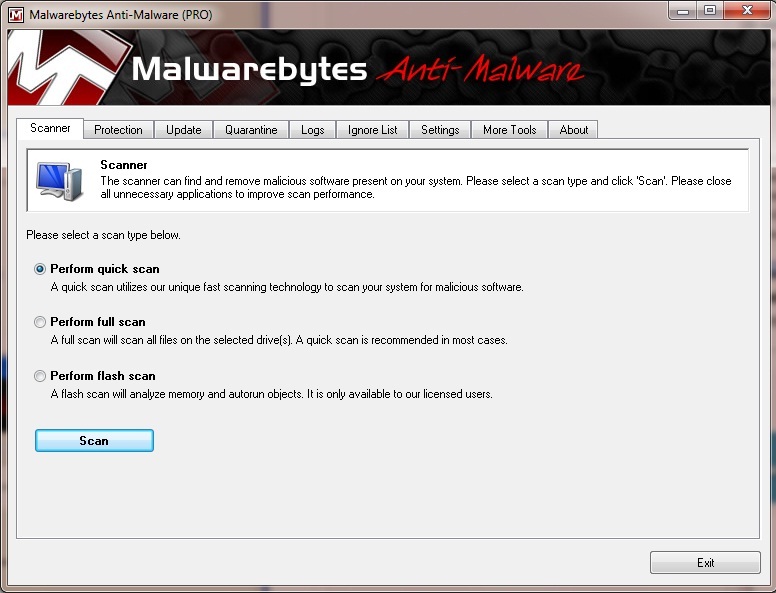
After updating, run a “Quick Scan” from this tab:
![MBAM-Console]()
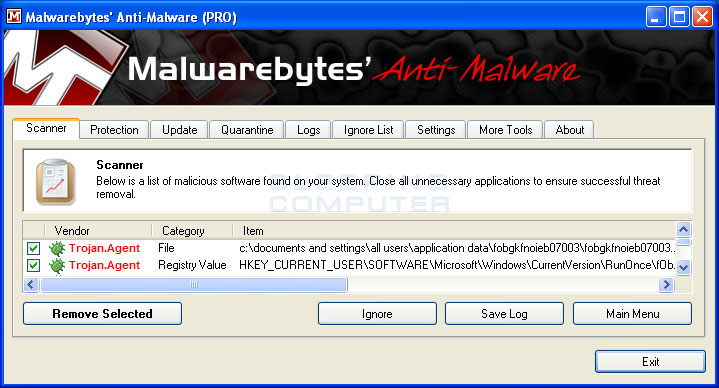
If MBAM finds any malware, it will display it as in the screen below. Simply click on the “Remove Selected” button and the infection will be removed.
![Sample]()
A Log will be generated and you should review the information carefully.
If you already have a question pending on Experts-Exchange, attach the log to a post in your question.
If you haven’t yet started a question, do it now and post the log as part of the process.
At this point I will usually shut down the system for a few minutes and then do a cold boot.
When you re-start your system, go ahead and do another “Complete Scan” with Malwarebytes. You will almost never find additional infections, but this scan will only take a few extra minutes and is well worth it.
Depending on your results, it may be necessary to run another tool such as ComboFix ("ComboFix" (http://www.bleepingcomputer.com/combofix/how-to-use-combofix), but don’t take any further actions until your MBAM log has been evaluated.
One of the cautions in fighting malware is to use the minimum number of tools possible. If you can (1) effectively stop the rogue processes and (2) successfully run Malwarebytes, you are well on your way to cleaning your system. Open a question in the Virus & Spyware Topic Areas and post the logs from the tools/scanners you have used and get some input from our experts.
In specific instances there may be tools targeted for a certain variant of malware that you have. In those cases, the Experts can provide you with additional instructions.
If you used a USB drive, be sure to scan it before using it again - remember that some malware can spread via USB drive.
Below are some general comments about frequently recommended tools in the Virus & Spyware Zones.
Educate yourself about the product – and also about the “Expert” who is recommending it. Feel free to ask the Expert "why" they are making the recommendation they've posted. After all, it is YOUR computer – and you need to be prudent about the actions you take.
Some other valid Articles here on Experts-Exchange that I highly recommend you read are:
Malware Fighting – Best Practices
2012-Malware-Variants
MALWARE - "An Ounce of Prevention..."
Basic Malware Troubleshooting
Rogue-Killer-What-a-great-name
Latest-Malware-Threat-Windows-Stability-Center
Desktop icons missing - Empty program files
Viruses in System Volume Information (System Restore)
THINGS YOU NEED TO DO WHEN YOUR PC IS INFECTED:
IF YOU CAN'T RUN .EXES IN AN INFECTED SYSTEM:
Can't Install an Antivirus - Windows Security Center still detects previous AV:
HijackThis - Some Tips & Tricks:
HijackThis reports missing files on 64-bit Systems:
"Google Hijack" - Google Search Gets Redirected:
MBAM-Scan.bmp
****************
For those familiar with basic “First Aid” principles, one of the first steps in a medical emergency is to “stop the bleeding”.
If you come upon an injured person, you don’t splint a broken leg first, right? You make sure air is flowing into the lungs, stop the bleeding, and then treat for shock.
After getting the basics out of the way you can then move on to address any other problems that exist.
*******************
Fighting Malware (http://en.wikipedia.org/wiki/Malware) must start with:
“Stop the Rogue Processes”
Most variants of malware will make your computer do something that you don’t want it doing. It might be a simple ‘re-direct’ problem; where you type in www.abc.com and your browser goes to www.xyz.com – not a big deal, right?
Well, maybe it is a very big deal. You didn’t end up at the web site you intended, and who knows what is waiting for you when to get to that re-directed site. It's not uncommon for malware to direct users to sites where they can pick up other "drive-by downloads" or even to install additional malware directly.
You might click on one of your favorite applications, but instead of “MS Word” opening up, totally different functions start happening.
Worse than annoying, some of these rogue processes/applications can be stealing information from your computer or allowing your computer to be used for improper/illegal acts.
Many of the current malware infections will prevent even the best scanner programs from running properly. Some can even recognize the executable name of these scanners when you try to install them on an infected computer - then prevent the installation or alter the results of the scan.
“The Rogue Stoppers”
Three known effective tools are:
1. RogueKiller - http://www.geekstogo.com/forum/files/file/413-roguekiller/
2. RKill - http://www.bleepingcomputer.com/download/anti-virus/rkill
3. TheKiller - http://maliprog.geekstogo.com/explorer.exe
At each of those links are additional instructions that you need to review carefully before using the tools. REMEMBER: it's best to access these via another computer, copy the file(s) to a CD (or - not preferred - a USB drive), and transport them for installation on the infected computer.
RogueKiller is discussed at the link given above and for more information about RKill, read the information here: http://www.bleepingcomputer.com/forums/topic308364.html
Of the three, I prefer RogueKiller because of the additional functions/fixes it provides after stopping the processes. "TheKiller" has had great reviews from some very high level anti-malware experts and has some automated functions that make cleaning up even easier.
**************
Continuing the treatment.
Once the rogue processes are stopped (DO NOT re-boot your computer), you can scan for malware with your favorite scanners.
My first scanner of choice is always Malwarebytes (MBAM) (http://www.malwarebytes.org/mbam.php)
The team of developers at Malwarebytes is among the most dedicated in the business and they update the scan (DAT) files several times a day.
When I download MBAM from the link above, I always use the Internet Explorer “Save As” function to rename the executable from “mbam-setup-xxxx.exe” to something like “mb.exe”. Some malware variants can recognize the actual executable file name and prevent it from installing or functioning correctly.
After you have installed Malwarebytes, be sure to update it from this tab:

After updating, run a “Quick Scan” from this tab:
If MBAM finds any malware, it will display it as in the screen below. Simply click on the “Remove Selected” button and the infection will be removed.
A Log will be generated and you should review the information carefully.
If you already have a question pending on Experts-Exchange, attach the log to a post in your question.
If you haven’t yet started a question, do it now and post the log as part of the process.
At this point I will usually shut down the system for a few minutes and then do a cold boot.
When you re-start your system, go ahead and do another “Complete Scan” with Malwarebytes. You will almost never find additional infections, but this scan will only take a few extra minutes and is well worth it.
Depending on your results, it may be necessary to run another tool such as ComboFix ("ComboFix" (http://www.bleepingcomputer.com/combofix/how-to-use-combofix), but don’t take any further actions until your MBAM log has been evaluated.
One of the cautions in fighting malware is to use the minimum number of tools possible. If you can (1) effectively stop the rogue processes and (2) successfully run Malwarebytes, you are well on your way to cleaning your system. Open a question in the Virus & Spyware Topic Areas and post the logs from the tools/scanners you have used and get some input from our experts.
In specific instances there may be tools targeted for a certain variant of malware that you have. In those cases, the Experts can provide you with additional instructions.
If you used a USB drive, be sure to scan it before using it again - remember that some malware can spread via USB drive.
Below are some general comments about frequently recommended tools in the Virus & Spyware Zones.
In the past I have used SpyBot (http://www.safer-networking.org/index2.html) and SuperAntiSpyware (http://www.superantispyware.com/), but they (IMO) don’t begin to compare with the effectiveness of MBAM.
You might also see recommendations for TDSSKiller (http://support.kaspersky.com/viruses/solutions?qid=208280684) or HitmanPro (http://www.surfright.nl/en/hitmanpro)
TDSSKiller is an effective tool for fighting “Rootkit” type infections, but I’ve tested HitmanPro and haven’t found to do anything beyond what MBAM has already done.
TDSSKiller is an effective tool for fighting “Rootkit” type infections, but I’ve tested HitmanPro and haven’t found to do anything beyond what MBAM has already done.
There is really no way to provide a comprehensive list of all the recommendations you might see, but you definitely need to be in “Caveat Emptor” mode. Before using any recommendation, go to the linked site and read about it. Read the FAQ’s and Forums, then evaluate how well the developers respond to their users. Some tools are very well known and have been used by millions of people all over the world, but most are not that well known.
Educate yourself about the product – and also about the “Expert” who is recommending it. Feel free to ask the Expert "why" they are making the recommendation they've posted. After all, it is YOUR computer – and you need to be prudent about the actions you take.
Some other valid Articles here on Experts-Exchange that I highly recommend you read are:
Malware Fighting – Best Practices
2012-Malware-Variants
MALWARE - "An Ounce of Prevention..."
Basic Malware Troubleshooting
Rogue-Killer-What-a-great-
Latest-Malware-Threat-Wind
Desktop icons missing - Empty program files
Viruses in System Volume Information (System Restore)
THINGS YOU NEED TO DO WHEN YOUR PC IS INFECTED:
IF YOU CAN'T RUN .EXES IN AN INFECTED SYSTEM:
Can't Install an Antivirus - Windows Security Center still detects previous AV:
HijackThis - Some Tips & Tricks:
HijackThis reports missing files on 64-bit Systems:
"Google Hijack" - Google Search Gets Redirected:
MBAM-Scan.bmp
Have a question about something in this article? You can receive help directly from the article author. Sign up for a free trial to get started.

Comments (18)
Commented:
Good comprehensive advice from BillDL.
Definitely my yes vote! Thank you.
Author
Commented:I heartily concur with your thoughts about BillDL - he posts some of the most thorough/well-researched advice on EE (or anywhere else).
Commented:
Commented:
("=" are the red cheeks)
(but the praise is deserved)
Commented:
View More