Bardlebee
asked on
Cisco 1811 VPN/IPSEC setup
So, I am trying to setup 5 remote sites that for the most part will always stay the same IP address. It is on IPsec mode and I really only need static routes. The problem is that I have been doing research for the past week trying to set this bad boy up and I can't seem to get it right. That is, it is a bit over my head as I only have a CCENT so my knowledge is slim on this subject, though I know in theory how it works.
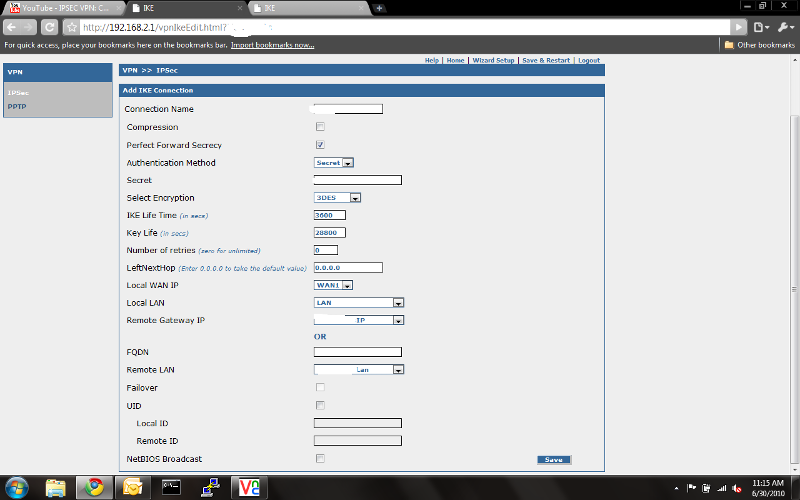
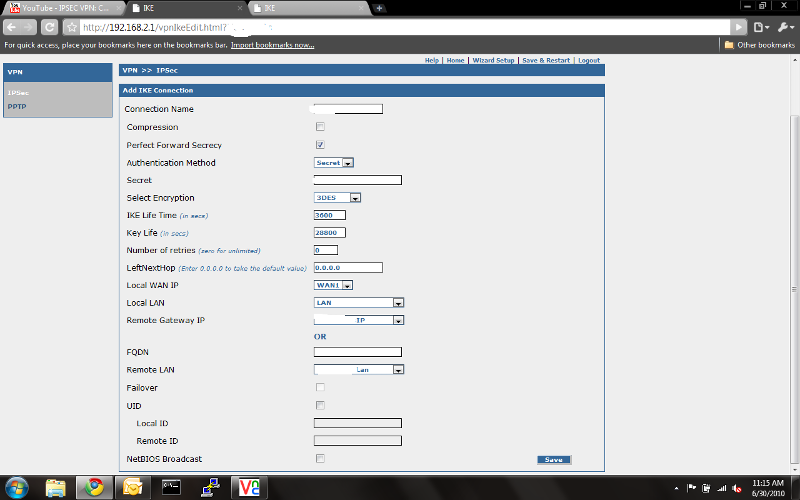
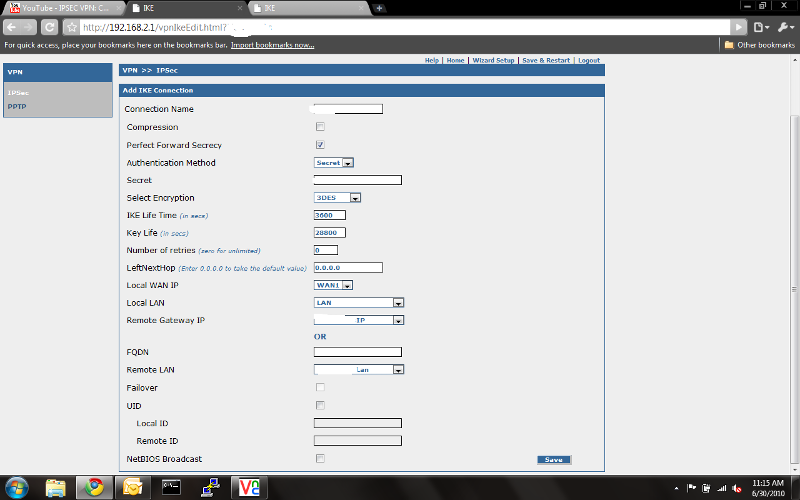
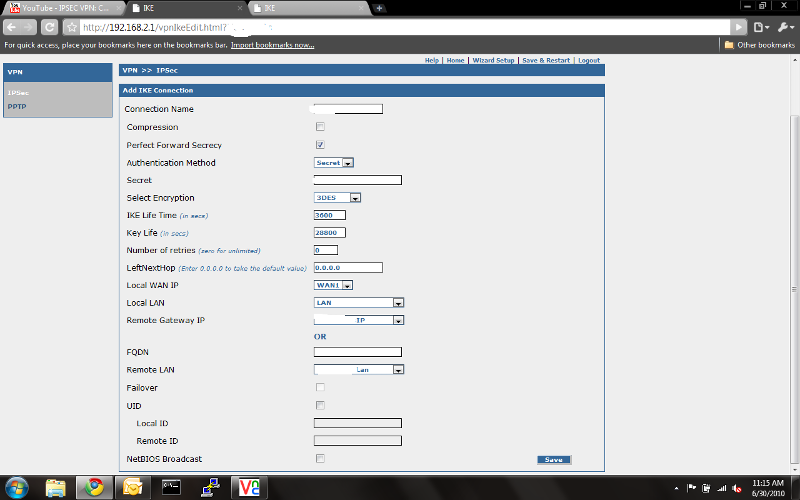
The first attachment is of my current RouteFinder that I am replacing with this Cisco 1811. The second image is of another RouteFinder which is my remote site. Each site is setup exactly the same so really I only need to be shown/advised once then I can nit pick through the rest.
Cisco Router 1811 - RouteFinder LAN: 192.168.2.0
Cisco Router 1811 - Outside IP Address: 111.111.111.1112 (this is fake obviously)
RouteFinder Remote Site LAN: 192.168.11.0
RouteFinder Remote Site Outside IP Address: 111.111.111.113 (fake as well)
You can see that I have NAT going as well, took me quite awhile to figure that one out...
Here is my sh run config:
Current configuration : 3746 bytes
!
version 12.4
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname WG-STSC
!
boot-start-marker
boot-end-marker
!
no logging buffered
!
no aaa new-model
!
crypto pki trustpoint TP-self-signed-3872896560
enrollment selfsigned
subject-name cn=IOS-Self-Signed-Certifi
revocation-check none
rsakeypair TP-self-signed-3872896560
!
!
crypto pki certificate chain TP-self-signed-3872896560
certificate self-signed 01
30820246 308201AF A0030201 02020101 300D0609 2A864886 F70D0101 04050030
31312F30 2D060355 04031326 494F532D 53656C66 2D536967 6E65642D 43657274
69666963 6174652D 33383732 38393635 3630301E 170D3130 30363235 31363337
35315A17 0D323030 31303130 30303030 305A3031 312F302D 06035504 03132649
4F532D53 656C662D 5369676E 65642D43 65727469 66696361 74652D33 38373238
39363536 3030819F 300D0609 2A864886 F70D0101 01050003 818D0030 81890281
8100BE8A B5790460 A9253C5A 38A1933A 19925684 71E3593E F352827B CA66CCC1
024EEC73 63C2FB7E DE069B52 F335D5EA A1A0839F A9E6104E EC45ABFA 8DA03006
BD0FE01F 35D15726 8D8E23E5 21BCD930 D220CE65 4528F3DC BA15C82F 4720549B
5EA44127 8DA7E630 EC359BC4 502C5E31 9DC8DA5E FF3D0393 DE10ED8D BC0013F5
2FD30203 010001A3 6E306C30 0F060355 1D130101 FF040530 030101FF 30190603
551D1104 12301082 0E57472D 53545343 2E574753 54534330 1F060355 1D230418
30168014 176C5BC2 2E35E8A6 02309904 DA180631 A77880D9 301D0603 551D0E04
16041417 6C5BC22E 35E8A602 309904DA 180631A7 7880D930 0D06092A 864886F7
0D010104 05000381 81008D31 D77BC5FC 24ECF53F D08E4371 5677043A 6A3F0D17
4E066A7B 8AB49E22 3B8F260F B8BB3723 2F10042A 66D44365 04F56FDB CD6DD582
7C1C0E80 E73093F2 00880ECB 11050139 A40B8767 F6D7EF2B BA3DDE2F 8DFA7D3C
58B8C04C 209A6D80 2C55F9B2 53BC4827 C92DEB9E E3865133 B6111C49 E98E486D
8C638C74 52170C4E AEBA
quit
dot11 syslog
!
!
ip cef
no ip dhcp use vrf connected
ip dhcp excluded-address 192.168.2.1
ip dhcp excluded-address 192.168.2.1 192.168.2.105
ip dhcp excluded-address 192.168.2.200 192.168.2.254
!
ip dhcp pool 192.168.2.0/24
network 192.168.2.0 255.255.255.0
default-router 192.168.2.1
dns-server 66.196.216.10
!
ip dhcp pool 192.168.2.0\24
dns-server 192.168.2.113 255.255.255.0
!
!
ip domain name WGSTSC
!
multilink bundle-name authenticated
!
!
username admin privilege 15 secret 5 $1$okPG$sSaKRYxgE8z7A/oZYT
!
!
archive
log config
hidekeys
!
!
!
!
!
interface FastEthernet0
ip address 111.111.111.112 255.255.255.240
ip nat outside
ip virtual-reassembly
duplex auto
speed auto
!
interface FastEthernet1
no ip address
duplex auto
speed auto
!
interface FastEthernet2
!
interface FastEthernet3
!
interface FastEthernet4
!
interface FastEthernet5
!
interface FastEthernet6
!
interface FastEthernet7
!
interface FastEthernet8
!
interface FastEthernet9
speed 100
!
interface Vlan1
ip address 192.168.2.1 255.255.255.0
ip nat inside
ip virtual-reassembly
!
interface Async1
no ip address
encapsulation slip
!
ip forward-protocol nd
ip route 0.0.0.0 0.0.0.0 111.111.111.111
!
!
ip http server
ip http authentication local
ip http secure-server
ip http timeout-policy idle 600 life 86400 requests 10000
ip nat inside source list 102 interface FastEthernet0 overload
!
access-list 1 remark SDM_ACL Category=2
access-list 1 permit 192.168.2.0 0.0.0.255
access-list 102 permit ip 192.168.2.0 0.0.0.255 any
!
!
!
!
!
!
control-plane
!
!
line con 0
line 1
modem InOut
stopbits 1
speed 115200
flowcontrol hardware
line aux 0
line vty 0 4
privilege level 15
login local
transport input telnet ssh
line vty 5 15
privilege level 15
login local
transport input ssh
line vty 16
privilege level 15
login local
transport input all
!
end
 Untitled2.png
Untitled2.png
The first attachment is of my current RouteFinder that I am replacing with this Cisco 1811. The second image is of another RouteFinder which is my remote site. Each site is setup exactly the same so really I only need to be shown/advised once then I can nit pick through the rest.
Cisco Router 1811 - RouteFinder LAN: 192.168.2.0
Cisco Router 1811 - Outside IP Address: 111.111.111.1112 (this is fake obviously)
RouteFinder Remote Site LAN: 192.168.11.0
RouteFinder Remote Site Outside IP Address: 111.111.111.113 (fake as well)
You can see that I have NAT going as well, took me quite awhile to figure that one out...
Here is my sh run config:
Current configuration : 3746 bytes
!
version 12.4
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname WG-STSC
!
boot-start-marker
boot-end-marker
!
no logging buffered
!
no aaa new-model
!
crypto pki trustpoint TP-self-signed-3872896560
enrollment selfsigned
subject-name cn=IOS-Self-Signed-Certifi
revocation-check none
rsakeypair TP-self-signed-3872896560
!
!
crypto pki certificate chain TP-self-signed-3872896560
certificate self-signed 01
30820246 308201AF A0030201 02020101 300D0609 2A864886 F70D0101 04050030
31312F30 2D060355 04031326 494F532D 53656C66 2D536967 6E65642D 43657274
69666963 6174652D 33383732 38393635 3630301E 170D3130 30363235 31363337
35315A17 0D323030 31303130 30303030 305A3031 312F302D 06035504 03132649
4F532D53 656C662D 5369676E 65642D43 65727469 66696361 74652D33 38373238
39363536 3030819F 300D0609 2A864886 F70D0101 01050003 818D0030 81890281
8100BE8A B5790460 A9253C5A 38A1933A 19925684 71E3593E F352827B CA66CCC1
024EEC73 63C2FB7E DE069B52 F335D5EA A1A0839F A9E6104E EC45ABFA 8DA03006
BD0FE01F 35D15726 8D8E23E5 21BCD930 D220CE65 4528F3DC BA15C82F 4720549B
5EA44127 8DA7E630 EC359BC4 502C5E31 9DC8DA5E FF3D0393 DE10ED8D BC0013F5
2FD30203 010001A3 6E306C30 0F060355 1D130101 FF040530 030101FF 30190603
551D1104 12301082 0E57472D 53545343 2E574753 54534330 1F060355 1D230418
30168014 176C5BC2 2E35E8A6 02309904 DA180631 A77880D9 301D0603 551D0E04
16041417 6C5BC22E 35E8A602 309904DA 180631A7 7880D930 0D06092A 864886F7
0D010104 05000381 81008D31 D77BC5FC 24ECF53F D08E4371 5677043A 6A3F0D17
4E066A7B 8AB49E22 3B8F260F B8BB3723 2F10042A 66D44365 04F56FDB CD6DD582
7C1C0E80 E73093F2 00880ECB 11050139 A40B8767 F6D7EF2B BA3DDE2F 8DFA7D3C
58B8C04C 209A6D80 2C55F9B2 53BC4827 C92DEB9E E3865133 B6111C49 E98E486D
8C638C74 52170C4E AEBA
quit
dot11 syslog
!
!
ip cef
no ip dhcp use vrf connected
ip dhcp excluded-address 192.168.2.1
ip dhcp excluded-address 192.168.2.1 192.168.2.105
ip dhcp excluded-address 192.168.2.200 192.168.2.254
!
ip dhcp pool 192.168.2.0/24
network 192.168.2.0 255.255.255.0
default-router 192.168.2.1
dns-server 66.196.216.10
!
ip dhcp pool 192.168.2.0\24
dns-server 192.168.2.113 255.255.255.0
!
!
ip domain name WGSTSC
!
multilink bundle-name authenticated
!
!
username admin privilege 15 secret 5 $1$okPG$sSaKRYxgE8z7A/oZYT
!
!
archive
log config
hidekeys
!
!
!
!
!
interface FastEthernet0
ip address 111.111.111.112 255.255.255.240
ip nat outside
ip virtual-reassembly
duplex auto
speed auto
!
interface FastEthernet1
no ip address
duplex auto
speed auto
!
interface FastEthernet2
!
interface FastEthernet3
!
interface FastEthernet4
!
interface FastEthernet5
!
interface FastEthernet6
!
interface FastEthernet7
!
interface FastEthernet8
!
interface FastEthernet9
speed 100
!
interface Vlan1
ip address 192.168.2.1 255.255.255.0
ip nat inside
ip virtual-reassembly
!
interface Async1
no ip address
encapsulation slip
!
ip forward-protocol nd
ip route 0.0.0.0 0.0.0.0 111.111.111.111
!
!
ip http server
ip http authentication local
ip http secure-server
ip http timeout-policy idle 600 life 86400 requests 10000
ip nat inside source list 102 interface FastEthernet0 overload
!
access-list 1 remark SDM_ACL Category=2
access-list 1 permit 192.168.2.0 0.0.0.255
access-list 102 permit ip 192.168.2.0 0.0.0.255 any
!
!
!
!
!
!
control-plane
!
!
line con 0
line 1
modem InOut
stopbits 1
speed 115200
flowcontrol hardware
line aux 0
line vty 0 4
privilege level 15
login local
transport input telnet ssh
line vty 5 15
privilege level 15
login local
transport input ssh
line vty 16
privilege level 15
login local
transport input all
!
end
 Untitled2.png
Untitled2.png
After going through the wizard in SDM, you'll have to go into CLI and add those two lifetime commands.
ASKER
Ok I will try this out and let you know, with the long weekend coming up this may not be until Tuesday. Thanks!
ASKER
Here is my sh run what do you think?
Building configuration...
*Jul 2 13:58:26.227: %SYS-5-CONFIG_I: Configured from console by console
Current configuration : 4184 bytes
!
version 12.4
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname WG-STSC
!
boot-start-marker
boot-end-marker
!
no logging buffered
!
no aaa new-model
!
crypto pki trustpoint TP-self-signed-3872896560
enrollment selfsigned
subject-name cn=IOS-Self-Signed-Certifi
revocation-check none
rsakeypair TP-self-signed-3872896560
!
!
crypto pki certificate chain TP-self-signed-3872896560
certificate self-signed 01
30820246 308201AF A0030201 02020101 300D0609 2A864886 F70D0101 04050030
31312F30 2D060355 04031326 494F532D 53656C66 2D536967 6E65642D 43657274
69666963 6174652D 33383732 38393635 3630301E 170D3130 30363235 31363337
35315A17 0D323030 31303130 30303030 305A3031 312F302D 06035504 03132649
4F532D53 656C662D 5369676E 65642D43 65727469 66696361 74652D33 38373238
39363536 3030819F 300D0609 2A864886 F70D0101 01050003 818D0030 81890281
8100BE8A B5790460 A9253C5A 38A1933A 19925684 71E3593E F352827B CA66CCC1
024EEC73 63C2FB7E DE069B52 F335D5EA A1A0839F A9E6104E EC45ABFA 8DA03006
BD0FE01F 35D15726 8D8E23E5 21BCD930 D220CE65 4528F3DC BA15C82F 4720549B
5EA44127 8DA7E630 EC359BC4 502C5E31 9DC8DA5E FF3D0393 DE10ED8D BC0013F5
2FD30203 010001A3 6E306C30 0F060355 1D130101 FF040530 030101FF 30190603
551D1104 12301082 0E57472D 53545343 2E574753 54534330 1F060355 1D230418
30168014 176C5BC2 2E35E8A6 02309904 DA180631 A77880D9 301D0603 551D0E04
16041417 6C5BC22E 35E8A602 309904DA 180631A7 7880D930 0D06092A 864886F7
0D010104 05000381 81008D31 D77BC5FC 24ECF53F D08E4371 5677043A 6A3F0D17
4E066A7B 8AB49E22 3B8F260F B8BB3723 2F10042A 66D44365 04F56FDB CD6DD582
7C1C0E80 E73093F2 00880ECB 11050139 A40B8767 F6D7EF2B BA3DDE2F 8DFA7D3C
58B8C04C 209A6D80 2C55F9B2 53BC4827 C92DEB9E E3865133 B6111C49 E98E486D
8C638C74 52170C4E AEBA
quit
dot11 syslog
!
!
ip cef
no ip dhcp use vrf connected
ip dhcp excluded-address 192.168.2.1
ip dhcp excluded-address 192.168.2.1 192.168.2.105
ip dhcp excluded-address 192.168.2.200 192.168.2.254
!
ip dhcp pool 192.168.2.0/24
network 192.168.2.0 255.255.255.0
default-router 192.168.2.1
dns-server 66.196.216.10
!
ip dhcp pool 192.168.2.0\24
dns-server 192.168.2.113 255.255.255.0
!
!
ip domain name WGSTSC
!
multilink bundle-name authenticated
!
!
username admin privilege 15 secret 5 $1$okPG$sSaKRYxgE8z7A/oZYT
!
!
crypto isakmp policy 1
encr 3des
authentication pre-share
group 5
crypto isakmp key css address 111.111.111.113
!
!
crypto ipsec transform-set esp-aes-sha esp-aes esp-sha-hmac
crypto ipsec transform-set esp-3des-sha1 esp-3des esp-sha-hmac
!
crypto map vpn 10 ipsec-isakmp
set peer 111.111.111.113
set transform-set esp-aes-sha
match address 101
!
archive
log config
hidekeys
!
!
!
!
!
interface FastEthernet0
ip address 111.111.111.112 255.255.255.240
ip nat outside
ip virtual-reassembly
duplex auto
speed auto
crypto map vpn
!
interface FastEthernet1
no ip address
duplex auto
speed auto
!
interface FastEthernet2
!
interface FastEthernet3
!
interface FastEthernet4
!
interface FastEthernet5
!
interface FastEthernet6
!
interface FastEthernet7
!
interface FastEthernet8
!
interface FastEthernet9
speed 100
!
interface Vlan1
ip address 192.168.2.1 255.255.255.0
ip nat inside
ip virtual-reassembly
!
interface Async1
no ip address
encapsulation slip
!
ip forward-protocol nd
ip route 0.0.0.0 0.0.0.0 111.111.111.111
!
!
ip http server
ip http authentication local
ip http secure-server
ip http timeout-policy idle 600 life 86400 requests 10000
ip nat inside source list 102 interface FastEthernet0 overload
!
access-list 1 remark SDM_ACL Category=2
access-list 1 permit 192.168.2.0 0.0.0.255
access-list 101 permit ip 192.168.2.0 0.0.0.255 192.168.11.0 0.0.0.255
access-list 102 permit ip 192.168.2.0 0.0.0.255 any
!
!
!
!
!
!
control-plane
!
!
line con 0
line 1
modem InOut
stopbits 1
speed 115200
flowcontrol hardware
line aux 0
line vty 0 4
privilege level 15
login local
transport input telnet ssh
line vty 5 15
privilege level 15
login local
transport input ssh
line vty 16
privilege level 15
login local
transport input all
!
end
Building configuration...
*Jul 2 13:58:26.227: %SYS-5-CONFIG_I: Configured from console by console
Current configuration : 4184 bytes
!
version 12.4
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname WG-STSC
!
boot-start-marker
boot-end-marker
!
no logging buffered
!
no aaa new-model
!
crypto pki trustpoint TP-self-signed-3872896560
enrollment selfsigned
subject-name cn=IOS-Self-Signed-Certifi
revocation-check none
rsakeypair TP-self-signed-3872896560
!
!
crypto pki certificate chain TP-self-signed-3872896560
certificate self-signed 01
30820246 308201AF A0030201 02020101 300D0609 2A864886 F70D0101 04050030
31312F30 2D060355 04031326 494F532D 53656C66 2D536967 6E65642D 43657274
69666963 6174652D 33383732 38393635 3630301E 170D3130 30363235 31363337
35315A17 0D323030 31303130 30303030 305A3031 312F302D 06035504 03132649
4F532D53 656C662D 5369676E 65642D43 65727469 66696361 74652D33 38373238
39363536 3030819F 300D0609 2A864886 F70D0101 01050003 818D0030 81890281
8100BE8A B5790460 A9253C5A 38A1933A 19925684 71E3593E F352827B CA66CCC1
024EEC73 63C2FB7E DE069B52 F335D5EA A1A0839F A9E6104E EC45ABFA 8DA03006
BD0FE01F 35D15726 8D8E23E5 21BCD930 D220CE65 4528F3DC BA15C82F 4720549B
5EA44127 8DA7E630 EC359BC4 502C5E31 9DC8DA5E FF3D0393 DE10ED8D BC0013F5
2FD30203 010001A3 6E306C30 0F060355 1D130101 FF040530 030101FF 30190603
551D1104 12301082 0E57472D 53545343 2E574753 54534330 1F060355 1D230418
30168014 176C5BC2 2E35E8A6 02309904 DA180631 A77880D9 301D0603 551D0E04
16041417 6C5BC22E 35E8A602 309904DA 180631A7 7880D930 0D06092A 864886F7
0D010104 05000381 81008D31 D77BC5FC 24ECF53F D08E4371 5677043A 6A3F0D17
4E066A7B 8AB49E22 3B8F260F B8BB3723 2F10042A 66D44365 04F56FDB CD6DD582
7C1C0E80 E73093F2 00880ECB 11050139 A40B8767 F6D7EF2B BA3DDE2F 8DFA7D3C
58B8C04C 209A6D80 2C55F9B2 53BC4827 C92DEB9E E3865133 B6111C49 E98E486D
8C638C74 52170C4E AEBA
quit
dot11 syslog
!
!
ip cef
no ip dhcp use vrf connected
ip dhcp excluded-address 192.168.2.1
ip dhcp excluded-address 192.168.2.1 192.168.2.105
ip dhcp excluded-address 192.168.2.200 192.168.2.254
!
ip dhcp pool 192.168.2.0/24
network 192.168.2.0 255.255.255.0
default-router 192.168.2.1
dns-server 66.196.216.10
!
ip dhcp pool 192.168.2.0\24
dns-server 192.168.2.113 255.255.255.0
!
!
ip domain name WGSTSC
!
multilink bundle-name authenticated
!
!
username admin privilege 15 secret 5 $1$okPG$sSaKRYxgE8z7A/oZYT
!
!
crypto isakmp policy 1
encr 3des
authentication pre-share
group 5
crypto isakmp key css address 111.111.111.113
!
!
crypto ipsec transform-set esp-aes-sha esp-aes esp-sha-hmac
crypto ipsec transform-set esp-3des-sha1 esp-3des esp-sha-hmac
!
crypto map vpn 10 ipsec-isakmp
set peer 111.111.111.113
set transform-set esp-aes-sha
match address 101
!
archive
log config
hidekeys
!
!
!
!
!
interface FastEthernet0
ip address 111.111.111.112 255.255.255.240
ip nat outside
ip virtual-reassembly
duplex auto
speed auto
crypto map vpn
!
interface FastEthernet1
no ip address
duplex auto
speed auto
!
interface FastEthernet2
!
interface FastEthernet3
!
interface FastEthernet4
!
interface FastEthernet5
!
interface FastEthernet6
!
interface FastEthernet7
!
interface FastEthernet8
!
interface FastEthernet9
speed 100
!
interface Vlan1
ip address 192.168.2.1 255.255.255.0
ip nat inside
ip virtual-reassembly
!
interface Async1
no ip address
encapsulation slip
!
ip forward-protocol nd
ip route 0.0.0.0 0.0.0.0 111.111.111.111
!
!
ip http server
ip http authentication local
ip http secure-server
ip http timeout-policy idle 600 life 86400 requests 10000
ip nat inside source list 102 interface FastEthernet0 overload
!
access-list 1 remark SDM_ACL Category=2
access-list 1 permit 192.168.2.0 0.0.0.255
access-list 101 permit ip 192.168.2.0 0.0.0.255 192.168.11.0 0.0.0.255
access-list 102 permit ip 192.168.2.0 0.0.0.255 any
!
!
!
!
!
!
control-plane
!
!
line con 0
line 1
modem InOut
stopbits 1
speed 115200
flowcontrol hardware
line aux 0
line vty 0 4
privilege level 15
login local
transport input telnet ssh
line vty 5 15
privilege level 15
login local
transport input ssh
line vty 16
privilege level 15
login local
transport input all
!
end
So far so good, it looks like you still need to fix your NAT, or else tunnel traffic will go out NAT'd. I believe in the SDM if you test the tunnel while it's down, it should notice the NAT issue and offer a link to fix it for you. If not, take a look at my example and you'll see how the NAT line now points to a route map, which in turn points to an extended ACL that says "deny NAT for any traffic from 192.168.2.x to 192.168.11.x, but allow NAT for anything else outbound".
Also don't forget to add lifetime 3600 inside crypto isakmp policy 1, and the global config line crypto ipsec security-association lifetime seconds 28800 to set your IPsec lifetime.
Also, I see you chose AES, make sure to match that on the other device as well, as it is currently set to 3DES.
Also don't forget to add lifetime 3600 inside crypto isakmp policy 1, and the global config line crypto ipsec security-association lifetime seconds 28800 to set your IPsec lifetime.
Also, I see you chose AES, make sure to match that on the other device as well, as it is currently set to 3DES.
ASKER
On this line:
crypto ipsec transform-set esp-aes-sha esp-aes esp-sha-hmac
Can I change it so that my transform set uses 3des by using this line?:
crypto ipsec transform-set esp-3des-sha1 esp-3des esp-sha-hmac
I did just that by putting in transform-set esp-3des-sha1
Would this match the router which is using 3des on the other side? Also, I am a bit confused on what you mean by fixing my NAT? I will have to look at the SDM...
crypto ipsec transform-set esp-aes-sha esp-aes esp-sha-hmac
Can I change it so that my transform set uses 3des by using this line?:
crypto ipsec transform-set esp-3des-sha1 esp-3des esp-sha-hmac
I did just that by putting in transform-set esp-3des-sha1
Would this match the router which is using 3des on the other side? Also, I am a bit confused on what you mean by fixing my NAT? I will have to look at the SDM...
Yes, in you:
crypto map vpn 10 ipsec-isakmp
set peer 111.111.111.113
set transform-set esp-aes-sha
match address 101
You can change the transform-set used by setting it to esp-3des-sha1
For the NAT, go to SDM -> Configure -> VPN -> Edit Site To Site VPN -> Test Tunnel. Once it runs through the tests, it should give you a list of configuration problems and suggested fixed. One of them should be about NAT and offer a blue hyperlink to fix it for you automatically.
crypto map vpn 10 ipsec-isakmp
set peer 111.111.111.113
set transform-set esp-aes-sha
match address 101
You can change the transform-set used by setting it to esp-3des-sha1
For the NAT, go to SDM -> Configure -> VPN -> Edit Site To Site VPN -> Test Tunnel. Once it runs through the tests, it should give you a list of configuration problems and suggested fixed. One of them should be about NAT and offer a blue hyperlink to fix it for you automatically.
ASKER
Now does the router have to be connected to the internet for the fix to happen? Right now I am just straight up connecting to it via COM port.
No, link status shouldn't have an effect on that. It will still evaluate the tunnel config.
ASKER
This is what I got when I hooked it up, happened every time I pinged or it may have happened every few minutes:
Jul 8 12:42:56.955: %CRYPTO-4-RECVD_PKT_INV_SP
Interesting.... what is the spi??
Jul 8 12:42:56.955: %CRYPTO-4-RECVD_PKT_INV_SP
Interesting.... what is the spi??
It means there is still something not quite right with the setup, here is a great article on SPI and troubleshooting it, etc:
http://www.cisco.com/en/US/docs/ios/12_3t/12_3t2/feature/guide/gt_ispir.html
http://www.cisco.com/en/US/docs/ios/12_3t/12_3t2/feature/guide/gt_ispir.html
ASKER
I did the configuration fix with the GUI now it looks like its up, so I tested it again and it is complaining about MTU size... am I supposed to specify the size as well?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
I can now ping my outside site, so I think I have it setup correctly, though when I went into fa0, I had to do the command:
ip mtu 1440
It said something about not supporting simple 'mtu 1440'
Before I go on to the error I have, someone said to disable DOM, I know it stands for Digital Optical Manager (I think?) but I don't know what would use it. My satellite sites are using basic retail VPN routers..
When I do the Cisco SDM test again, it states its up, I can ping, but it gives me the same error. Here is what it looks like:
Untitled.png
ip mtu 1440
It said something about not supporting simple 'mtu 1440'
Before I go on to the error I have, someone said to disable DOM, I know it stands for Digital Optical Manager (I think?) but I don't know what would use it. My satellite sites are using basic retail VPN routers..
When I do the Cisco SDM test again, it states its up, I can ping, but it gives me the same error. Here is what it looks like:
Untitled.png
ASKER
You can scratch that question I was asking about DOM. The guy wasn't referring to me in the forum I was in. :P
Next I would fire up the SDM and going through the VPN site-to-site wizard (don't do "quick setup") for your 1811, it makes configuring the tunnel quite easy and I've had good success with it. It will also fix your NAT ACL for you so that tunnel traffic is not NAT'd.
At the end of it all your (or if you want to jump right to CLI...) config is going to look like:
crypto isakmp policy 1
encr 3des
authentication pre-share
group 2
lifetime 3600
crypto isakmp key MYSHAREDKEY address 111.111.111.113
crypto ipsec security-association lifetime seconds 28800
crypto ipsec transform-set ESP-3DES-SHA1 esp-3des esp-sha-hmac
crypto map SDM_CMAP_1 1 ipsec-isakmp
description Tunnel to111.111.111.113
set peer 111.111.111.113
set transform-set ESP-3DES-SHA1
set pfs group2
match address 100
ip nat inside source route-map SM_RMAP_1 interface FastEthernet0 overload
access-list 100 remark SDM_ACL Category=4
access-list 100 remark IPSec Rule
access-list 100 permit ip 192.168.2.0 0.0.0.255 192.168.11.0 0.0.0.255
route-map SDM_RMAP_1 permit 1
match ip address nonat
ip access-list extended nonat
remark SDM_ACL Category=18
deny ip 192.168.2.0 0.0.0.255 192.168.11.0 0.0.0.255
permit ip 192.168.2.0 0.0.0.255 any
From a CLI perspective, here is a how-to on IPsec VPNs in Cisco routers:
http://www.routergeek.net/content/view/50/41/