failing PCI scan due to SSL2 issue
A third-party PCI compliance scanner let us know that we need to disable SSL2 on our mail server. I followed this MS KB, and did that (including a reboot):
http://support.microsoft.com/kb/187498
Requested a re-scan, but the results are the same:
serversniff.net reports:
Available SSL2 ciphers:
DES-CBC3-MD5 168 bit
RC4-MD5 128 bit
So I'm guessing I need to disable these ciphers as well. However, I'm not sure what registry entry corresponds with these 2 ciphers. These are the ciphers listed in the registry:
Windows 2008 Server/IIS 7
Thanks.
http://support.microsoft.com/kb/187498
Requested a re-scan, but the results are the same:
s_client -host x.x.x.x -port 443 -ssl2
Ciphers common between both SSL endpoints:
RC4-MD5 DES-CBC3-MD5
New, SSLv2, Cipher is DES-CBC3-MD5
Server public key is 1024 bit
Secure Renegotiation IS NOT supported
SSL-Session:
Protocol : SSLv2
serversniff.net reports:
Available SSL2 ciphers:
DES-CBC3-MD5 168 bit
RC4-MD5 128 bit
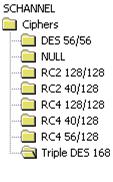
So I'm guessing I need to disable these ciphers as well. However, I'm not sure what registry entry corresponds with these 2 ciphers. These are the ciphers listed in the registry:
Windows 2008 Server/IIS 7
Thanks.
ASKER
Yes, as I said, I followed the first KB article, which specifies to change those dword values and restart.
My second question is indeed about the ciphers: "So I'm guessing I need to disable these ciphers as well. However, I'm not sure what registry entry corresponds with these 2 ciphers. These are the ciphers listed in the registry" (see pic that I posted).
My second question is indeed about the ciphers: "So I'm guessing I need to disable these ciphers as well. However, I'm not sure what registry entry corresponds with these 2 ciphers. These are the ciphers listed in the registry" (see pic that I posted).
Hi,
For PCI Compliance, your CIPHERS and SSL version need to be updated. Here is the registry setting I implement for all my clients.
1. Create SSL.reg with this code attached.
2. Execute entry into registry.
3. Reboot and run scan again.
Let me know if you have questions,
Hades666
For PCI Compliance, your CIPHERS and SSL version need to be updated. Here is the registry setting I implement for all my clients.
1. Create SSL.reg with this code attached.
2. Execute entry into registry.
3. Reboot and run scan again.
Let me know if you have questions,
Hades666
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols]
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\SSL 2.0]
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\SSL 2.0\Client]
"DisabledByDefault"=dword:00000001
"Enabled"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\SSL 2.0\Server]
"Enabled"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\SSL 3.0]
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\SSL 3.0\Client]
"Enabled"=dword:00000001
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\SSL 3.0\Server]
"Enabled"=dword:00000001
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.0]
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.0\Client]
"Enabled"=dword:00000001
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.0\Server]
"Enabled"=dword:00000001
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Ciphers]
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Ciphers\RC2 128/128]
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Ciphers\RC4 128/128]
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Ciphers\Triple DES]
And yes, for the other CIPHERS you have, Delete these keys.
DES 56/56, NULL, RC2 40/128, RC4 40/128, RC4 56/128
They are weak ciphers.
Cheers,
Hades666
DES 56/56, NULL, RC2 40/128, RC4 40/128, RC4 56/128
They are weak ciphers.
Cheers,
Hades666
ASKER
Thanks Hades666, I'll give it a shot.
ASKER
Ok, did that, but still seeing this from http://serversniff.net/sslcheck.php:
Preferred cipher:
TLSv1/SSLv3, Cipher is RC4-MD5 RC4(128)
Available SSL2 ciphers:
DES-CBC3-MD5 168 bit
RC4-MD5 128 bit
Attached file is what the registry looks like currently (2 files in one here - ciphers the protocols).
I don't have values set for the SSL2 client keys - does this matter? Seems I've seen KB articles that both mention this, and don't mention it.
ciphers-protocols.txt
Preferred cipher:
TLSv1/SSLv3, Cipher is RC4-MD5 RC4(128)
Available SSL2 ciphers:
DES-CBC3-MD5 168 bit
RC4-MD5 128 bit
Attached file is what the registry looks like currently (2 files in one here - ciphers the protocols).
I don't have values set for the SSL2 client keys - does this matter? Seems I've seen KB articles that both mention this, and don't mention it.
ciphers-protocols.txt
Hi,
Yes, you need to disable the client and server protocols.
You should also delete the following cipher keys completely. Don't disable them. Both my sites report only 128/168/256 Bit encryption and SSL3 only.
Here is how my register Channels and ciphers are configured.
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\SYSTEM
[HKEY_LOCAL_MACHINE\SYSTEM
[HKEY_LOCAL_MACHINE\SYSTEM
[HKEY_LOCAL_MACHINE\SYSTEM
[HKEY_LOCAL_MACHINE\SYSTEM
[HKEY_LOCAL_MACHINE\SYSTEM
"DisabledByDefault"=dword:
"Enabled"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM
"Enabled"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM
[HKEY_LOCAL_MACHINE\SYSTEM
"Enabled"=dword:00000001
[HKEY_LOCAL_MACHINE\SYSTEM
"Enabled"=dword:00000001
[HKEY_LOCAL_MACHINE\SYSTEM
[HKEY_LOCAL_MACHINE\SYSTEM
"Enabled"=dword:00000001
[HKEY_LOCAL_MACHINE\SYSTEM
"Enabled"=dword:00000001
cheers, Hades666
ASKER
Ok, thanks, this all looks good and I'll give it another shot. However, I'm wondering what the difference is between using 00000001 and ffffffff for the "Enabled" DWORD values?
In your example:
[HKEY_LOCAL_MACHINE\SYSTEM
"Enabled"=dword:00000001
In mine:
[HKEY_LOCAL_MACHINE\SYSTEM
"Enabled"=dword:ffffffff
I know you mentioned your sites are passing the PCI scans just fine, so all must be well :) but I'm curious, as that MS cipher KB mentions: "To allow this cipher algorithm, change the DWORD value data of the Enabled value to 0xffffffff, otherwise change the DWORD value data to 0x0. "
In your example:
[HKEY_LOCAL_MACHINE\SYSTEM
"Enabled"=dword:00000001
In mine:
[HKEY_LOCAL_MACHINE\SYSTEM
"Enabled"=dword:ffffffff
I know you mentioned your sites are passing the PCI scans just fine, so all must be well :) but I'm curious, as that MS cipher KB mentions: "To allow this cipher algorithm, change the DWORD value data of the Enabled value to 0xffffffff, otherwise change the DWORD value data to 0x0. "
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
Also, this is only one part of the PCI requirements regarding SSL. Another one is to disable all weak ciphers:
http://blog.zenone.org/2009/03/pci-compliance-disable-sslv2-and-weak.html