install ruby gem behind ISA
I am trying to install ruby gem behind ISA but I keep getting the following:
Error: Http://gems.rubyforge.org/ does not appear to be a repository
Error: could not find gem rails locally or in a repository
anybody knows how to fix this?
thanks
Error: Http://gems.rubyforge.org/ does not appear to be a repository
Error: could not find gem rails locally or in a repository
anybody knows how to fix this?
thanks
I think now it's http://rubygems.org
Also, on the Mac, you can just go to Terminal and try some of the commands ther:
Sorry; I don't know anything about MS Forefront; it might also be a configuration setting there.
gem list <== this lists the local gems
gem list -r <== this lists (a lot of) remote gems
gem install <gem-name>
Sorry; I don't know anything about MS Forefront; it might also be a configuration setting there.
gem list <== this lists the local gems
gem list -r <== this lists (a lot of) remote gems
gem install <gem-name>
ASKER
I can connect to ruby gems if I try from a computer not behind the firewall with the command below
Sudo gem install rais
But I can't connect when I try from a Mac behind the firewall
Sudo gem install rais
But I can't connect when I try from a Mac behind the firewall
This link:
http://stackoverflow.com/questions/4418/how-do-i-update-ruby-gems-from-behind-a-proxy-isa-ntlm
has a couple of answers about setting up a proxy to get through the firewall.
http://stackoverflow.com/questions/4418/how-do-i-update-ruby-gems-from-behind-a-proxy-isa-ntlm
has a couple of answers about setting up a proxy to get through the firewall.
ASKER
we have two ISAs 2000 and 2006. the updates can be installed from ISA 2000, but not from 2006. where is the setting in ISA2006 that need to change.
What system are you running? If you're on Linux or Mac, you would update your .bashrc file (that's the file that is run as part of your startup in Linux or when you start Terminal in Mac. This previous question and the answer might help you out in this case: https://www.experts-exchange.com/questions/26578638/How-Do-I-Add-a-PATH-environment-variable-to-the-bashrc-File.html?sfQueryTermInfo=1+10+30+bashrc+jesii
If you're on a Windows machine, you'd need to set your environment variables (Right-click on Computer, select Properties and there will be a button for "Environment Variables" where you can set the value as described in the previous link describing the proxy settings.
I've not done this myself so I can't guarantee this will work, but it seems to me to be a reasonable approach. Hope this helps.
If you're on a Windows machine, you'd need to set your environment variables (Right-click on Computer, select Properties and there will be a button for "Environment Variables" where you can set the value as described in the previous link describing the proxy settings.
I've not done this myself so I can't guarantee this will work, but it seems to me to be a reasonable approach. Hope this helps.
ASKER
I am using Mac. installed socks 5 and that doesn't work either
Firewalls are crazy/complex beasties, as I'm sure you know. If you don't have a security administrator to help you that's tough. Are you the one trying to configure the firewall?
In any event, it looks like you might have to set firewall policy rules... possibly in the "Non-web server protocol publishing rule" (see image - just above the selected item).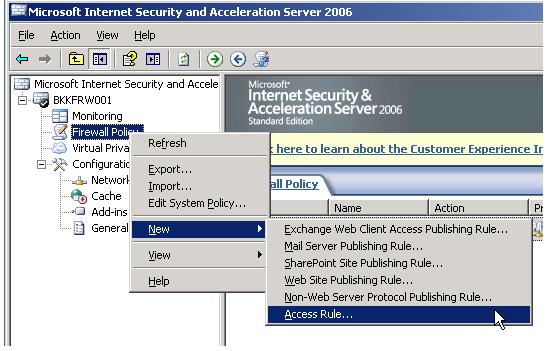 or possibly with the generic "Access Rule" wizard. See http://www.linglom.com/2008/01/07/getting-started-with-microsoft-isa-server-2006-part-iii-create-firewall-policy-rule/ for a little more about that.
or possibly with the generic "Access Rule" wizard. See http://www.linglom.com/2008/01/07/getting-started-with-microsoft-isa-server-2006-part-iii-create-firewall-policy-rule/ for a little more about that.
If that doesn't help, I'm tapped out... sorry.
In any event, it looks like you might have to set firewall policy rules... possibly in the "Non-web server protocol publishing rule" (see image - just above the selected item).
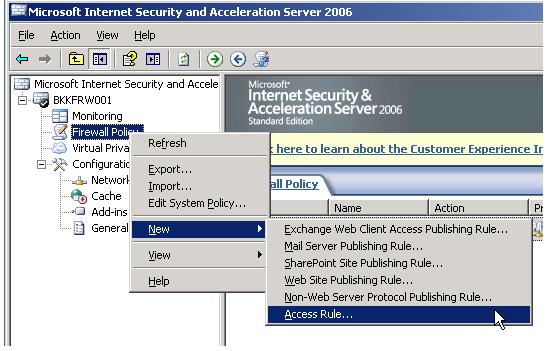 or possibly with the generic "Access Rule" wizard. See http://www.linglom.com/2008/01/07/getting-started-with-microsoft-isa-server-2006-part-iii-create-firewall-policy-rule/ for a little more about that.
or possibly with the generic "Access Rule" wizard. See http://www.linglom.com/2008/01/07/getting-started-with-microsoft-isa-server-2006-part-iii-create-firewall-policy-rule/ for a little more about that.If that doesn't help, I'm tapped out... sorry.
ASKER
I am getting the following on the ISA 2006
first line
destination: xx.xx.xx.xx
destination port:80
protocol: HTTP
Action: Initiated Connection
Rule: My Rule
Client IP: my IP
Client Username: blank
second Liine:
destination: xx.xx.xx.xx
destination port:80
protocol:blank
Action: Closed Connection
Rule: My Rule
Client IP: my IP
Client Username: Anonymous
third line
destination: xx.xx.xx.xx
destination port:80
protocol: HTTP
Action: Closed Connection
Rule: My Rule
Client IP: my IP
Client Username: blank
first line
destination: xx.xx.xx.xx
destination port:80
protocol: HTTP
Action: Initiated Connection
Rule: My Rule
Client IP: my IP
Client Username: blank
second Liine:
destination: xx.xx.xx.xx
destination port:80
protocol:blank
Action: Closed Connection
Rule: My Rule
Client IP: my IP
Client Username: Anonymous
third line
destination: xx.xx.xx.xx
destination port:80
protocol: HTTP
Action: Closed Connection
Rule: My Rule
Client IP: my IP
Client Username: blank
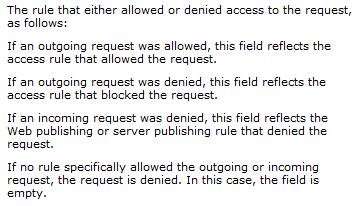
OK... have you checked out what the "My Rule" rule says? Here's a description of the "Rule" field, found at http://technet.microsoft.com/en-us/library/bb838824.aspx#WebProxyFilterLogFields. 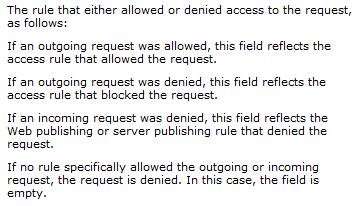
ASKER
My ISA firewall may have configuration problem. I need to reconfigure this
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
I did everything you told me to do, but still couldn't get rubygem to install behind the ISA. my only solution was to add another soniwall firewall and skip the proxy.
thanks for trying to help out
thanks for trying to help out
I'm really sorry that didn't work out, but glad that the at least were able to do what you wanted to do. Thank you for the opints.