Router Config Draytek 2820 - External IP address
Hi all, I've got a Draytek 2820 with an ADSL2+ line with a static IP Address.
All works fine and well.
However, what I'd like to do is
1. Get another external IP address, namely IP address A and IP address B
2. Configure one internal machine to have the external IP address A. Meaning that in the network settings of the windows 2008 server (which I intend to make it), it will be an external IP and not an internal IP and NAT-ed by the router.
3. The local LAN (not including the external faced machine mentioned in no.2) will be NAT-ed for internet access.
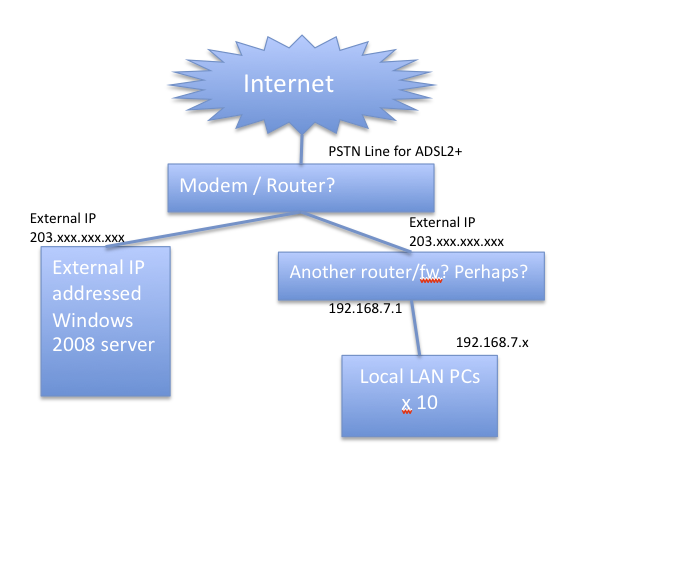
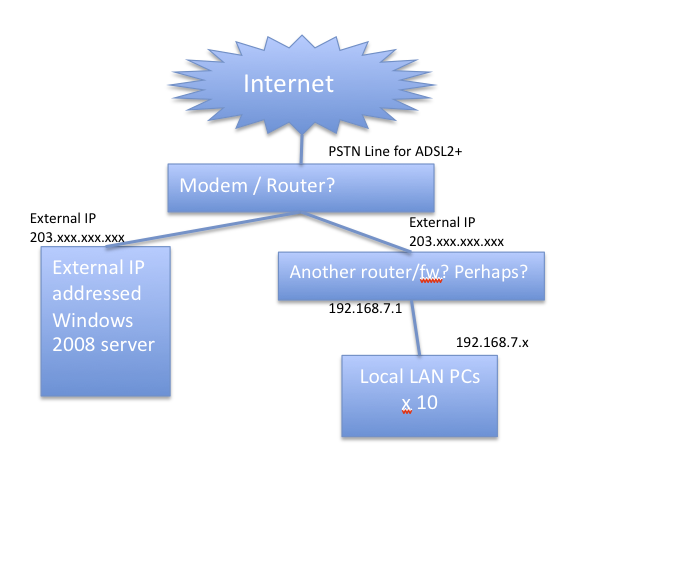
Can you advise if I'm on the right track as per the diagram I cooked up. As well as what Draytek model or what generic advice you can provide.
Thanks a million!
All works fine and well.
However, what I'd like to do is
1. Get another external IP address, namely IP address A and IP address B
2. Configure one internal machine to have the external IP address A. Meaning that in the network settings of the windows 2008 server (which I intend to make it), it will be an external IP and not an internal IP and NAT-ed by the router.
3. The local LAN (not including the external faced machine mentioned in no.2) will be NAT-ed for internet access.
Can you advise if I'm on the right track as per the diagram I cooked up. As well as what Draytek model or what generic advice you can provide.
Thanks a million!
Yes a good way would be to follow the above guide. I also agree with cocospm. You would be far better using port forward on the services you require to have public access on the 2008 server.
If its becuse you want to isolate the server totally you would be better having the draytek 3300V+ as this has true DMZ
http://www.draytek.co.uk/products/vigor3300vplus.html
If you wanted to do this you would need a simple adsl modem ( you could use your current router - set it up using the second lan range, just put in your public address) to sit in front of the 3300v.
SEtup the 2008 server in the dmz and your regualr clients behind the lan ports of the 3300v.
If its becuse you want to isolate the server totally you would be better having the draytek 3300V+ as this has true DMZ
http://www.draytek.co.uk/products/vigor3300vplus.html
If you wanted to do this you would need a simple adsl modem ( you could use your current router - set it up using the second lan range, just put in your public address) to sit in front of the 3300v.
SEtup the 2008 server in the dmz and your regualr clients behind the lan ports of the 3300v.
ASKER
Hi, we intend to install 3cx SIP server on the windows 2008 server. Even though it works behind a firewall with port forwarding etc, there is still an issue with remote hard phones (outside the current network). To avoid any problems with firewalls issues, compatibility and all, we've tested with an internet based server as a test. Now the challenge is to get the current infrastructure we've got (which is an internal server) to act as an internet facing server directly.
The multiNAT feature will not work in what I'm trying to achieve as it still is "PORT FORWARDING" to the designated server.
I understand from Draytek support that you can use the IP ROUTING Feature under the LAN settings. Not sure if this will work as I haven't tried it yet... I didn't think they understood my requirements though....
Any thoughts?
The multiNAT feature will not work in what I'm trying to achieve as it still is "PORT FORWARDING" to the designated server.
I understand from Draytek support that you can use the IP ROUTING Feature under the LAN settings. Not sure if this will work as I haven't tried it yet... I didn't think they understood my requirements though....
Any thoughts?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
But I have to ask - why you are trying to do this?? SBS 2008 has very good remote access facilities, and none of these require multiple public IP addresses. Also, the way you have illustrated your intended setup, you have the LAN workstations on a separate subnet from the SBS 2008 (which won't work), connected via a second router.