itmandan
asked on
server not available
We have a server sbs 2003
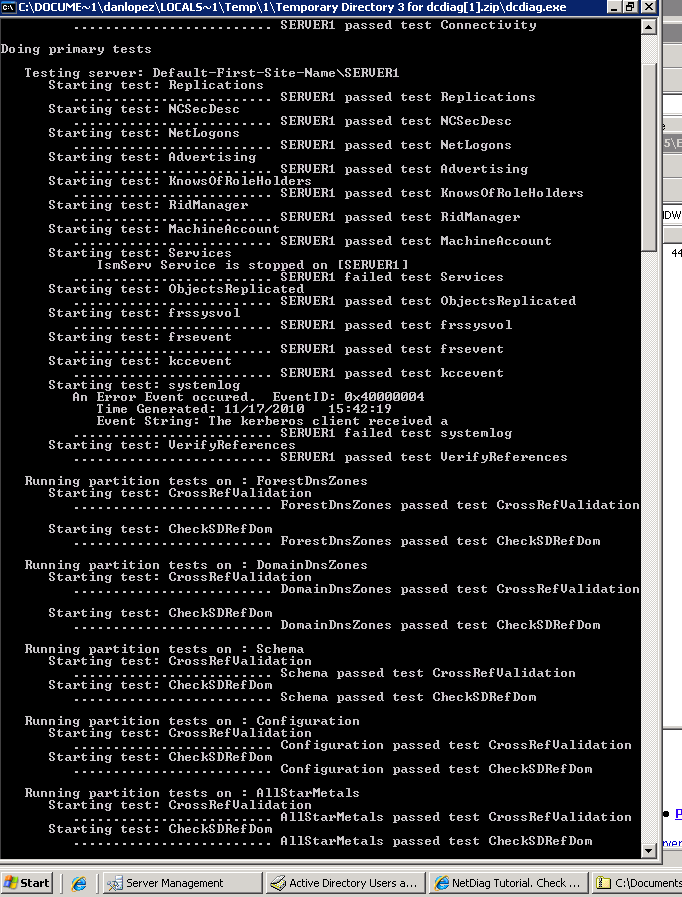
I am having a issue with logging onto the server it says server not available but it has to be because I am connected on my other computer and can remote and access the network files. I also can't add a computer on to the domain because it says the allstarmetals domain is not available. but I ran a dcdiag.exe on the server and everything passed except the IsmServ service I don't know if that is related but since I am fairly new to this any help would be appreciated.
ASKER
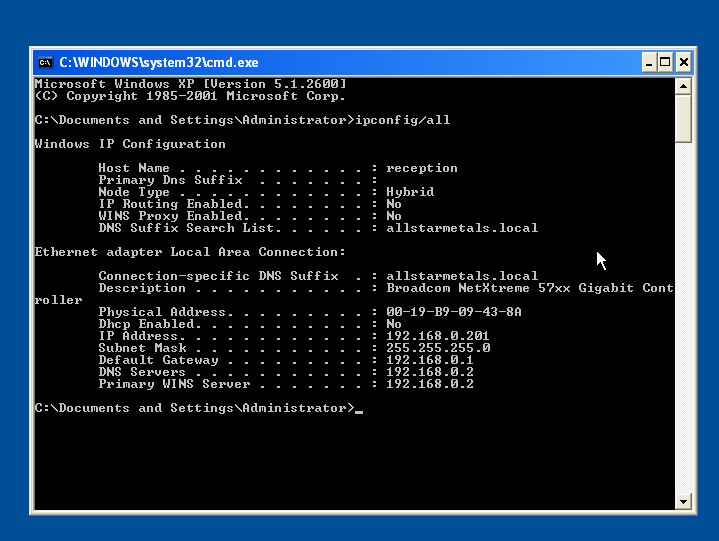
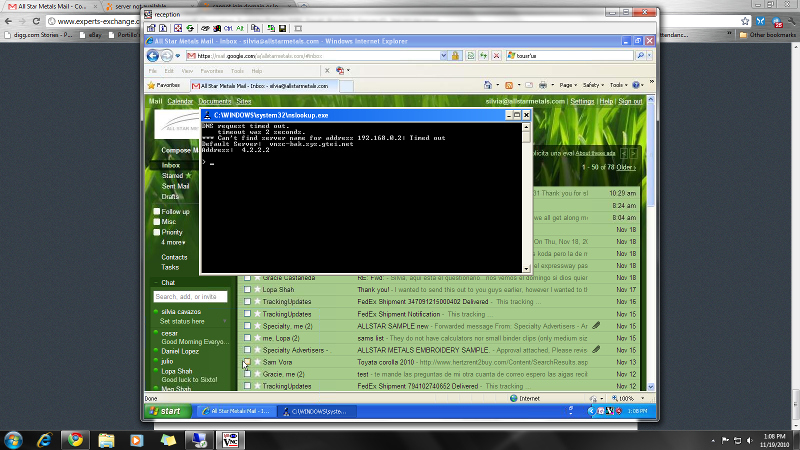
Pretty well guarantee your problem is the second image the workstation which points to 4.2.2.2 as an alternate. You cannot do that in a windows domain it will cause all sorts of name resolution problems. Server and workstation must point ONLY to the server for DNS. ISP is added with the wizard to the server's forwarders.
ASKER
To explain further. DNS does not work as you would expect. It makes a request from all listed servers. The first one to respond, which is often the ISP believe it or not, tries to resolve the name (usually that of the server), when it can't it times out and tries the second. With somethings this results in delays such as logons, but with others such as joining a domain it just fails altogether.
It is also best practice to use DHCP on the workstations and make sure the SBS is the DHCP server, not the router. This not an absolute must but definitely recommended for many reasons.
It is also best practice to use DHCP on the workstations and make sure the SBS is the DHCP server, not the router. This not an absolute must but definitely recommended for many reasons.
It cannot find it because of your DNS configuration, you must remove the 4.2.2.2 DNS server
ASKER
Forwarder is fine, but you cannot have 4.2.2.2 in the workstation TCP/IP configuration (or the server).
Many folk do this thinking if the SBS is off line they will still have Internet access, though it is true it will ruin internal DNS which is the backbone of a Windows domain.
Many folk do this thinking if the SBS is off line they will still have Internet access, though it is true it will ruin internal DNS which is the backbone of a Windows domain.
By the way after removing 4.2.2.2 you need to reboot or flush the DNS cache
ipconfig /flushdns
ipconfig /flushdns
ASKER
ASKER
even with the DNS 4.2.2.2 taken off and flushed it still gives me internet connection issues and I still cant access the domain.
If you remove 4.2.2.2 and you cannot connect to the Internet it means the server's forwarder is wrong. You should update 205.171.3.65 to be 4.2.2.2
I believe 205.171.3.65 is a Quest DNS server and 4.2.2.2 is Veizon and/or Comcast.
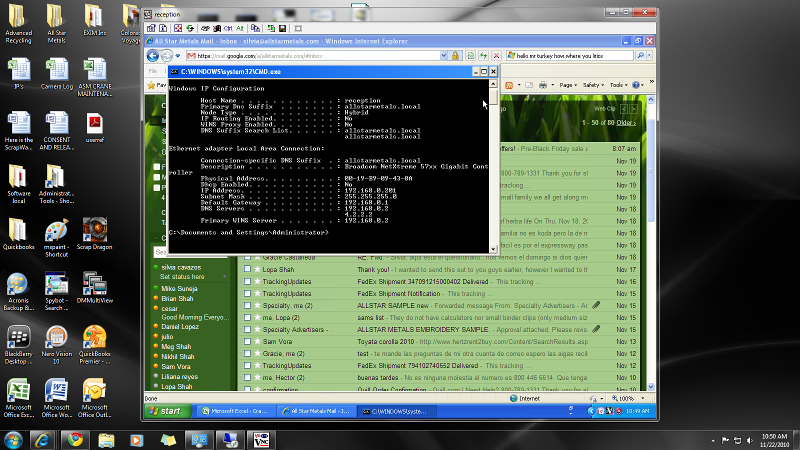
This output is from a different computer that you showed earlier. This one is also missing the DNS suffix which is probably why you cannot join the domain. This is why you should be using DHCP and the SBS as the DHCP server. SBS will assign and IP, gateway, subnet mask, correct DNS, WINS, domain suffix, and node type. It also assures proper DNS registration and avoids IP conflicts.
If you are going to use a static on the workstation add your domain suffix allstartmetals.local on the workstation under TCP/IP properties | advanced | DNS | use this DNS suffix for this connection
http://www.lan-2-wan.com/Added%20Images/Blog/DNS.jpg
I believe 205.171.3.65 is a Quest DNS server and 4.2.2.2 is Veizon and/or Comcast.
This output is from a different computer that you showed earlier. This one is also missing the DNS suffix which is probably why you cannot join the domain. This is why you should be using DHCP and the SBS as the DHCP server. SBS will assign and IP, gateway, subnet mask, correct DNS, WINS, domain suffix, and node type. It also assures proper DNS registration and avoids IP conflicts.
If you are going to use a static on the workstation add your domain suffix allstartmetals.local on the workstation under TCP/IP properties | advanced | DNS | use this DNS suffix for this connection
http://www.lan-2-wan.com/Added%20Images/Blog/DNS.jpg
ASKER
yes you are right, on our router it has the ip address as 205.171.3.65 I used 4.2.2.2 from Verizon because someone said it was a open DNS server. we have a T1 connection and I believe the 205.171.3.65 was what we got from them as the dns server.
ASKER
Once you remove 4.2.2.2 from the workstation, it will always contact the SBS for name resolution, even www.google.com The SBS of course cannot resolve that so it uses a forwarded to resolve, which must be active, accessible, and correct. I suspect 205.171.3.65 may not be working. Regardless you can re-run the CEICW (server management | internet and e-mail | connect to the internet) wizard, and change to 4.2.2.2 even as a test and see if it works OK.
I assume that a client machine can ping the server OK? Verifying there is a physical (TCP/IP) connection.
ping 192.168.0.2
Once you have removed the 4.2.2.2 and added the domain suffix can you ping the server by name?
ping server1
I assume that a client machine can ping the server OK? Verifying there is a physical (TCP/IP) connection.
ping 192.168.0.2
Once you have removed the 4.2.2.2 and added the domain suffix can you ping the server by name?
ping server1
That means you have existing connections to the server using different credentials. That is not allowed. Most often this is from mapped drives.
You can try from a command line using
net use /persistent:no
net use * /delete
and reboot.
You can try from a command line using
net use /persistent:no
net use * /delete
and reboot.
ASKER
i have run the connect to the internet wizard and used 4.2.2.2 it says on the DNS its forwarders is 4.2.2.2 and on the workstation I took out the 4.2.2.2 dns record and flushed the dns and it wont connect to the internet.
ASKER
are talking about doing the:
net use /persistent:no
net use * /delete
and reboot.
on the workstation or server?
net use /persistent:no
net use * /delete
and reboot.
on the workstation or server?
Can the server itself connect to the Internet?
Can you ping the server by IP and name from the workstation?
Can you ping the server by IP and name from the workstation?
>>"on the workstation or server? "
Workstation, the one with the error message relating to connections.
Workstation, the one with the error message relating to connections.
ASKER
I can ping the server by name "server1" and i can ping it by ip address "192.168.0.2"
I also ran the commands for killing the existing connections
also, one important thing "thanks" you are a big help Rob and I really apreciate this, at the very least I am gaining some much needed on hands experience.
I also ran the commands for killing the existing connections
also, one important thing "thanks" you are a big help Rob and I really apreciate this, at the very least I am gaining some much needed on hands experience.
ASKER
oh and yes i have internet access on the server, even with the dns changed to 4.2.2.2
You are very welcome. Glad to try to help.
Server sounds good.
If you can ping the server by name and have run the drive un-mapping commands, and reboot the workstation, try again to join the domain. We can then deal with Internet.
Server sounds good.
If you can ping the server by name and have run the drive un-mapping commands, and reboot the workstation, try again to join the domain. We can then deal with Internet.
ASKER
now it says the specified server cannot perform the operation.
Interesting.
-Is the time on the workstation within 2 minutes of the server? (actually has to be within 5 minutes, but 2 is certain).
-In the Workstation's TCP/IP configuration add the WINS server as your SBS IP (192.168.0.2) -likely won't help
-What O/S is the connecting PC? looks like XP which is fine, unless 64bit. Vista and Win7 are OK but there are some considerations.
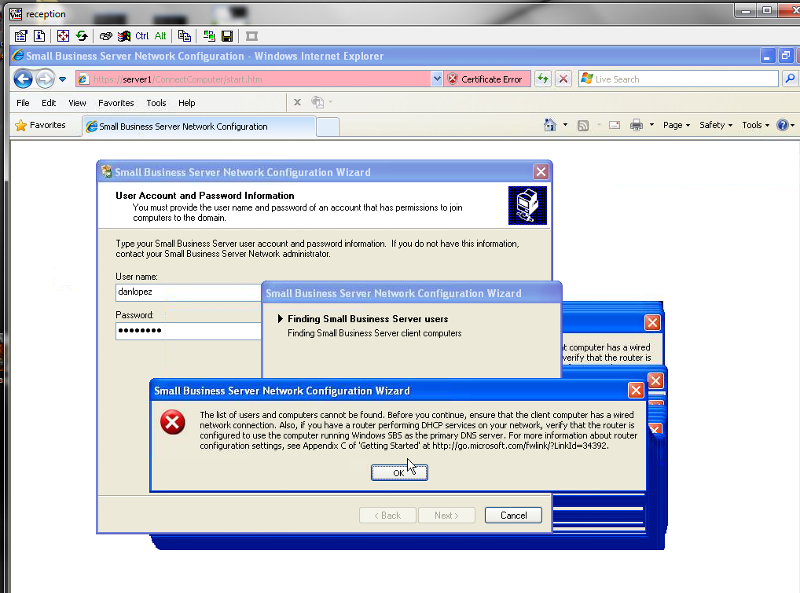
-This is SBS we should be doing this the correct way. The method you are using should work, but it is actually wrong for an SBS domain and doesn't allow for auto-configuration of many SBS features. The proper way is on the server to open the Server Management console and click on computers and in the left menu choose add client computers. Create a computer account for your connecting PC. it can be the same name it has now or a new one. If the user account does not already exist do the same under users. The wizards will allow you to assign a specific user to the PC if you like. This gives them admin rights to that particular machine. Then from the workstation you want to connect to the domain open a web browser and go to http://server1/connectcomputer It should start a wizard allowing you to properly join an SBS domain.
-Is the time on the workstation within 2 minutes of the server? (actually has to be within 5 minutes, but 2 is certain).
-In the Workstation's TCP/IP configuration add the WINS server as your SBS IP (192.168.0.2) -likely won't help
-What O/S is the connecting PC? looks like XP which is fine, unless 64bit. Vista and Win7 are OK but there are some considerations.
-This is SBS we should be doing this the correct way. The method you are using should work, but it is actually wrong for an SBS domain and doesn't allow for auto-configuration of many SBS features. The proper way is on the server to open the Server Management console and click on computers and in the left menu choose add client computers. Create a computer account for your connecting PC. it can be the same name it has now or a new one. If the user account does not already exist do the same under users. The wizards will allow you to assign a specific user to the PC if you like. This gives them admin rights to that particular machine. Then from the workstation you want to connect to the domain open a web browser and go to http://server1/connectcomputer It should start a wizard allowing you to properly join an SBS domain.
ASKER
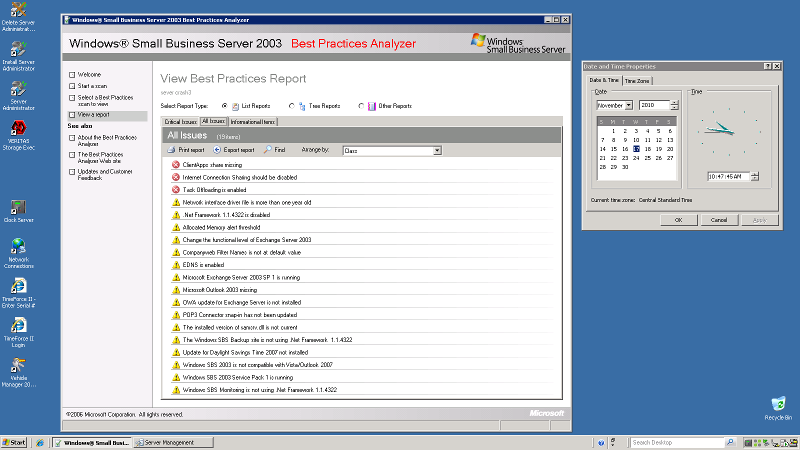
Internet and connection sharing can definitely cause problems though I am surprised pinging by name works. I would disable that. An the daylight savings time patch has not been installed. I am not sure if that would affect the time issue. The others I do not see affecting joining the domain.
Just to confirm "Admin" is an existing domain administrator account in active directory and not a local admin account on the workstation?
Just to confirm "Admin" is an existing domain administrator account in active directory and not a local admin account on the workstation?
ASKER
admin is a domain admin account i created and is in the active directory.
how would I go about disabling internet and connection sharing?
how would I go about disabling internet and connection sharing?
Might you have ever changed the name of the server or the domain after the initial server install?
ASKER
no i never have but I inherited the server, also another thing I was experiencing some problems when I used disk cleanup, it compressed some files that some have said is detrimental to the sbs OS so i uncompressed all files in all directories, don't know if that might shed some light on your end.
I don't see disk cleanup as causing this problem, assuming you compressed the folders they suggested and you didn't manually add system folders.
If you go to the server and open the following text file C:\Inetpub\ConnectComputer
It should show: domain="allstartmetals.loc
Is that correct?
I have a service call to make. I will check back but can only do so every now and then over the next 2-3 hours.
If you go to the server and open the following text file C:\Inetpub\ConnectComputer
It should show: domain="allstartmetals.loc
Is that correct?
I have a service call to make. I will check back but can only do so every now and then over the next 2-3 hours.
ASKER
cool, okay thanks rob and i will wait for your post and yes it does say domain="allstartmetals.loc
>>"disabling internet and connection sharing?"
If you disable RRAS that will do it, but if you have a VPN set up it will break it. You can also disable the service in the services management console.
Normally it is done on the network adpter but that can only be enabled there if you have more than 1 NIC on the server. Might there be more than 1?
If you disable RRAS that will do it, but if you have a VPN set up it will break it. You can also disable the service in the services management console.
Normally it is done on the network adpter but that can only be enabled there if you have more than 1 NIC on the server. Might there be more than 1?
ASKER
nope, I only got one NIC, so i guess going through the service tab is the best course of action. will that affect any remote desktop service I have?
No.
At least if you disable in service managemet it is easy to re-enable. I am surprised it is enabled with a single NIC.
At least if you disable in service managemet it is easy to re-enable. I am surprised it is enabled with a single NIC.
ASKER
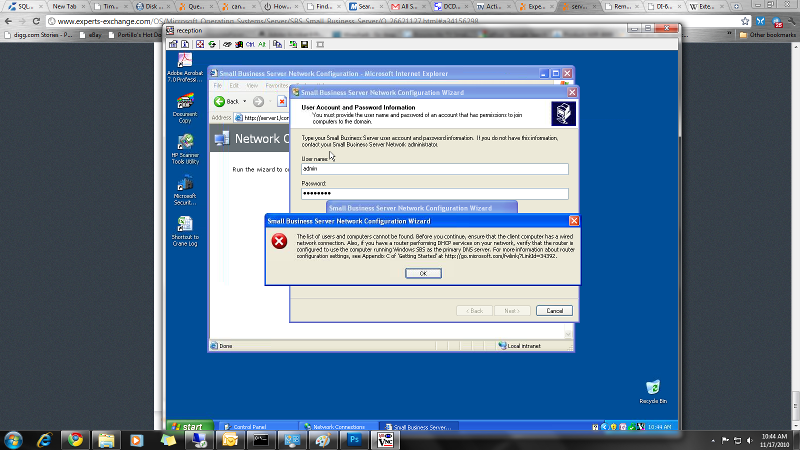
I was wondering if this is a issue
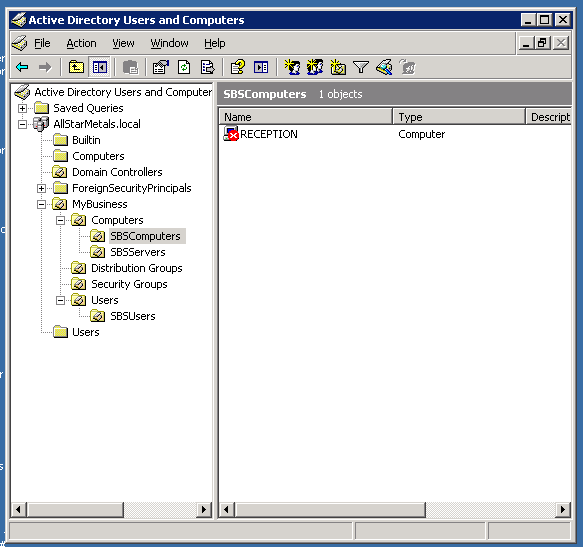 and on this image its not there
and on this image its not there
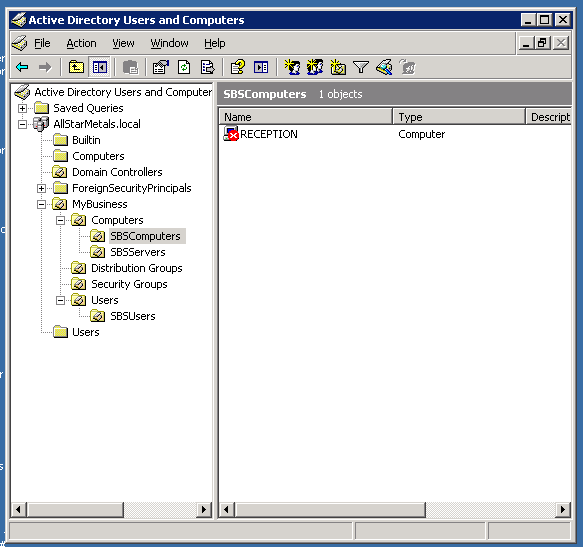 but when i try to add a computer to the allstarmetals.local computers ou I get this
but when i try to add a computer to the allstarmetals.local computers ou I get this
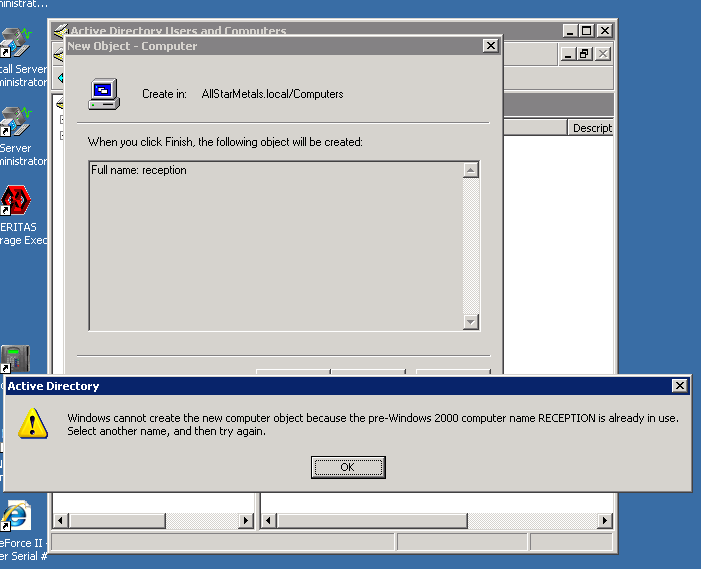 Untitled12.png
Untitled12.png
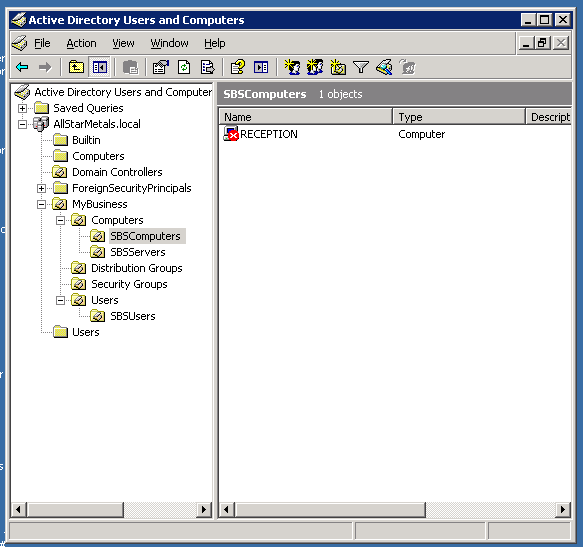 and on this image its not there
and on this image its not there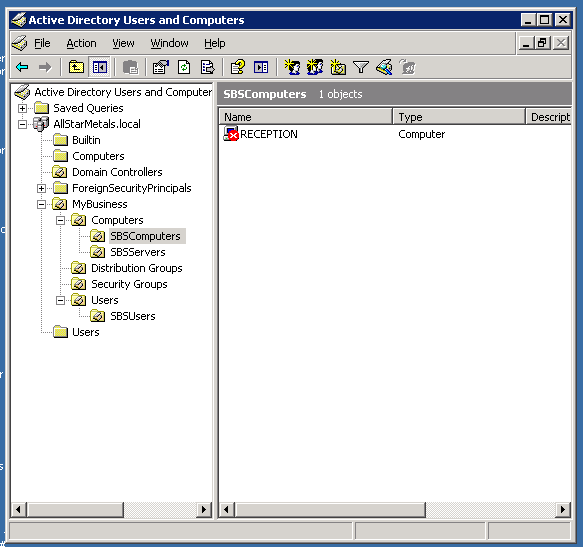 but when i try to add a computer to the allstarmetals.local computers ou I get this
but when i try to add a computer to the allstarmetals.local computers ou I get this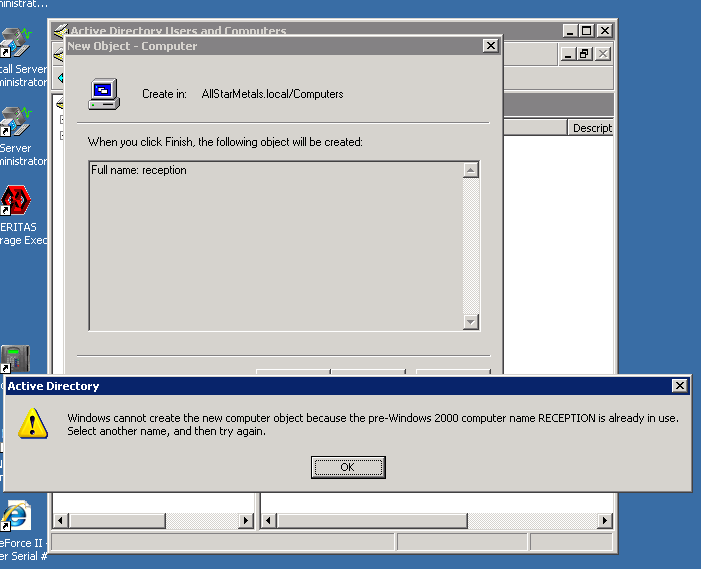 Untitled12.png
Untitled12.png
If you have already created the reception computer account on the server with the add computer wizard, and it has not yet joined the domain, I belive it will show with a red x.
Regardless when joining the domain you are not getting far enough to select a computer name from the http://sbsname/connectcomputer wizard fior that to be a problem
Regardless when joining the domain you are not getting far enough to select a computer name from the http://sbsname/connectcomputer wizard fior that to be a problem
I appreciate we have done all of this but based on the link below could you reboot the workstation and supply an updated ipconfig /all please.
http://support.microsoft.com/kb/837369
http://support.microsoft.com/kb/837369
ASKER
The only difference is allstarmetals.local is not shown as primary dns suffix.
Have you tried the manual (not connectcomputer) method of joining the domain and using allstarmetals.local as the domain name rather than just the short/NetBIOS name allstarmetals ?
Have you tried the manual (not connectcomputer) method of joining the domain and using allstarmetals.local as the domain name rather than just the short/NetBIOS name allstarmetals ?
ASKER
I tried it earlier but let me redo it again and see the result.
ASKER
nope, i tried allstarmetals.local and no dice, i tried allstarmetals and it ask for my credentials so that tell me its netbios is working. I have no clue why the credentials dont work, I am getting connection errors on most of our computers stating that it cant reach allstarmetals.
Is there a firewall enabled on the server. The windows should auto-configure but any other may not. I find some of the "security suites" are notorious for blocking server access.
ASKER
there are no security suites and windows firewall is on with exceptions.
ASKER
someone mention to use this
Make sure the DC advertising itself as domain controller,
Run below tests to verfiy the DC and post result.
dcdiag /q
netdiag /q
Netdom query dc - it will show all DCs in network.
netdom query fsmo - check FSMO roles are ok from the DC
but i cant run them
Make sure the DC advertising itself as domain controller,
Run below tests to verfiy the DC and post result.
dcdiag /q
netdiag /q
Netdom query dc - it will show all DCs in network.
netdom query fsmo - check FSMO roles are ok from the DC
but i cant run them
On the SBS just run DCDiag
You need to download it with the resource tool set or from:
http://www.computerperformance.co.uk/w2k3/utilities/windows_dcdiag.htm
You could also try running netdiag on the connecting workstation.
If there are errors in either please post the results here.
You need to download it with the resource tool set or from:
http://www.computerperformance.co.uk/w2k3/utilities/windows_dcdiag.htm
You could also try running netdiag on the connecting workstation.
If there are errors in either please post the results here.
ASKER
ASKER
it runs them both on the server so quickly i can't get a snapshot.
dcdiag.exe
netdiag.exe
dcdiag.exe
netdiag.exe
You need to run from a command lien (DOS window)
ASKER
ASKER
hey Rob, its quiting time for me but if you got time tomorrow to help I would greatly appreciate it.
oh and if you want here is my email dan@allstarmetals.com
once again thanks for everything and hope to hear from you tomorrow. Oh and if your ever in south texas ill buy you a beer.
oh and if you want here is my email dan@allstarmetals.com
once again thanks for everything and hope to hear from you tomorrow. Oh and if your ever in south texas ill buy you a beer.
That doesn't really tell us anything. "IsmServ is stopped" is normal on an SBS and "failed test systemlog" means there are errors in the system log. It might be worth looking in the Event Viewer under system log to see if there is anything relevant.
What does running netdiag on the workstation show.
Sorry to drag this out so long. It is very odd.
What does running netdiag on the workstation show.
Sorry to drag this out so long. It is very odd.
ASKER
hi Rob
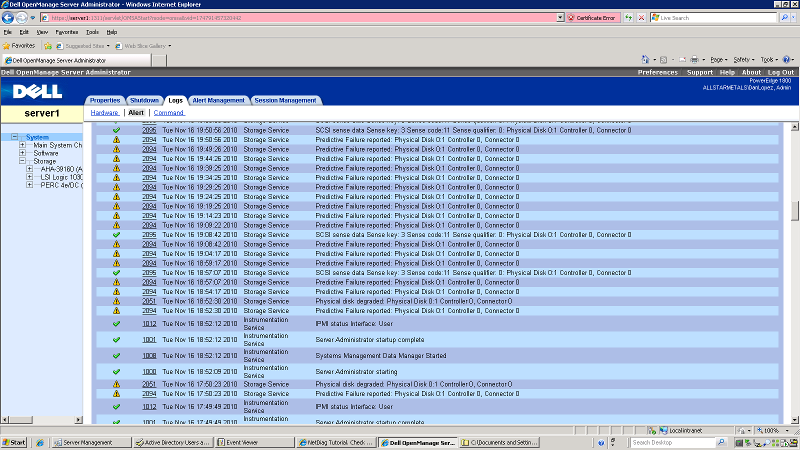
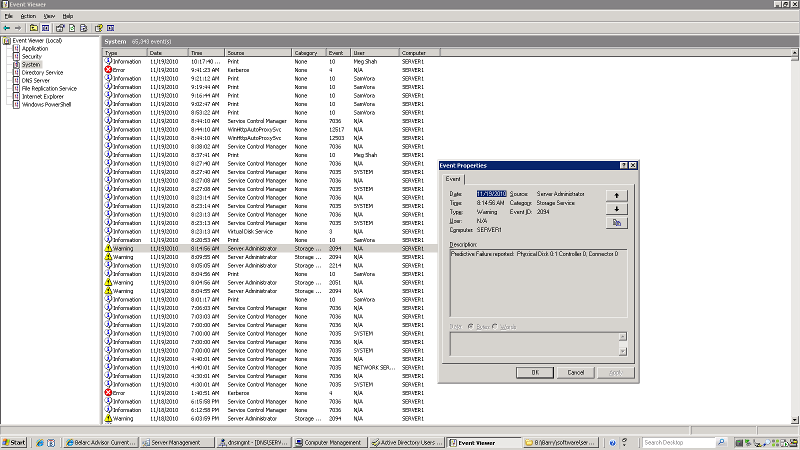
about the time I ran a diskclean up and compressed files on the C: drive at 5 I got this error msg on the dell open manage server admin page:
2095 Tue Nov 16 19:50:56 2010 Storage Service SCSI sense data Sense key: 3 Sense code:11 Sense qualifier: 0: Physical Disk 0:1 Controller 0, Connector 0
2095 Tue Nov 16 19:50:56 2010 Storage Service SCSI sense data Sense key: 3 Sense code:11 Sense qualifier: 0: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 19:50:56 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 19:49:26 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 19:44:26 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 19:39:25 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 19:34:25 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 19:29:25 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 19:24:25 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 19:19:25 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 19:14:23 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 19:09:22 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2095 Tue Nov 16 19:08:42 2010 Storage Service SCSI sense data Sense key: 3 Sense code:11 Sense qualifier: 0: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 19:08:42 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 19:04:17 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 18:59:17 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2095 Tue Nov 16 18:57:07 2010 Storage Service SCSI sense data Sense key: 3 Sense code:11 Sense qualifier: 0: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 18:57:07 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 18:54:17 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2051 Tue Nov 16 18:52:30 2010 Storage Service Physical disk degraded: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 18:52:30 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
1012 Tue Nov 16 18:52:12 2010 Instrumentation Service IPMI status Interface: User
1001 Tue Nov 16 18:52:12 2010 Instrumentation Service Server Administrator startup complete
1008 Tue Nov 16 18:52:12 2010 Instrumentation Service Systems Management Data Manager Started
1000 Tue Nov 16 18:52:09 2010 Instrumentation Service Server Administrator starting
2051 Tue Nov 16 17:50:23 2010 Storage Service Physical disk degraded: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 17:50:23 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
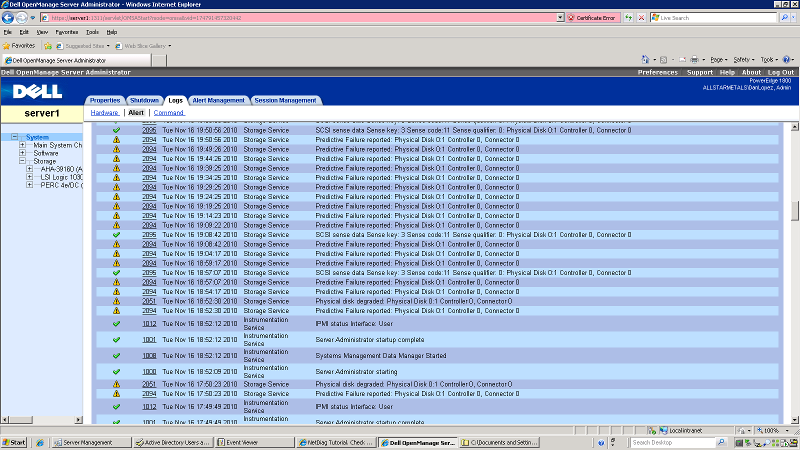
any other suggestions would be helpful, oh and we have a Raid 5 array if that helps.
about the time I ran a diskclean up and compressed files on the C: drive at 5 I got this error msg on the dell open manage server admin page:
2095 Tue Nov 16 19:50:56 2010 Storage Service SCSI sense data Sense key: 3 Sense code:11 Sense qualifier: 0: Physical Disk 0:1 Controller 0, Connector 0
2095 Tue Nov 16 19:50:56 2010 Storage Service SCSI sense data Sense key: 3 Sense code:11 Sense qualifier: 0: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 19:50:56 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 19:49:26 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 19:44:26 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 19:39:25 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 19:34:25 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 19:29:25 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 19:24:25 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 19:19:25 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 19:14:23 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 19:09:22 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2095 Tue Nov 16 19:08:42 2010 Storage Service SCSI sense data Sense key: 3 Sense code:11 Sense qualifier: 0: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 19:08:42 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 19:04:17 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 18:59:17 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2095 Tue Nov 16 18:57:07 2010 Storage Service SCSI sense data Sense key: 3 Sense code:11 Sense qualifier: 0: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 18:57:07 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 18:54:17 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2051 Tue Nov 16 18:52:30 2010 Storage Service Physical disk degraded: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 18:52:30 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
1012 Tue Nov 16 18:52:12 2010 Instrumentation Service IPMI status Interface: User
1001 Tue Nov 16 18:52:12 2010 Instrumentation Service Server Administrator startup complete
1008 Tue Nov 16 18:52:12 2010 Instrumentation Service Systems Management Data Manager Started
1000 Tue Nov 16 18:52:09 2010 Instrumentation Service Server Administrator starting
2051 Tue Nov 16 17:50:23 2010 Storage Service Physical disk degraded: Physical Disk 0:1 Controller 0, Connector 0
2094 Tue Nov 16 17:50:23 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
any other suggestions would be helpful, oh and we have a Raid 5 array if that helps.
I am doubtful that is related to your problem unless some of the system files have become corrupted but it implies one of the disks in the array is about to fail. I would address this immediately. From the dell site:
Error #2094
Description: Predictive Failure reported.
Cause: The physical disk is predicted to fail. Many physical disks contain Self Monitoring Analysis and Reporting Technology (SMART). When enabled, SMART monitors the health of the disk based on indications such as the number of write operations that have been performed on the disk.
Action: Replace the physical disk. Even though the disk may not have failed yet, it is strongly recommended that you replace the disk. If this disk is part of a redundant virtual disk, perform the Offline task on the disk; replace the disk; and then assign a hot spare and the rebuild will start automatically. If this disk is part of a nonredundant disk, back up your data immediately. If the disk fails, you will not be able to recover the data. If this disk is a hot spare, then unassign the hot spare; perform the Prepare to Remove task on the disk; replace the disk; and assign the new disk as a hot spare.
Error #2094
Description: Predictive Failure reported.
Cause: The physical disk is predicted to fail. Many physical disks contain Self Monitoring Analysis and Reporting Technology (SMART). When enabled, SMART monitors the health of the disk based on indications such as the number of write operations that have been performed on the disk.
Action: Replace the physical disk. Even though the disk may not have failed yet, it is strongly recommended that you replace the disk. If this disk is part of a redundant virtual disk, perform the Offline task on the disk; replace the disk; and then assign a hot spare and the rebuild will start automatically. If this disk is part of a nonredundant disk, back up your data immediately. If the disk fails, you will not be able to recover the data. If this disk is a hot spare, then unassign the hot spare; perform the Prepare to Remove task on the disk; replace the disk; and assign the new disk as a hot spare.
ps:
Error #2051
Description: Physical disk degraded
Cause: A physical disk has reported an error condition and may be degraded. The physical disk may have reported the error condition in response to a check consistency or other operation.
Action: Replace the degraded physical disk. You can identify which disk is degraded by locating the disk that has a red X for its status. Perform a rescan after replacing the disk.
Severity: Warning/Noncritical. See "Alert Severity Levels" for more information.
Clear Alert Number: None.
SNMP Trap Number: 903. See "SNMP Support for Storage Management Alerts" for more information.
Error #2051
Description: Physical disk degraded
Cause: A physical disk has reported an error condition and may be degraded. The physical disk may have reported the error condition in response to a check consistency or other operation.
Action: Replace the degraded physical disk. You can identify which disk is degraded by locating the disk that has a red X for its status. Perform a rescan after replacing the disk.
Severity: Warning/Noncritical. See "Alert Severity Levels" for more information.
Clear Alert Number: None.
SNMP Trap Number: 903. See "SNMP Support for Storage Management Alerts" for more information.
ASKER
okay, so basically it hasn't failed but is going to soon. Rob and on the initial problem im having on the server, where the workstations can't see the domain controler, I don't think there is anything wrong with the workstation because I get errors on other workstations on the domain that are already disconnected, I think the problem would reside somewhere with the server.
>>"it hasn't failed but is going to soon"
The problem with a failing drive is it could be 2 years from now or it could be 2 minutes. A failing drive will often die on the next reboot. Be careful.
It sounds like the trust relationship between server and PC's is breaking.
What does netdiag show from a problematic PC show.
http://www.lan-2-wan.com/Diag-FAQ.htm#q1
The problem with a failing drive is it could be 2 years from now or it could be 2 minutes. A failing drive will often die on the next reboot. Be careful.
It sounds like the trust relationship between server and PC's is breaking.
What does netdiag show from a problematic PC show.
http://www.lan-2-wan.com/Diag-FAQ.htm#q1
ASKER
Rob, i downloaded the app but when I run it, it runs to fast how can I run it on the run command?
ASKER
Netdiag has to be run from the command line.
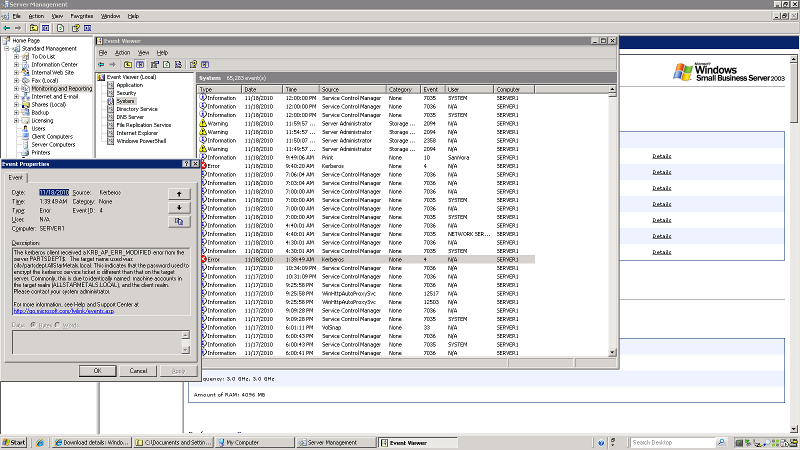
Kerberos issue.....now that is more promising. Kerberos handles all authentication between networked devices. Basically it is the key that allows PC's and servers to talk. Finding the problem can be more difficult, but it likely explains the dropped connections and the inability to enumerate the user and computer lists.
As the message suggests is there any possibility of two devices on the network with the same name, such as 2 reception computers? That is a common cause.
If possible it would be interesting to connect just the reception computer and the server to a single switch. Physically remove everything else from the working network and see if you can join the domain.
Kerberos issue.....now that is more promising. Kerberos handles all authentication between networked devices. Basically it is the key that allows PC's and servers to talk. Finding the problem can be more difficult, but it likely explains the dropped connections and the inability to enumerate the user and computer lists.
As the message suggests is there any possibility of two devices on the network with the same name, such as 2 reception computers? That is a common cause.
If possible it would be interesting to connect just the reception computer and the server to a single switch. Physically remove everything else from the working network and see if you can join the domain.
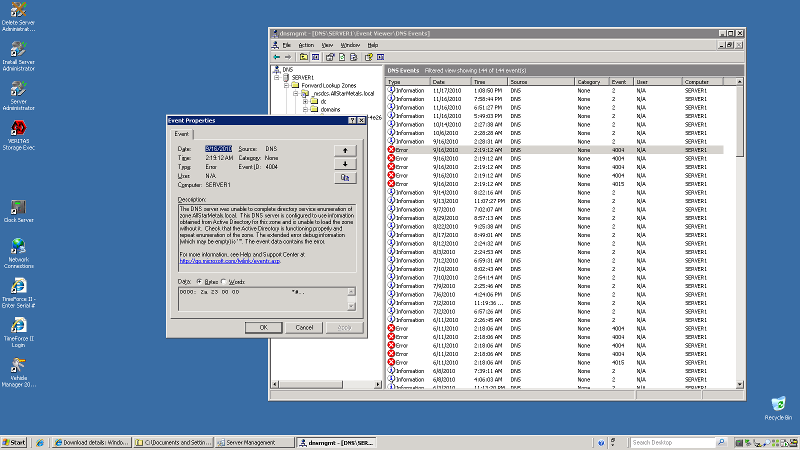
This implies there may be corruption in active directory, which could result in the Kerberos and other issues. I am surprised DCDiag ran clean with these Kerberos and DNS issues. Can you try it again and see if we are seeing gradual degradation? If it looks the same as yesterday no need to post. It would be good to run NetDiag the server at this point. There are different versions of NetDiag it has to be the server version. That you can get from the same site as DCDiag.
ASKER
everything passed except for the IsmServ but as you said earlier it really should have no bearing on the problem. If it is a degredation I haven't seen anything to suggest that. although I did see today that disk error today:
Severity ID Date and Time Category Description
2094 Thu Nov 18 12:04:57 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Thu Nov 18 11:59:57 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Thu Nov 18 11:54:57 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2358 Thu Nov 18 11:50:07 2010 Storage Service The battery charge cycle is complete.: Battery 0 Controller 0
2094 Thu Nov 18 11:49:57 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
but not as prevalent. Could I simply swap out the failing drive for another? It configured in a Raid 5 array SCSi type.
Severity ID Date and Time Category Description
2094 Thu Nov 18 12:04:57 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Thu Nov 18 11:59:57 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2094 Thu Nov 18 11:54:57 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
2358 Thu Nov 18 11:50:07 2010 Storage Service The battery charge cycle is complete.: Battery 0 Controller 0
2094 Thu Nov 18 11:49:57 2010 Storage Service Predictive Failure reported: Physical Disk 0:1 Controller 0, Connector 0
but not as prevalent. Could I simply swap out the failing drive for another? It configured in a Raid 5 array SCSi type.
was the disk error in the event log?
ASKER
Not sure, well Rob I'm heading home now but if you got time tomorrow we can go over the disk error. Once again thank you so much for your help.
Sorry I haven't been much help so far.
My concern is if the disk is going that means there are bad sectors. Bad sectors can mean corrupt data, which could explain the Kerberos/AD/DNS issues.
Have a great evening!
--Rob
My concern is if the disk is going that means there are bad sectors. Bad sectors can mean corrupt data, which could explain the Kerberos/AD/DNS issues.
Have a great evening!
--Rob
ASKER
That is the same error that Dell reported. The Dell utility writes it to the event log. I thought it might be a Windows error.
Yes, it depends why Dell is reporting the "predicted failure". In most cases it is because it discovered bad sectors on the hard drive. In that case it marks those sectors as bad and doesn't use them anymore, If this is detected when writting to the drive it is not a problem as it will use another sector, but if the sector become unusable after data was written to it, it can be lost. However when thinking about it, in a raid configuration that should not be a problem as everything is duplicated in one way or another.
There does however seem like there may be some system file corruption.
Yes, it depends why Dell is reporting the "predicted failure". In most cases it is because it discovered bad sectors on the hard drive. In that case it marks those sectors as bad and doesn't use them anymore, If this is detected when writting to the drive it is not a problem as it will use another sector, but if the sector become unusable after data was written to it, it can be lost. However when thinking about it, in a raid configuration that should not be a problem as everything is duplicated in one way or another.
There does however seem like there may be some system file corruption.
ASKER
I believe that is the system file that is corrupt as well, I don't really know what else could be the issue.
That message says that Verizon's server (4.2.2.2) cannot resolve the IP 192.168.0.2 which makes sense as it would not be possible.
Either you still have the workstation pointing to 4.2.2.2 for DNS (possibly an alternate) or the server's DNS is not working properly and it is somehow forwarding ALL requests to Verizon.
Either you still have the workstation pointing to 4.2.2.2 for DNS (possibly an alternate) or the server's DNS is not working properly and it is somehow forwarding ALL requests to Verizon.
ASKER
Difficult conflict. If you add 4.2.2.2 to the workstation I guarantee you will not be able to join the domain. When you remove it you cannot access the internet because it sounds like you have corruption as mentioned. If this is the case you might be best to do a restore or contact Microsoft support to try to rebuild.
ASKER
something is wrong with the DNS, all my clients have alternate 4.2.2.2 dns and the ones that don't can't connect to the internet or the cant ping server by name.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Thanks for all the help Rob, I will look into the matter.
Thanks itmandan. Sorry I was not of more help.
Cheers!
--Rob
Cheers!
--Rob





Usually this is a DNS issue where the client is missing the DNS suffix in it's TCP/IP configuration and/or DNS points to something other than the server. Pointing to a router or ISP, even as an alternate, can cause this problem.