carradonna
asked on
Class and Sequence Diagram
Hi,
I am using a case study to create a class diagram and a sequence diagram but am becoming a bit unstuck...
The case study is as follows;
Liverpool chemicals makes a range of intermediate ingredients for household and other chemical goods. Examples are perfumes, fixers and colours. These are manufactured at 2 plants. One in Liverpool, one in St Helens.
After manufacture goods are placed into barrels (square ones). They are then moved to a distribution warehouse operated by a third party logistics company and is referred to as Leyland Depot. All goods leave the factory site upon being barreled up. Normally they are rolled onto special 'rool on roll off' barrel containers that are then shipped to Leyland Depot. All outgoing goods to customers are 'picked' at leyland depot and sent out through a variety of hauliers.
On occasion Leyland depot is full. At this point each factory has an overflow container park which holds a buffer stock. Wach factory has 2 hauliers on retainer to put these materials into these buffer stocks and move them when space allows to Leyland Depot. These containers are loaded by forklift and hence more expensive to run than the roll of roll off system.
================
I have attached a copy of a Visio image with what I have captured to date and it does not look correct!
Any help would be appreciated.
Cheer.
Doc2.docx
I am using a case study to create a class diagram and a sequence diagram but am becoming a bit unstuck...
The case study is as follows;
Liverpool chemicals makes a range of intermediate ingredients for household and other chemical goods. Examples are perfumes, fixers and colours. These are manufactured at 2 plants. One in Liverpool, one in St Helens.
After manufacture goods are placed into barrels (square ones). They are then moved to a distribution warehouse operated by a third party logistics company and is referred to as Leyland Depot. All goods leave the factory site upon being barreled up. Normally they are rolled onto special 'rool on roll off' barrel containers that are then shipped to Leyland Depot. All outgoing goods to customers are 'picked' at leyland depot and sent out through a variety of hauliers.
On occasion Leyland depot is full. At this point each factory has an overflow container park which holds a buffer stock. Wach factory has 2 hauliers on retainer to put these materials into these buffer stocks and move them when space allows to Leyland Depot. These containers are loaded by forklift and hence more expensive to run than the roll of roll off system.
================
I have attached a copy of a Visio image with what I have captured to date and it does not look correct!
Any help would be appreciated.
Cheer.
Doc2.docx
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
This should give you a good start (see class diagram). If you navigate through the relationships and think about what makes sense for each of these types of objects should look like, you will see I think that it satisfies most of your described requirements.
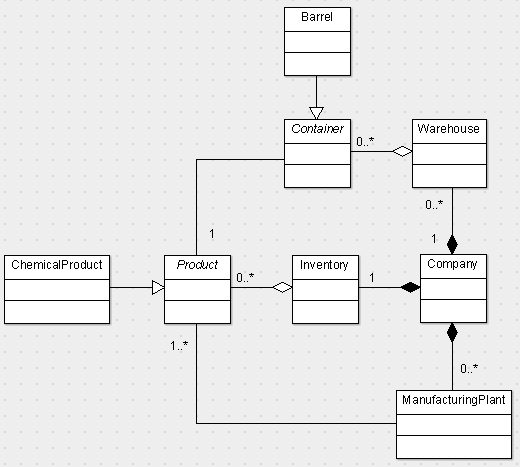
E.g. Your Company has an Inventory of Products. Products are made in ManufacturingPlants and are stored in Containers (such as Barrels). And so on...
Then, think about what important attributes and behaviors you need for each. E.g. a Product certainly has a price, a name, a description, and possibly a unique ID. A Product should be able to tell you its type (e.g. ChemicalProduct), whether it's dangerous (isFlammable() method perhaps), where it's manufactured (Set of ManufacturingPlants), and where it's located (which Warehouse).
You get the idea.
Then, sequence diagrams just walk through some public behaviors. E..g
1- Warehouse creates a Product
2- Product is placed in a Container
3- Container is moved to a Warehouse
4- Inventory is updated to include the Product
5- ...
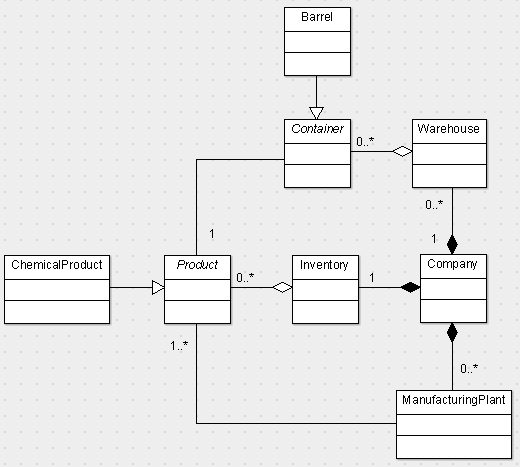
E.g. Your Company has an Inventory of Products. Products are made in ManufacturingPlants and are stored in Containers (such as Barrels). And so on...
Then, think about what important attributes and behaviors you need for each. E.g. a Product certainly has a price, a name, a description, and possibly a unique ID. A Product should be able to tell you its type (e.g. ChemicalProduct), whether it's dangerous (isFlammable() method perhaps), where it's manufactured (Set of ManufacturingPlants), and where it's located (which Warehouse).
You get the idea.
Then, sequence diagrams just walk through some public behaviors. E..g
1- Warehouse creates a Product
2- Product is placed in a Container
3- Container is moved to a Warehouse
4- Inventory is updated to include the Product
5- ...
@marklorenz: some errors in your diagram:
> Wharehouse won't aggregate Container, this is a simple association (their life's cycle are not dependent
> Barel won't inherit from Container
> Company -> Plant relationship is not 0..*. Currently it is 2..2, but could be designed as 1..* (Company must have at least one Plant)
And some entities are missing : Hauliers, Buffer park, ...
> Wharehouse won't aggregate Container, this is a simple association (their life's cycle are not dependent
> Barel won't inherit from Container
> Company -> Plant relationship is not 0..*. Currently it is 2..2, but could be designed as 1..* (Company must have at least one Plant)
And some entities are missing : Hauliers, Buffer park, ...
Nice work Xper4net!! chapeau!
ASKER
Thank you all for your responses.
Xper4net, thank you for the breakdown, I will try and use that type of methodology in the future.
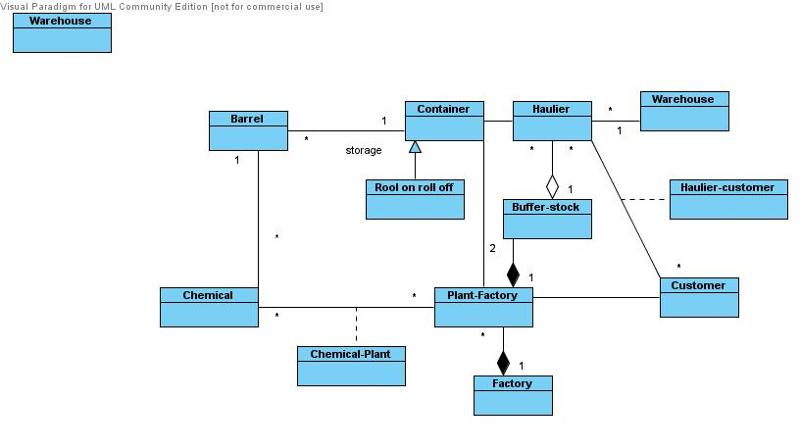
Zopilote that is an excellent diagram many thanks, I have just seen my lecturer a moment ago and he advised that I should be looking at having a 'journeys' class since hauliers and barrels can make many journeys?
Xper4net, thank you for the breakdown, I will try and use that type of methodology in the future.
Zopilote that is an excellent diagram many thanks, I have just seen my lecturer a moment ago and he advised that I should be looking at having a 'journeys' class since hauliers and barrels can make many journeys?
Cardinality is easily changed to fit your requirements. And missing classes can be added too - left something for you!
A note: the extra stock areas don't need a separate class IMO. In fact, making them different class would be undesirable - they are the same except just stored in a different location!
Finally, for "journey", generally this is handled as an Event type object. Examples include SalesTransaction (in retail). In your case, this would probably be a TransportEvent.
A note: the extra stock areas don't need a separate class IMO. In fact, making them different class would be undesirable - they are the same except just stored in a different location!
Finally, for "journey", generally this is handled as an Event type object. Examples include SalesTransaction (in retail). In your case, this would probably be a TransportEvent.
@Zopilote : a little mismatch, as there's no inheritance between Container and RollOnRollOff
I just have a little time to transcript my own analysis:
Chemicals.png
I just have a little time to transcript my own analysis:
Chemicals.png
This question has been classified as abandoned and is closed as part of the Cleanup Program. See the recommendation for more details.
btw, you can download for free Visual Paradigm
Doc-barrel.docx