sinister_kris
asked on
Outlook To-Do List Export
Hi,
Currently have a client using Google Apps via IMAP. The profile corrupted in outlook and I needed to transfer everything to a new profile. The To-Do List under tasks, did not transfer.
How can I export the Outlook To-Do list to a pst/csv and transfer it to another profile?
Thanks
Currently have a client using Google Apps via IMAP. The profile corrupted in outlook and I needed to transfer everything to a new profile. The To-Do List under tasks, did not transfer.
How can I export the Outlook To-Do list to a pst/csv and transfer it to another profile?
Thanks
ASKER
Thx for your reply.
That's the procedure for another version of outlook, and that's a general way to exporting a .pst.
To export in 2010 it's File -> Open -> Import -> Export to a file.
Secondly, as stated, it doesn't export the To-Do List. I'm looking to an export of the Outlook To-Do List.
Thanks
That's the procedure for another version of outlook, and that's a general way to exporting a .pst.
To export in 2010 it's File -> Open -> Import -> Export to a file.
Secondly, as stated, it doesn't export the To-Do List. I'm looking to an export of the Outlook To-Do List.
Thanks
Sorry, didn't notice the 2010 part.
I don't see anything about the To-Do list not exporting. In fact I don't see anything in your question about you having tried an export. You note that the profile did not transfer, but there's no mention that the transfer you tried was via an export.
Maybe I should back up a step and ask what you mean when you say "To-Do List". If that means the task list and if you've already tried exporting it and that failed, then it seems reasonable that the data is corrupt and can't be exported.
I don't see anything about the To-Do list not exporting. In fact I don't see anything in your question about you having tried an export. You note that the profile did not transfer, but there's no mention that the transfer you tried was via an export.
Maybe I should back up a step and ask what you mean when you say "To-Do List". If that means the task list and if you've already tried exporting it and that failed, then it seems reasonable that the data is corrupt and can't be exported.
ASKER
No problemo :)
Yeah, I'm transferring profiles by Exporting/Importing pst's in 2010. What I did was create a new profile, added the email credentials, then went to import the calendar, contacts, etc.
Let's say I was trying to export JUST the To-Do List in Outlook to import to another PC. Where would you do that?
When I say To-Do List, if you go to "Tasks", It's the flag icon under "My Tasks". However, it's not under the tasks because it's just a flag for follow up, not a created task.
Hope that clears things up :)
Kris
Yeah, I'm transferring profiles by Exporting/Importing pst's in 2010. What I did was create a new profile, added the email credentials, then went to import the calendar, contacts, etc.
Let's say I was trying to export JUST the To-Do List in Outlook to import to another PC. Where would you do that?
When I say To-Do List, if you go to "Tasks", It's the flag icon under "My Tasks". However, it's not under the tasks because it's just a flag for follow up, not a created task.
Hope that clears things up :)
Kris
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
Right. That's not an actual list. It's a view. The items that appear in the view are the items that are flagged. If you've already copied over the items, then you already have everything.
ASKER
But they are not there. :)
That's what I mean. When you add a follow up flag to the email, it creates this To Do list.
Is there a way to transfer the flag settings also or just by itself?
That's what I mean. When you add a follow up flag to the email, it creates this To Do list.
Is there a way to transfer the flag settings also or just by itself?
Ok, let's start a the beginning. Are the items there? If yes, do they have flags?
ASKER
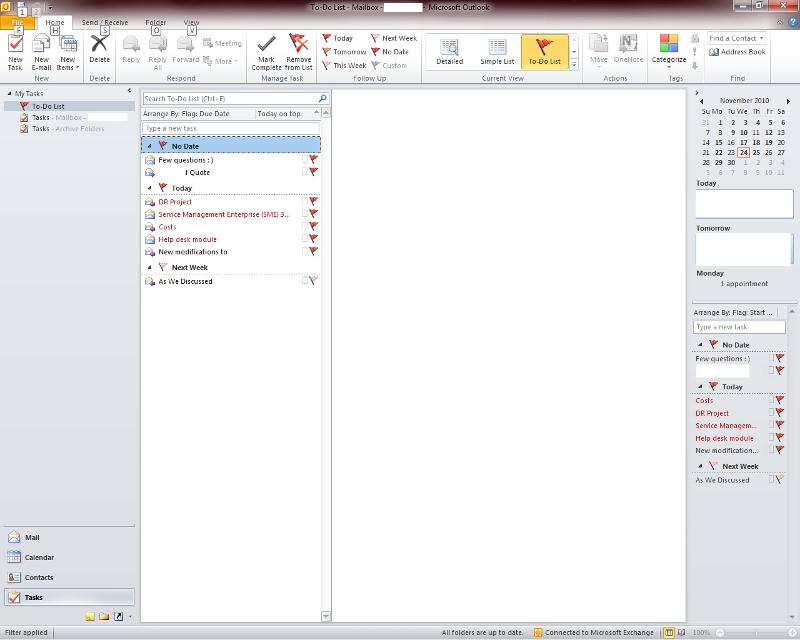
Yup, they are in the picture. :)
It's impossible for me to know if the screen shot is from a working system that you're using as an example or the affected system.
So what is it that's not showing up? If these are are the flagged items, then what's missing? I see 7 flagged items on the To-Do list on the right-hand pane and 7 items in the view list.
So what is it that's not showing up? If these are are the flagged items, then what's missing? I see 7 flagged items on the To-Do list on the right-hand pane and 7 items in the view list.
ASKER
The flagged items are the ones that are not showing up on the new profile.
That's a picture of the flagged items BEFORE the transfer to the new.
That's a picture of the flagged items BEFORE the transfer to the new.
So then we're back to my original question. Are the missing items there AFTER the transfer? By "there" I don't mean in the To-Do list, I mean in tasks, the inbox, etc. Keeping in mind that the To-Do list is a virtual list, not actual items, that is based on items that are flagged. Are the items themselves there? If yes, are they flagged?
ASKER
So then we're back to my original question. Are the missing items there AFTER the transfer?
Yes, tasks are there. I can export tasks via CSV and import them. That works.
If yes, are they flagged?
No, they are not flagged.
Keeping in mind that the To-Do list is a virtual list, not actual items
Does this mean it cannot be exported by itself to a CSV of some sort since it's 'Virtual'?
Thanks
Yes, tasks are there. I can export tasks via CSV and import them. That works.
If yes, are they flagged?
No, they are not flagged.
Keeping in mind that the To-Do list is a virtual list, not actual items
Does this mean it cannot be exported by itself to a CSV of some sort since it's 'Virtual'?
Thanks
Not just tasks, the missing tasks.
If the missing tasks are there, but are not flagged, then that's why they don't appear in the To-Do list.
No, it cannot be exported because it doesn't exist. It's a list that is the result of a search. The underlying items can be exported, but you indicate that you've already done that. The problem appears to be that the items are losing their flag when they are exported/imported. Without they falg they don't qualify to make it into the To-Do list.
If the missing tasks are there, but are not flagged, then that's why they don't appear in the To-Do list.
No, it cannot be exported because it doesn't exist. It's a list that is the result of a search. The underlying items can be exported, but you indicate that you've already done that. The problem appears to be that the items are losing their flag when they are exported/imported. Without they falg they don't qualify to make it into the To-Do list.
ASKER
The problem appears to be that the items are losing their flag when they are exported/imported.
Correct. Any way to keep their flags? :)
Correct. Any way to keep their flags? :)
Have you tried exporting to a PST file instead of to a CSV?
ASKER
Yep, both ways!
Then without being able to see for myself what's going on, I'm at a loss to explain what's happening. If the flag is set on the source item, then it should be set on the imported item. If it's not, then I don't know why.
ASKER
Incredibly helpful, but not the answer i was looking for to solve the problem.
1. Click File and select Import and Export.
2. Select Export to a file
3. Select the type of file to export to
4. Select the folder you want to export
Once you have the new profile in place perform the same steps this time selecting import instead of export.