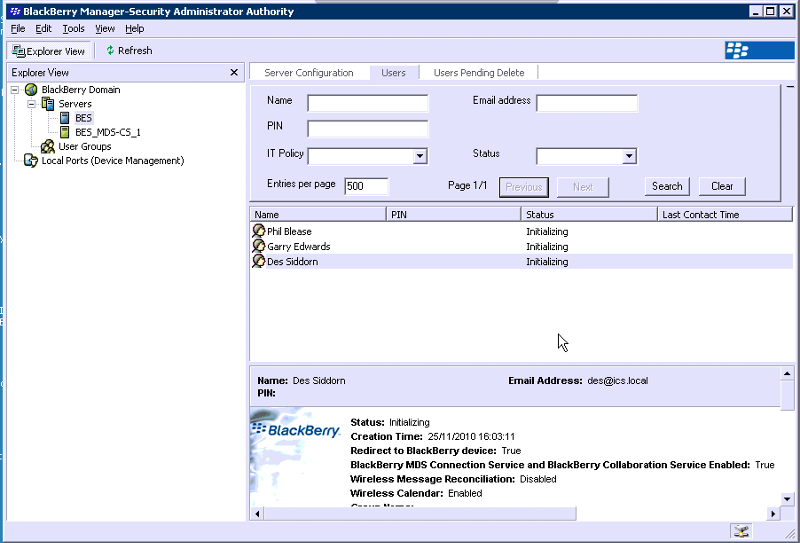
Blackberry Users stuck on initializing on new BES Server
Hi Guys, got a new blackberry install sat on a 2003 standrad and done all the 'hard bit' the exchange server talks to it fine, the sql database is cool, and ive tested the serp login with the utility you get and it talks to RIM fine and logs on and comes back ok.
can anyone suggest whats stopping the users from moving past initialization??
oh yeah i was there 72 hours ago and ive logged in remotely just and they are still sat there so they are well and truly stuck :)
dead grateful to any help - im back there tomorrow! :)
can anyone suggest whats stopping the users from moving past initialization??
oh yeah i was there 72 hours ago and ive logged in remotely just and they are still sat there so they are well and truly stuck :)
dead grateful to any help - im back there tomorrow! :)
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
Hi, this might sound a stupid question here , but as you can not rule anything out I have to ask, have you run enterprise activation on the handheld?
Hi,
As above, I assume that you have created an activation password, communicated this to the end users and they have entered this into the Enterprise Activation screen on the device?
Normally there are several things that will prevent an OTA Activation (assuming this is what you are doing):
1. If the Enterprise Service Policy is enabled, has the PIN been added to the 'allowed' devices list?
2. Make sure the SIMs are provisioned with the correct service plan
3. Make sure that any mail 'sweepers' are not blocking emails from blackberry.net or blackberry.com - these have an attachment which can be intercepted.
4. Make sure there are no mailbox rules which are moving the message to a sub-folder, putting it in junk etc.
Hope this helps,
Robmobility.
As above, I assume that you have created an activation password, communicated this to the end users and they have entered this into the Enterprise Activation screen on the device?
Normally there are several things that will prevent an OTA Activation (assuming this is what you are doing):
1. If the Enterprise Service Policy is enabled, has the PIN been added to the 'allowed' devices list?
2. Make sure the SIMs are provisioned with the correct service plan
3. Make sure that any mail 'sweepers' are not blocking emails from blackberry.net or blackberry.com - these have an attachment which can be intercepted.
4. Make sure there are no mailbox rules which are moving the message to a sub-folder, putting it in junk etc.
Hope this helps,
Robmobility.
ASKER