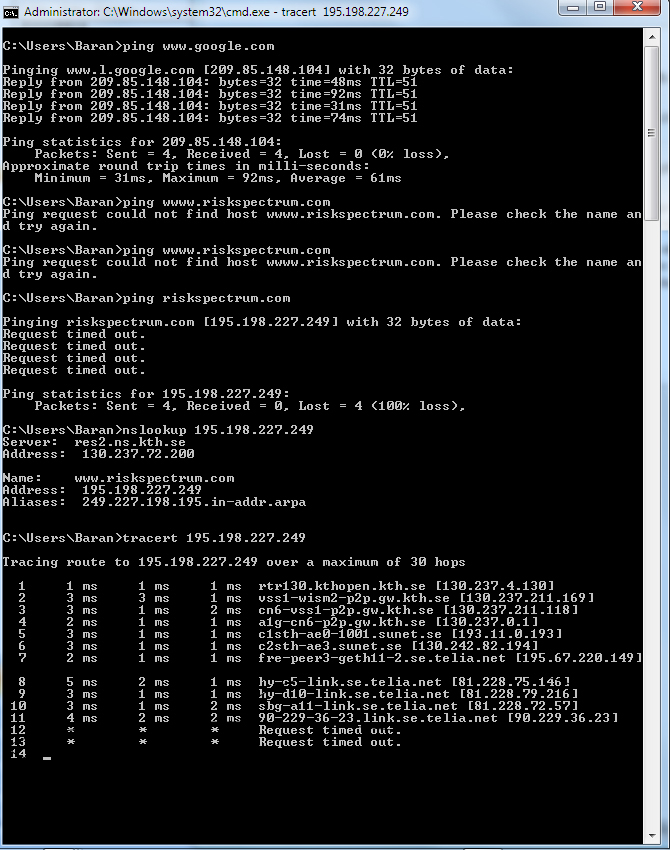
Could someone tell me the reason and fix for the ping failure for the following IP?
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Thank you. One final thing, when I try for the address as attached, why isn't it replying?
confidentiality.txt
confidentiality.txt
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
I seem to connect via telnet <addr.> 80 but I couldn't see anything when I press <enter> multiple times.
yeah, not 100% sure it could depend on other factors- don't have telnet on this machine and don't really want to install it (borrowing gf's laptop to reply to you). Sounds like everything's working the way it should though- not sure why you're not getting redirected when you go to that URL in your browser.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
>>I think to get a response via telnet you would have to send an HTTP request that the server could >>respond to.
Could you give me an example for HTTP requests?
Kind regards.
Could you give me an example for HTTP requests?
Kind regards.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER