How do I stop the UDP port 5353 mDNS floods on our LAN?
I've looked all over the Internet trying to find a good solution to my problem, to no avail.
Lately, we are seeing our LAN brought to its knees by mDNS floods.
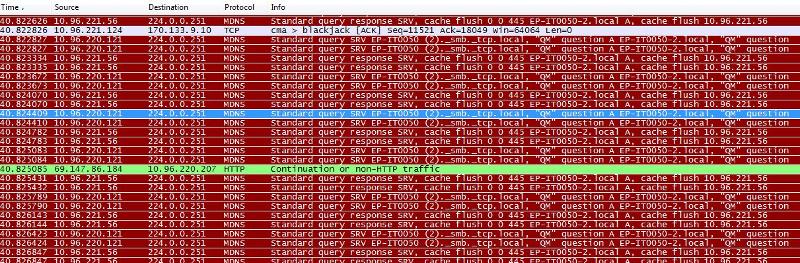
When analyzing the traffic using WireShark, I am seeing that numerous devices are broadcasting and responding using UDP port 5353 to a multicast IP address of 224.0.0.251.
Most of these devices are laptops and PCs with iTunes installed, and the bonjour service running. The same happens for printers with bonjour enabled, and any iPods and iPhones that connect to the wireless network.
I keep turning off Bonjour on each PC, and printer, and tell each user to disconnect their iPod or iPhone from the company wireless network, but all it takes is one person to get a new iPhone or iPod, and it starts happening again.
What can I do to track down the specific culprit (if there is one), and/or what can be done on a larger/centralized scale to avoid the micromanagement nightmare of kicking all of these devices off the network one by one?
Embedded is an image showing the traffic in WireShark.
Lately, we are seeing our LAN brought to its knees by mDNS floods.
When analyzing the traffic using WireShark, I am seeing that numerous devices are broadcasting and responding using UDP port 5353 to a multicast IP address of 224.0.0.251.
Most of these devices are laptops and PCs with iTunes installed, and the bonjour service running. The same happens for printers with bonjour enabled, and any iPods and iPhones that connect to the wireless network.
I keep turning off Bonjour on each PC, and printer, and tell each user to disconnect their iPod or iPhone from the company wireless network, but all it takes is one person to get a new iPhone or iPod, and it starts happening again.
What can I do to track down the specific culprit (if there is one), and/or what can be done on a larger/centralized scale to avoid the micromanagement nightmare of kicking all of these devices off the network one by one?
Embedded is an image showing the traffic in WireShark.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
Bonjour is the worst piece of crap ever designed. It is a resource and network hog that should never be.
The only other thing you can do is create some VLANs and route between them, this will contain the broadcasts to devices on each VLAN and lessen the load a little.
The only other thing you can do is create some VLANs and route between them, this will contain the broadcasts to devices on each VLAN and lessen the load a little.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
Ugh, we're buried in these multicast packets right now as well. Surely there's a way to control these. We have a fairly open environment with lots of interns and people coming and going, in this case the Mac that's flooding our network isn't corporately owned so we're "not allowed" to touch it. The guy's there to do some work... this kind of scenario isn't uncommon. I've not found any practical solution to this, it's very frustrating.
I would compose a corporate policy related to computer and network usage, that has language included that stipulates that only company owned assets are granted full access. Once that policy has been approved, for network and information security reasons, of course... you can take actions, through your firewall to either block the MAC address of said Mac, or you can create specific rules that block all traffic from the specified computer, except for explicitly what you want to allow.
Yeah... that works fine for traffic going through a firewall, but this is within the LAN. I'd need to do something like creating a guest VLAN for any non-corporate machine... which ends up being massive maintenance for ongoing stuff...
For the record: http://support.apple.com/kb/HT3789 tells how to disable the service on a Mac. But this is still not really what we need.
For the record: http://support.apple.com/kb/HT3789 tells how to disable the service on a Mac. But this is still not really what we need.
Does your firewall also do DHCP? If so, you can control it that way, or you can set your DHCP server to give that MAC an address in a different scope, then control it through your firewall, by forcing it to use a gateway IP that is your firewall, to access anything else on your network.
we use a Sonicwall firewall, and I can setup LAN to LAN rules on the firewall, and even when the target computer does not directly have to pass through the firewall the rules that I have set in place are still affective.
ASKER
The people on the network are allowed to be there, so I'm not worried about that. And, if I am not mistaken, there will be some application development going on for such devices. So, I need to find out why this is happening, and kill the cause.
Correct me if I am wrong, but shouldn't a network be able to handle iphones, ipads and other devices that use the bonjour service without screeching to a halt?
All it takes is literally 1 new apple device, or itunes installation for the mass broadcasting to freeze our switches.
When monitoring with Wireshark, when the network is normal, and under heavy load, there might be an average of 300 packets per second, but when one of these devices enters the network, it jumps to about 1800, and connections start getting dropped.
I have seen packet flood control on my 3com switches, and I want to turn it on, but I am not sure if the packet rate control is per port or for the entire switch bank.