Is there a limit per Cisco on the amount of Cisco 3550 48 port switches that can daisychained together without degrading performance
Is there a limit on how many Cisco 3550 48 port switches that I can daisy chain together until performance starts to degrade? Thanks.
Hi,
There is no limit, but it is better to make start topology, with full gigabit center seitches!
Or you need to make ring topology, because it gives you backup lines...
I advise to configure mstp, or rstp!
How many the average bandwidth per users?
Best regards,
Istvan
There is no limit, but it is better to make start topology, with full gigabit center seitches!
Or you need to make ring topology, because it gives you backup lines...
I advise to configure mstp, or rstp!
How many the average bandwidth per users?
Best regards,
Istvan
There is a limit in the spanning-tree diameter. Which means the number of hops from the root bridge.
And you should count the largest number of hops possible in your network, or set bridge priorities so that you are shure that the most central switche takest the root role. And secondary root if the primary dies. If you have a network with a possibly big diameter, you have to be sure that the switches far out at the leaves never gets to be root.
The default diameter is 7 but can be configured to a smaller value for faster convergence.
If you exceed the diameter the BPDU:s are lost and the switches in the network don't have a consistent view of who is the root. This can cause instability, and even loops.
So, if you know what you do and set the priority right (middle switch) you can have 15 switches daisy chained. But in a good network design you should simulate that links goes down and count the hops in the worst possible case, and that shouldn't be more than 7 hops end-to-end
And you should count the largest number of hops possible in your network, or set bridge priorities so that you are shure that the most central switche takest the root role. And secondary root if the primary dies. If you have a network with a possibly big diameter, you have to be sure that the switches far out at the leaves never gets to be root.
The default diameter is 7 but can be configured to a smaller value for faster convergence.
If you exceed the diameter the BPDU:s are lost and the switches in the network don't have a consistent view of who is the root. This can cause instability, and even loops.
So, if you know what you do and set the priority right (middle switch) you can have 15 switches daisy chained. But in a good network design you should simulate that links goes down and count the hops in the worst possible case, and that shouldn't be more than 7 hops end-to-end
ASKER
After Daisy Chaining so many switches together, is there a point where network performace is degraded?
ASKER
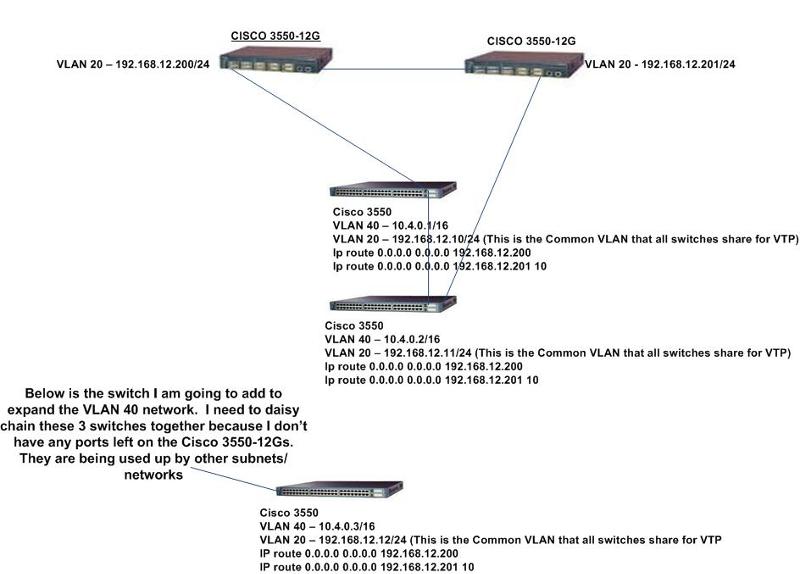
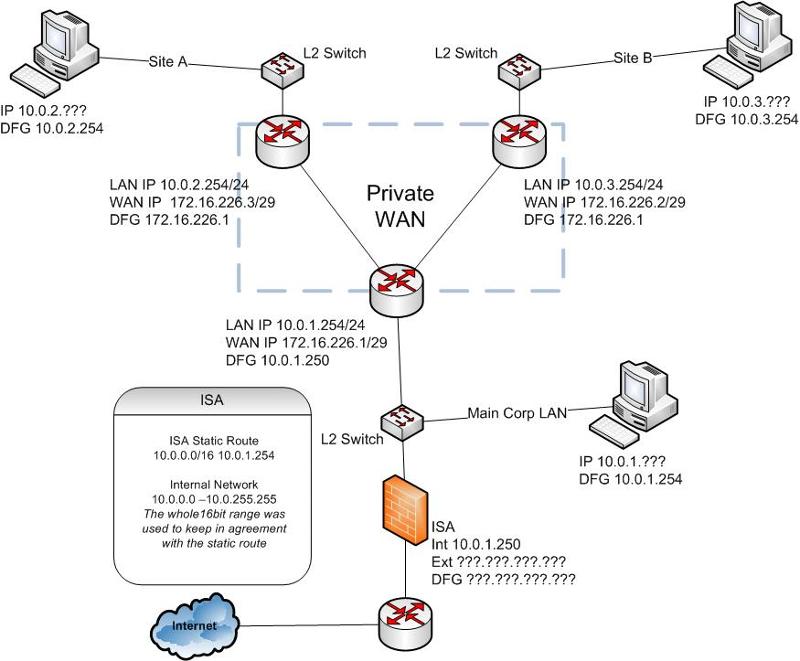
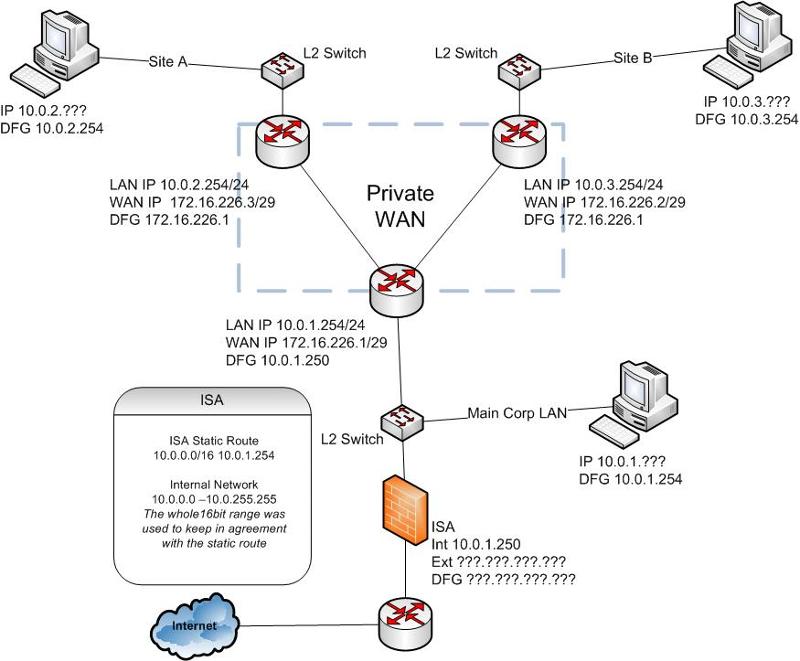
I attached a network diagram showing what I am trying to do. I currently have two cisco 3550 switches that are in the 10.4.0.0/16 network, and I need to add a third. You will see on the diagram how I have these switches wired. What I need to do is add a third switch to this 10.4.0.0/16 network. I'm not sure the best approach for wiring would be. Also is there any special STP configurations I need? I know that STP is enabled by default, I have not done any addition STP configurations. Do I need to? 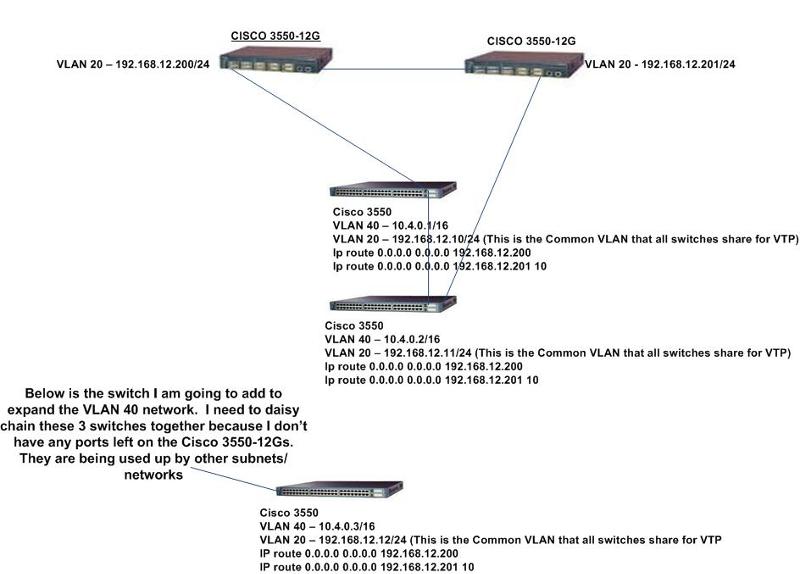
Hi,
I advise to make star toppology, and make the two CISCO 3650-12G to the L3 devices and connect all swirche to booth of them!
I advise to make star toppology, and make the two CISCO 3650-12G to the L3 devices and connect all swirche to booth of them!
ASKER
I can't connect all switches to the 3550-12Gs because I don't have enough ports. I have other subnets/networks not shown in the topology that are plugged into the 12Gs. Currently the 12Gs only have one more port available. This is why I am trying to daisy chain the switches that are in the 10.4.0.0/16 subnet together.
If you want the best throughput you should aim for a star topology, just as ikalmar says.
When you connect another switch in the loop, the only impact on performance is that more users uses the same uplink to the central switches.
Thats all there is. So you have to determine from the present bandwitdh usage, and expected future bandwidth usage if there is enough head-room.
In case ther isn't head-room you have to invest some money to be able to build a star topology.
When you connect another switch in the loop, the only impact on performance is that more users uses the same uplink to the central switches.
Thats all there is. So you have to determine from the present bandwitdh usage, and expected future bandwidth usage if there is enough head-room.
In case ther isn't head-room you have to invest some money to be able to build a star topology.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Thanks. pwindell, do you any documentation from Cisco that talks about how IP Segments should never be larger than 250-300 hosts? To invest more money into my infrastructure, I need to provide some documentation to my boss.
My concern is that in the next year I could be up to 7 or 8 48 port switches in the 10.4.0.0/16 network, and I'm trying to plan now for the future. Tonight I will be adding the third switch to to this subnet, and it sounds like I don't want to go over 4 switches daisy chained together. Its seems like I am growing out of the 3550-12Gs. Like I said, I only have one port available left on the 12Gs. What equipment would recommend for me? I do have more 3550-12Gs that I could daisy chain together so I would have more ports, but this doesn't seem like this would be a good solution. Any ideas would be greatly appreciated. thanks.
My concern is that in the next year I could be up to 7 or 8 48 port switches in the 10.4.0.0/16 network, and I'm trying to plan now for the future. Tonight I will be adding the third switch to to this subnet, and it sounds like I don't want to go over 4 switches daisy chained together. Its seems like I am growing out of the 3550-12Gs. Like I said, I only have one port available left on the 12Gs. What equipment would recommend for me? I do have more 3550-12Gs that I could daisy chain together so I would have more ports, but this doesn't seem like this would be a good solution. Any ideas would be greatly appreciated. thanks.
I wish I had. I only had it in hard copy form and it came from the Cisco Textbooks from their CCNA Classes,...worse yet it was not like they had a "chapter" on it you could flip to,...it was only mentioned in passing "along the way" as if it was a "given" and everyone just already knew it to start with. If you search on the Net you will find all kinds of conflicting debate on that,...much of which I blame on the schools doing such a poor job of teaching networking techniques because there is so much of an over-focus on graduating Programmers rather than Networks. I'm on the IT Advisory Committee of a local college that teaches the CCNA courses and it always seems to be teetering on whether they will continue teaching all 4 classes of it needed to fully train for the CCNA,...while the classes on teaching programming languages are going strong. That may be why so many Programmers are weak in networking and often write Applications built on horrible networking techniques when you try to incorporate the Applications into a network.
The golden rule (whether anybody remembers it anymore) is "for every 200 Hosts create a new 24 bit segment. Smaller segments are ok as long as you don't go overboard with the idea, but you need to keep segments no larger than the typical 24 bit mask (254 host).
The primary debate comes from the fact that we now have 1gig and 10gig Ethernet speeds now and also have switching which eliminates collisions experienced by Hubs. However that only makes the issue less noticeable,...it doesn't make it go away. Since a 100mbps LANs still seems fast to "human perception" you have to overload a 1Gig network pretty heavy before it degrades below the performance of a 100mbps LAN and becomes "humanly" noticeable. But if you actually want your 1Gig LAN to actually fully perform like a 1Gig LAN (and not like a 100mpbs LAN) then follow the same principles of segment size limitation.
I don't have a broad enough knowledge of individual equipment. Model number mean nothing to me and all of my routing and switching equipment is HP Procurve,...I don't use anything Cisco (in spite of my CCNA).
My single Procurve 5304XL L3 Switch (Router & Switch combined into one piece of hardware) can create 256 subnets all by itself. Although it doesn't have that many ports,..my particular model maxes out at a little less than 100 ports so I can create just under 100 subnets and keep each on a dedicated physical cable. I'm sure Cisco has a modular model of a similar physical design and capability.
Forget using a 10.4.0.0/16. You can really only use an IP Statement like that in the form of Superneting in a Routing Table over a backbone,...you cannot use that for a Host Segment,..it would be 65,534 Hosts. There is no way anyone can justify that many host on a single segment and there is no way it would ever run long before you ever got that high on the hosts.
The golden rule (whether anybody remembers it anymore) is "for every 200 Hosts create a new 24 bit segment. Smaller segments are ok as long as you don't go overboard with the idea, but you need to keep segments no larger than the typical 24 bit mask (254 host).
The primary debate comes from the fact that we now have 1gig and 10gig Ethernet speeds now and also have switching which eliminates collisions experienced by Hubs. However that only makes the issue less noticeable,...it doesn't make it go away. Since a 100mbps LANs still seems fast to "human perception" you have to overload a 1Gig network pretty heavy before it degrades below the performance of a 100mbps LAN and becomes "humanly" noticeable. But if you actually want your 1Gig LAN to actually fully perform like a 1Gig LAN (and not like a 100mpbs LAN) then follow the same principles of segment size limitation.
I don't have a broad enough knowledge of individual equipment. Model number mean nothing to me and all of my routing and switching equipment is HP Procurve,...I don't use anything Cisco (in spite of my CCNA).
My single Procurve 5304XL L3 Switch (Router & Switch combined into one piece of hardware) can create 256 subnets all by itself. Although it doesn't have that many ports,..my particular model maxes out at a little less than 100 ports so I can create just under 100 subnets and keep each on a dedicated physical cable. I'm sure Cisco has a modular model of a similar physical design and capability.
Forget using a 10.4.0.0/16. You can really only use an IP Statement like that in the form of Superneting in a Routing Table over a backbone,...you cannot use that for a Host Segment,..it would be 65,534 Hosts. There is no way anyone can justify that many host on a single segment and there is no way it would ever run long before you ever got that high on the hosts.
ASKER
I think I have a plan to help me in the mean time until we budget for new equipment. I do like the idea of a star topology, but as I said I didn't have enough ports on the 12Gs to do this. I do have two spare Cisco 3550-12Gs which I could connect to the current cisco 3550-12G switches to give me the extra ports I need. Doing this I would not have to daisy chain the 48 ports switches anymore and I could do a star topology. See below diagram. Does this look like it will work? Is the way I wired the 3550-12Gs correct? Thanks. 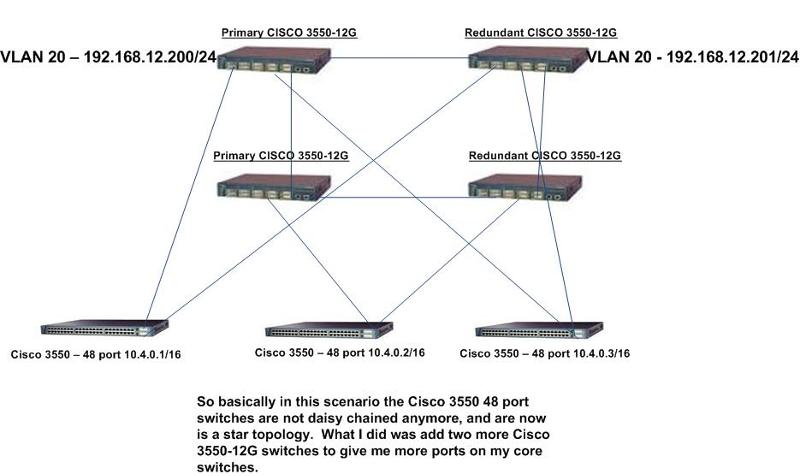
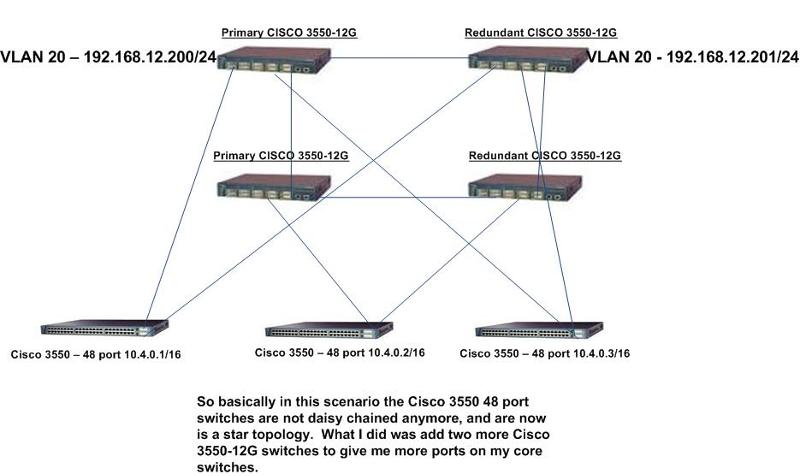
Actually that is a Switch Mesh. There's a lot of cabling overhead there,..I haven't personaly seen anyone do that anywhere that I have been. On top of that the topology descriptions generally are related to Routers and the Segments defined by them,...not really mentioned in ralation to Switches. Switch mainly are just "port expanders" comming off of each Router interface.
Maybe what you really want is something like below. It is a Hub & Spoke (or Star) design with three Segments giving a capacity of 762 IP Devices on the LAN total. The Switches in the diagram would be symbolic of either a Single Switch or a Switch Stack,...just depends on the number of Hosts.
http://phillipwindell.wordpress.com/2011/01/04/three-segment-lan-or-wan
3segmentlan.jpg
http://phillipwindell.wordpress.com
Maybe what you really want is something like below. It is a Hub & Spoke (or Star) design with three Segments giving a capacity of 762 IP Devices on the LAN total. The Switches in the diagram would be symbolic of either a Single Switch or a Switch Stack,...just depends on the number of Hosts.
http://phillipwindell.wordpress.com/2011/01/04/three-segment-lan-or-wan
3segmentlan.jpg
http://phillipwindell.wordpress.com
I assume you are suggesting that for redundancy sake. But that can be a bad thing,..It can cause to you maybe go for months with a bad link and never know it,..and hence never fix it. I like to know when something fails,...if I have a link fail I will know righ away,..therefore I can fix it right away. Too much redundancy can hide a problem until the problem grows to a Frankenstein Monster before you find out about it.
ASKER
What it looks like your proposing is router on a stick. My switching is completely layer3 so I don't want to go that route. This would mean that all traffic from all subnets would be going through one 10/100 router port, which would mean I wouldn't have a gigabit LAN anymore.
I need to have redundancy at the core switch level (3550-12G), because this is a requirement I have been given.
I need to have redundancy at the core switch level (3550-12G), because this is a requirement I have been given.
What it looks like your proposing is router on a stick.
What?? Where'd you get that idea?
That router has 3 separate interfaces! I don't know how you came up with "router on a stick".
redundancy at the core switch level
That just isjn't even possible without multiple Core Routers with multiple L3 paths.
My switching is completely layer3
That just is not even technologically possible. Layer3 is not even Switching at all,..and besides that it would require that every individual machine be on it's own subnet with a /30 bit network between itself and the Router it is "looking" at. Then you would loose exactly half of the addresses.
...unless you are just completely misusing terminology to the point that we might as well not even be speaking the same language.
What?? Where'd you get that idea?
That router has 3 separate interfaces! I don't know how you came up with "router on a stick".
redundancy at the core switch level
That just isjn't even possible without multiple Core Routers with multiple L3 paths.
My switching is completely layer3
That just is not even technologically possible. Layer3 is not even Switching at all,..and besides that it would require that every individual machine be on it's own subnet with a /30 bit network between itself and the Router it is "looking" at. Then you would loose exactly half of the addresses.
...unless you are just completely misusing terminology to the point that we might as well not even be speaking the same language.
Well you will just have to do whatever you want and hope for the best. I've said all I can say,...at this point I would only be repeated myself.
Ok,...maybe what you are talking about is this below. It is basically the same 3-segment LAN example but has 3 Routers in the Center. The diagram calls it a Private WAN,...but it can just as easily be Core Layer of a LAN. If you add another link between the two upper routers you would have a "Ring" design as ikalmar mentioned above (to give him credit). Doing that would only required 3 interfaces on each Router. This would provide redundancy just fine and would cover the loss of one link. It would also classify as a "Mess" because that is the full amount of links possible with a 3 router arraingment.
classify as a "Mess" because
Mesh,...not Mess
Mesh,...not Mess
i suppose that the switches are all in a CED room, so you can stack 4 3550 12G connecting them trought ethercannel links.
etherchannel is a link agregation technique that allow you to combine multiple links togheter so you can have more uplink bandwidth.
if you don't want to decrease bandwidth use the gbic modules to connect switches trou optical fiber.
in my experience i noticed that allso if it said to run at 1 gbps like other ports it works better for trunks and moreover you don't waste rj45 ports.
wich kind of switches do you use ffor access level?
etherchannel is a link agregation technique that allow you to combine multiple links togheter so you can have more uplink bandwidth.
if you don't want to decrease bandwidth use the gbic modules to connect switches trou optical fiber.
in my experience i noticed that allso if it said to run at 1 gbps like other ports it works better for trunks and moreover you don't waste rj45 ports.
wich kind of switches do you use ffor access level?
ASKER
Right now I do have a multi-segment LAN using layer 3 switches and not a router. This is currently in production and working fine. Let me explain.
Each LAN switch has two route statements: (when I say LAN switch I am referring to the 3550 48 ports switches) Below are the route statements all LAN switches have
ip route 0.0.0.0 0.0.0.0 192.168.12.200 (Primary 3550-12G_
ip route 0.0.0.0 0.0.0.0 192.168.12.201 10 (Secondary 3550-12G)
I have the following subnets configured on my network. Each subnet serves a different purpose.
10.9.1.0/24 - Which is on a cisco 3550 (One GBIC connects to Primary 3550-12G and other GBIC connects to the secondary 3550-12G.
10.10.1.0/24 - This network is also on a cisco 3550 48 port switch (One GBIC connects to the Primary 3550-12G and the other connects to the secondary 3550-12G
10.50.1.1/24 - This network is also on a cisco 3550 48 port switch (one GBIC connects to the Primary 3550-12G and the other GBIC connects to the secondary 3550-12G
10.4.0.0/16 - This network spreads across a couple switches. Right now the 10.4.0.0 network has two switches. the two switches are connected together via fiber, then go to the core switches.
When I say the core switches are redundant I am talking about the 3550-12Gs. I can shut down the primary and the secondary takes over. This does work and has been tested. This works because each LAN switch has two route statements. I also have VTP configured on all these switches.
Sorry for any miscommunication earlier.
Each LAN switch has two route statements: (when I say LAN switch I am referring to the 3550 48 ports switches) Below are the route statements all LAN switches have
ip route 0.0.0.0 0.0.0.0 192.168.12.200 (Primary 3550-12G_
ip route 0.0.0.0 0.0.0.0 192.168.12.201 10 (Secondary 3550-12G)
I have the following subnets configured on my network. Each subnet serves a different purpose.
10.9.1.0/24 - Which is on a cisco 3550 (One GBIC connects to Primary 3550-12G and other GBIC connects to the secondary 3550-12G.
10.10.1.0/24 - This network is also on a cisco 3550 48 port switch (One GBIC connects to the Primary 3550-12G and the other connects to the secondary 3550-12G
10.50.1.1/24 - This network is also on a cisco 3550 48 port switch (one GBIC connects to the Primary 3550-12G and the other GBIC connects to the secondary 3550-12G
10.4.0.0/16 - This network spreads across a couple switches. Right now the 10.4.0.0 network has two switches. the two switches are connected together via fiber, then go to the core switches.
When I say the core switches are redundant I am talking about the 3550-12Gs. I can shut down the primary and the secondary takes over. This does work and has been tested. This works because each LAN switch has two route statements. I also have VTP configured on all these switches.
Sorry for any miscommunication earlier.
ASKER
Anyway, we got way off topic. pwindell you did answer my original question about how many switches I can daisy chain together, so I will award the points to you. Thanks.
ASKER
Thanks
The other guys made good comments too. Maybe you should split the points. I'm not that worried about point for myself, I just wish I could have done better with the question, but it was hard for me to follow what everything really was.
But if you have more than 100-200 users on a LAN segment, you may want to consider splitting them up with a router.