BMI-IT
asked on
Exchange 2010 loosing diskspace on system drive
Hi.
We are running exchange 2010 - SP1 under 2008 R2. We are finding that something is filling up the system drive (c:) causing the system to shutdown due to back pressure.
For example, yesterday we had 13Gb free, I come in this morning and Find that I have 2Gb Free on the system drive!. The mail-stores are kept on another drive and are backing up just fine and clearing the mail-store logs So the problem is the system drive.
I have cleared out the \inetpub\logs\LogFiles\W3S
What else could cause 10Gb of space to be filled over night?
We are running exchange 2010 - SP1 under 2008 R2. We are finding that something is filling up the system drive (c:) causing the system to shutdown due to back pressure.
For example, yesterday we had 13Gb free, I come in this morning and Find that I have 2Gb Free on the system drive!. The mail-stores are kept on another drive and are backing up just fine and clearing the mail-store logs So the problem is the system drive.
I have cleared out the \inetpub\logs\LogFiles\W3S
What else could cause 10Gb of space to be filled over night?
also download "treesize free" and scan the c drive to see what is being used up. WSUS springs to mind for updates
ASKER
I have removed the inetpub\logs\LogFiles\W3SV
any other ideas?
any other ideas?
a colleague of mine who posts on here ( pete long ) wrote this on back pressure.
http://www.petenetlive.com/KB/Article/0000165.htm
http://www.petenetlive.com/KB/Article/0000165.htm
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
nothing on shadow copies, I experienced my first back-pressure issue yesterday and fixed that to get mail flowing.
Installed treesize free and found some older logs, moved away, thank you for that Tip. I am back at 14Gb free on the system drive so I will continue to monitor it for the next day then report back
Installed treesize free and found some older logs, moved away, thank you for that Tip. I am back at 14Gb free on the system drive so I will continue to monitor it for the next day then report back
ASKER
well so far after some cleaning of the system drive I stabilized it at 11.6 GB. How ever 4 Hours later I am down to 11.2GB, I also found a couple of big HDMP files located here
C:\Windows\ServiceProfiles
Am I correct that I can just remove these files?
This is turning into an obsession:)
C:\Windows\ServiceProfiles
Am I correct that I can just remove these files?
This is turning into an obsession:)
ASKER
Good Day,
just an update. after running more backups last night I got the free space down to 25Gb on the system drive, However upon checking again 11 hours later I am down to 16GB Free.
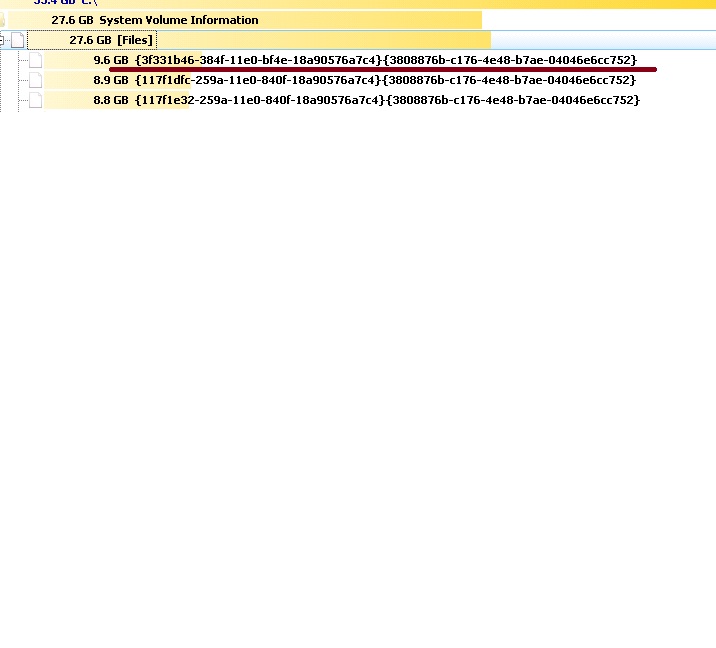
using treesize and comparing screen shoots of free data, I found the area under the system volume are bring filled up (see attached screen - underlined) This data file was newly created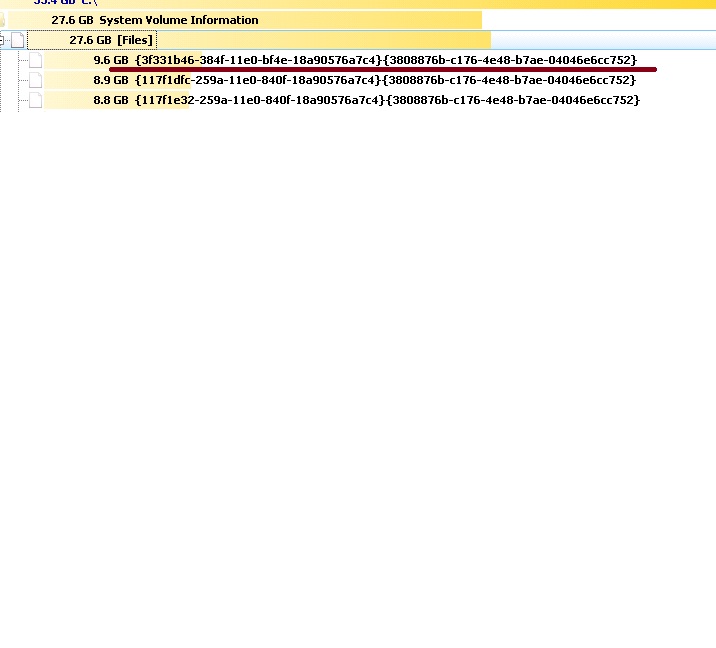
Has any one got any idea?
this is a stand alone server, the mailstores are on another drive, the ISS logs are saved elsewhere. I am really at a loss at why I'm loosing space at such an alarming rate
just an update. after running more backups last night I got the free space down to 25Gb on the system drive, However upon checking again 11 hours later I am down to 16GB Free.
using treesize and comparing screen shoots of free data, I found the area under the system volume are bring filled up (see attached screen - underlined) This data file was newly created
Has any one got any idea?
this is a stand alone server, the mailstores are on another drive, the ISS logs are saved elsewhere. I am really at a loss at why I'm loosing space at such an alarming rate
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
shadow copies.. shadows were disabled in the services but I checked the control panel for it and saw that the 3 instances of the offending files matched what was in the system volume. i confirmed it with the command "vssadmin list shadows"
I checked the settings and reduced the space needed down to 300mb and saved it and the offending files went away. I am back to 43GB Free
The question is: Do I need to use shadow copies and why if it was disabled in the services and in the control applet what was it still running! This is a mystery, i knew it was disabled but why would it be making copies???
I checked the settings and reduced the space needed down to 300mb and saved it and the offending files went away. I am back to 43GB Free
The question is: Do I need to use shadow copies and why if it was disabled in the services and in the control applet what was it still running! This is a mystery, i knew it was disabled but why would it be making copies???
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
Secondly, did you get a succesfull backup last night? if not the logs will not have been cleared.