alpineman331
asked on
Router Settings
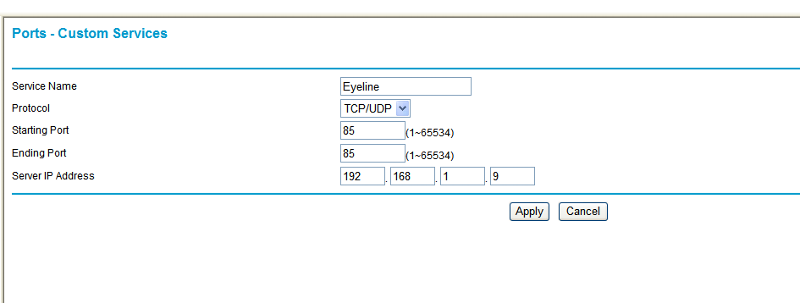
I have a surveillance program which displays images from a security camera. I used to be able to access/view the camera from online but since I switched routers I can't seem to get it to work. I contacted support from the company who wrote the surveillance program and they told me I needed to configure my router for "TCP\IP port forwarding from public port 85 to 192.168.1.9 port 85". So I tried but no such luck. Attached is a pic of my router settings. I am no networking expert... how should this be set up? 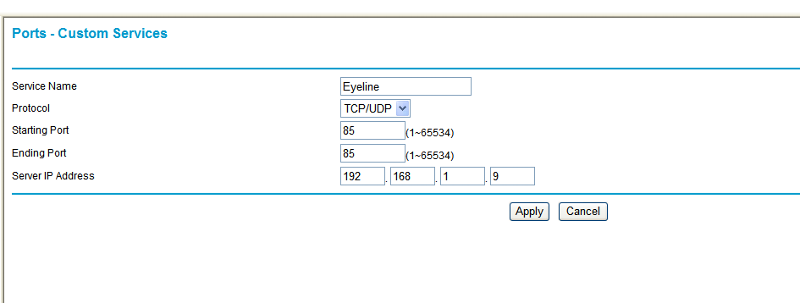
Your new router may also include a build in firewall that by default blocks all incoming connections. If that is the case, you need to configure that separately to allow port 85 to pass to 192.168.1.9
ASKER
Yes, that address works just from for LAN access, but for WAN access the support told me to access:
http://75.158.200.151:85
That address used to work for WAN access but now it just says "server not responding". The software does allow for configuration of this address, but I have no clue what address I should put in if not this one?
http://75.158.200.151:85
That address used to work for WAN access but now it just says "server not responding". The software does allow for configuration of this address, but I have no clue what address I should put in if not this one?
Are you sure 75.158.200.151 is still your WAN address? If your ISP assigns dynamic addresses, then changing router hardware most probably also changes your IP-address.
ASKER
Hmm... this may sound stupid, but how to I tell what my WAN address is?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Ah... so I know I said I'm not a networking expert but I should have thought of that! At any rate, you were right. My ISP changed my WAN address.
Thanks for everyones help!
Thanks for everyones help!
http://192.168.1.9:85
or
https://192.168.1.9:85
That should work, also make sure you use internet explorer for a test.