AXISHK
asked on
Comment font size for Word 2011
How to change the bubble font size for Word 2011 as it is too small to see the change ?
Thanks
Thanks
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Can you dump the screen for my reference ? I couldn't manage how it in my Word Window 2010.
Tks
Tks
So the 2011 above was a typo, and you are using Word 2010? That makes things easier (for me :))
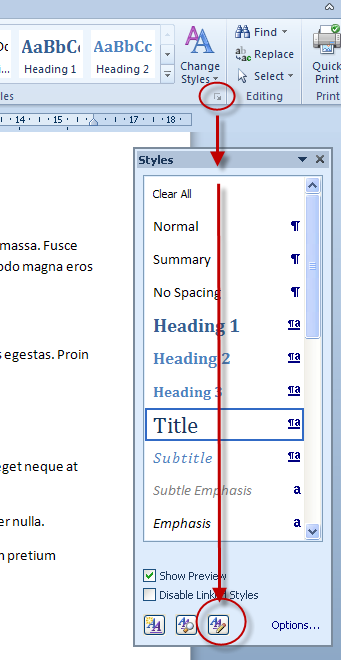
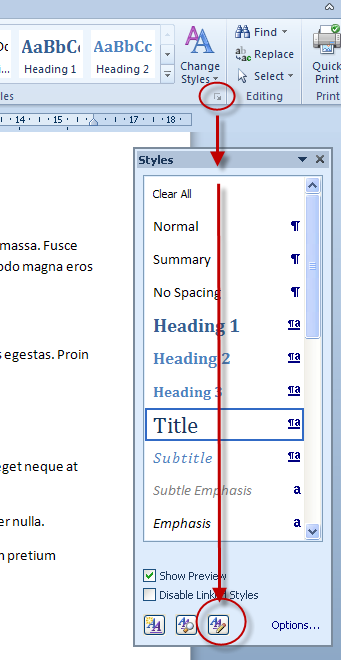
Click the lower right hand corner of the Styles group in the Home ribbon to open up the Styles pane. Click the button at the bottom of the Styles pane to Manage styles
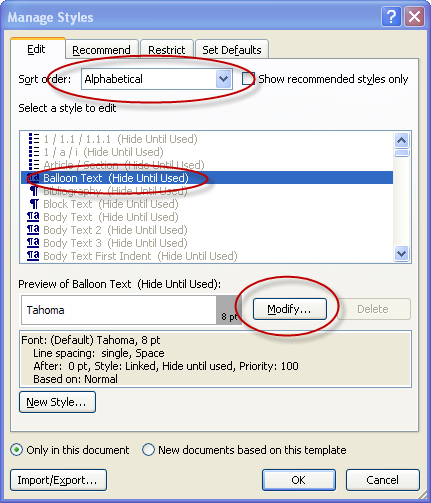
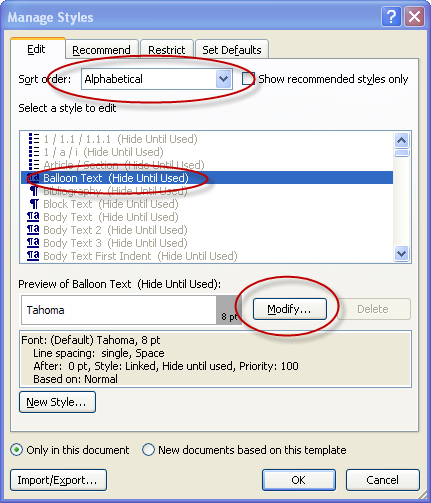
In the Manage Styles box, select Alphabetical from the first drop-down, so you can easily find the Balloon Text style. Select it and click the Modify button to make changes to the style.
In the next dialog, Modify Style, select a different font size, then close all dialogs.
cheers, teylyn
Click the lower right hand corner of the Styles group in the Home ribbon to open up the Styles pane. Click the button at the bottom of the Styles pane to Manage styles
In the Manage Styles box, select Alphabetical from the first drop-down, so you can easily find the Balloon Text style. Select it and click the Modify button to make changes to the style.
In the next dialog, Modify Style, select a different font size, then close all dialogs.
cheers, teylyn
ASKER
However, it doesn't work.