triphen
asked on
VB 6 Calendar not showing
Hello Experts,
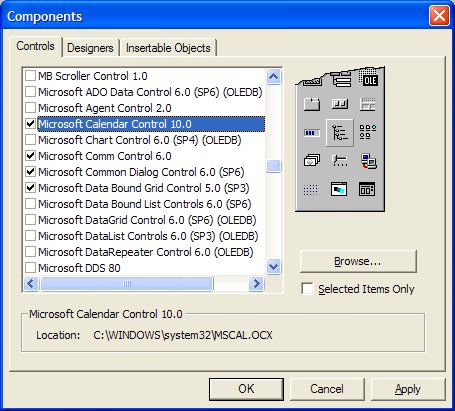
In my application I have the ability to select a date range. On My PC with Vb this works fine, but after I compile and test on another PC the calendar doesn't show correctly. See attached image. I am using MSCAL.ocx. this file is in the sytem32 folder of the Test PC.
Any ideas?
mscal.png
calendar.png
In my application I have the ability to select a date range. On My PC with Vb this works fine, but after I compile and test on another PC the calendar doesn't show correctly. See attached image. I am using MSCAL.ocx. this file is in the sytem32 folder of the Test PC.
Any ideas?
mscal.png
calendar.png
Have you installed Service Pack 6 for your VB6? I ask because my calendar control, which works equally well with XP or Win7, is version 10. Yours is version 8. Try updating to SP6, or at least get the latest available MSCAL.OCX. 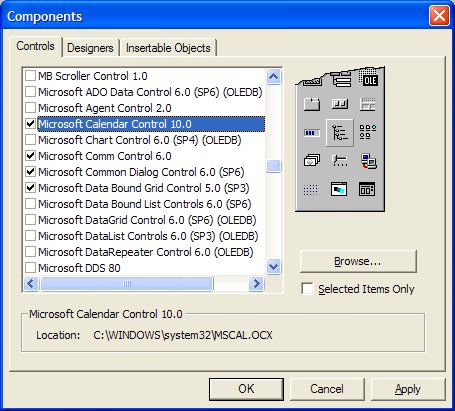
ASKER
Thanx for your quick response.
Attached is the version I am using. Is it the same as yours?
can you send me your MSCAL.ocx?
vb6sersion.png
Attached is the version I am using. Is it the same as yours?
can you send me your MSCAL.ocx?
vb6sersion.png
No, mine is much more recent. MSCAL.OCX may have dependencies contained within the SP6 service pack. Why not just go to Microsoft's web site and download/install SP6?
Image1.jpg
Image1.jpg
ASKER
I did download and isntall but something seems to be wrong. The version didnt update? Ill try again. Thanx!
ASKER
Damned thing wont work. When I execute the SP.exe a windows appears for a split second and disappears. That's it. Nothing is updated in VB. Maybe because of Win 7? I even tried Run as Administrator.
I'm sure it's Win7 that's preventing the install. Win7 is very picky about writing stuff to the Program Files folder, under which VB6 is located. Here is a link that tells how to install VB6 on Win7. Do all the stuff it says, but run the service pack update instead of installing VB6:
http://www.fortypoundhead.com/showcontent.asp?artid=20502
http://www.fortypoundhead.com/showcontent.asp?artid=20502
Also, in the link I posted, scroll down through the user comments. Some of them describe other people's experience with installing SP6 on Win7...
ASKER
Ok I found another link to SP6 that was 26MB vs 2MB. That one worked :)
I am on the same build as you are. But my Calendar is still v8. Can you send me your MSCAL.ocx?
I am on the same build as you are. But my Calendar is still v8. Can you send me your MSCAL.ocx?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.