Moving messages sent from a second mailbox, into that accounts sent items
I have a shared mailbox that 3 users use as an additional mailbox on their outlook 2010.
They all have 'send as' permissions on this mailbox and this is working as expected.
One of the users would like the email he 'send as'-es to go into the sent items folder of this additional mailbox, currently it goes into his own mailbox's 'sent items'
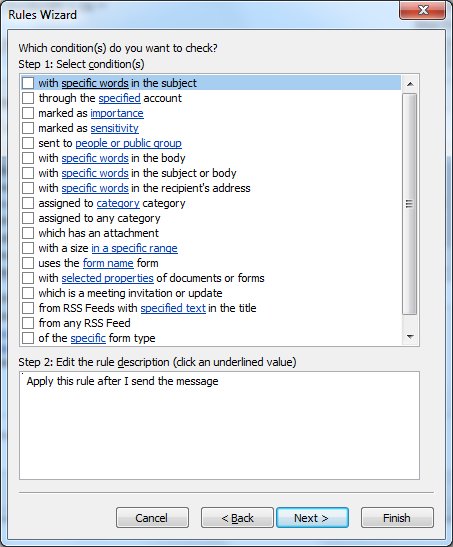
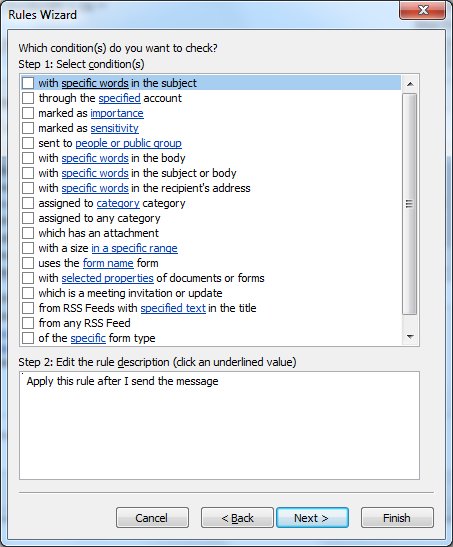
I assumed a rule could handle this but there is no rule to check for messages 'from' a specific person or mailbox using the 'apply this rule after I send the message' option
They all have 'send as' permissions on this mailbox and this is working as expected.
One of the users would like the email he 'send as'-es to go into the sent items folder of this additional mailbox, currently it goes into his own mailbox's 'sent items'
I assumed a rule could handle this but there is no rule to check for messages 'from' a specific person or mailbox using the 'apply this rule after I send the message' option
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
Well that's great news. So just setup the other accounts as full exchange accounts in the same profile and then when you open outlook up, you will have to provide the relevant credentials for the shared account, but the problem of the Sent Items will be no more.
The Previous versions outlook had some issue regarding this , but was corrected in OL2010 , From now on when a user sends a mail using his additional account , the mails will be present in Sent items in the additional account
ASKER