Report - Summing issue
Experts, I have this report that is in development. (rptFacilAvail2)
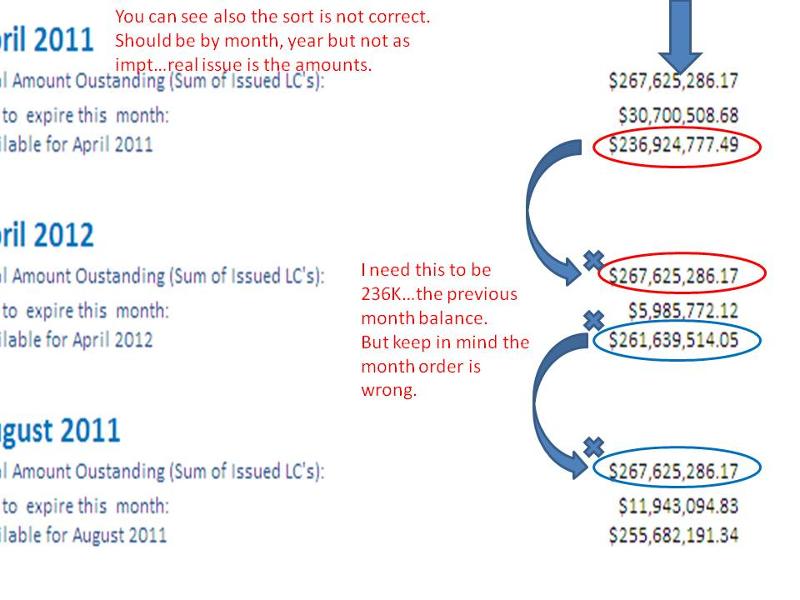
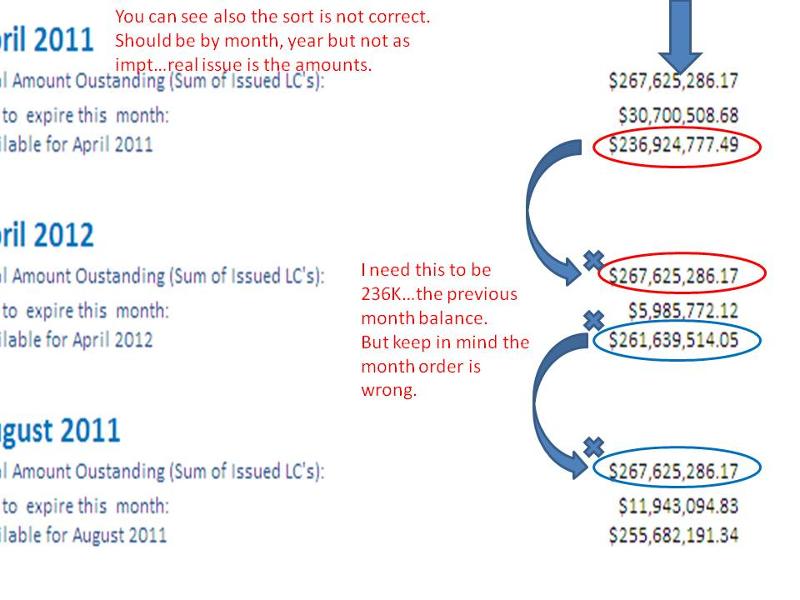
What I need is a sum of Available Per Month.
You can see from the pic that I am not getting the correct balance based on the previous month.
I think you can see from the pic what the issue is instead of trying to explain by words.
Need some advice on how to do this trick. (You can also see that the month order is not correct)
thank you
I attached the db.
 EE-report.zip
EE-report.zip
What I need is a sum of Available Per Month.
You can see from the pic that I am not getting the correct balance based on the previous month.
I think you can see from the pic what the issue is instead of trying to explain by words.
Need some advice on how to do this trick. (You can also see that the month order is not correct)
thank you
I attached the db.
 EE-report.zip
EE-report.zip
ASKER
Ok. Thanks. Not at computer and might not be for some time.
ASKER
Cap, is it possible to group those months together? Please see attachment. Thank you.
Presentation1.jpg
Presentation1.jpg
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Thank you. I see how you fixed it. Really appreciate it. I will ask another question about this.
EE-report.accdb