Blackberry services logons
I was working on the server (SBS DC) and logon under the different Admin acount. BB services associated under another account and did not start. So communications with BES server and BB do not receive emails.
If I change loon as local account the services will start. Would that work? Or soes it need only that BB account?
If I change loon as local account the services will start. Would that work? Or soes it need only that BB account?
ASKER
The thing is I wasn't working on BES server. I was working on SBS DC server that obviously communicating to BES server.
The Blackberry services did not start because they were under a different admin account. If change them to local they do start but the problem remains. No messages on BB..
The Blackberry services did not start because they were under a different admin account. If change them to local they do start but the problem remains. No messages on BB..
Is that the only DC available to the BES server?
ASKER
yes
OK, then first thing is to make sure that DC is up and functioning properly. Then log onto the BES server as the AD service account, besadmin, etc., and make sure the services start up properly running as the service account.
Running the BES services as the local system account will not work because that local system account will not have any permissions to the users' mailboxes.
Running the BES services as the local system account will not work because that local system account will not have any permissions to the users' mailboxes.
ASKER
On the BES server Blackberry accouts working as Local Profile logons. I did not touch BES, it seems to be working fine.
I'm not sure I understand what you mean by "local profile logons". Also, just because the services are running doesn't mean that the BES is working properly. If Blackberry devices are not receiving messages then there is a problem with the BES server, the email server, communication between those two, or communication between the BES server and RIM.
If everything appears to be running as it should be then you may need to contact RIM support, 877-255-2377.
If everything appears to be running as it should be then you may need to contact RIM support, 877-255-2377.
ASKER
Local System Account logon under services.. So in BES it is Local and in DC SBS its under the Domain Admin account.
ASKER
Yes on Domain Controller and BES server. I understand this is some kind of weird and abnormal setup.
Yes, I have never heard of Blackberry services running on a domain controller. Which services are on the DC and which services are on the BES server?
ASKER
Oops sorry. This is the same server. Bouncing the server helped. Yes, its all running on SBS DC. So changing the logins and rebooting server solved the problem.
Weird thing, was some services ran under the besadmin, and others under different domain admin account. BB Alert for example. do you know what that service for?
Weird thing, was some services ran under the besadmin, and others under different domain admin account. BB Alert for example. do you know what that service for?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Got it. Thank you!!
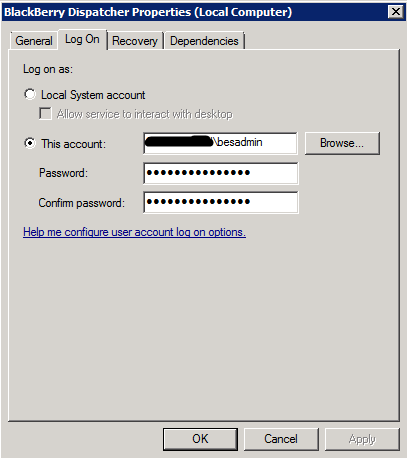
Make sure you log onto the server as besadmin, or whatever the BES service account is, and make sure the services start up.