php sessions not being read so setting a new one when not needed.
I have a page that is setting up session variables does various things and then posts back a form. The problem being that after the post back it sets up a new session for some reason and then my session information is being lost.
I am running php 5.3.5 and apache 2.2.8.
This is from the ini file,
session.use_cookies = 1
session.use_only_cookies = 1
session.name = PHPSESSID
session.auto_start = 0
session.cookie_lifetime = 0
The session files are being written and have the correct information in them for what has been set to the session variables for each run through but there is no carry over.
I checked the session_id() and it is different.
I am running php 5.3.5 and apache 2.2.8.
This is from the ini file,
session.use_cookies = 1
session.use_only_cookies = 1
session.name = PHPSESSID
session.auto_start = 0
session.cookie_lifetime = 0
The session files are being written and have the correct information in them for what has been set to the session variables for each run through but there is no carry over.
I checked the session_id() and it is different.
please post an example of the code
From your question above, i think whats happening is the following
page 1:
$_SESSION['test'] = $_POST['test'];
then u go to a page2 then return to the page1? if this is the cases then nothing is being posted again so it will set the variable to nothing
From your question above, i think whats happening is the following
page 1:
$_SESSION['test'] = $_POST['test'];
then u go to a page2 then return to the page1? if this is the cases then nothing is being posted again so it will set the variable to nothing
ASKER
session_start() is on the page, it reposts back to itself, and things do get set, its just that for some reason once I come back after the submit, it starts a new session.
$decrypt is a variable used later on in the code, the $_GET comes from a different page entirely with a value that I need, so I get it the first time I come to the page, then set it into a session variable, then from then on I check to see if there is any get value, if not I look for the session variable, the problem being that for some reason it does not pick up the session that was set before and I end up with no session variable by that name and my variable comes up with no value.
This is all on one server so there is no problems with that.
I don't unset anything on the entire page besides some com objects so I am not accidentally unsetting my session variables
$decrypt is a variable used later on in the code, the $_GET comes from a different page entirely with a value that I need, so I get it the first time I come to the page, then set it into a session variable, then from then on I check to see if there is any get value, if not I look for the session variable, the problem being that for some reason it does not pick up the session that was set before and I end up with no session variable by that name and my variable comes up with no value.
This is all on one server so there is no problems with that.
I don't unset anything on the entire page besides some com objects so I am not accidentally unsetting my session variables
if(!empty($_GET["userId"]))
{
$decrypt = $_GET['userId'];
$_SESSION['username']=$decrypt;
}
else
{
$decrypt=$_SESSION['username'];
}ASKER
As an update cookie setting works so that is not the problem.
For some reason it seems like the PHPSESSID cookie is being reset every time I call session_start().
If I manage to somehow save the original session_id I can then force the session_id to whatever the first session_id was and then the sessions work and I can access my stored session data.
Any one have any idea what could be triggering the PHPSESSID cookie overwrite after every session_start() call?
For some reason it seems like the PHPSESSID cookie is being reset every time I call session_start().
If I manage to somehow save the original session_id I can then force the session_id to whatever the first session_id was and then the sessions work and I can access my stored session data.
Any one have any idea what could be triggering the PHPSESSID cookie overwrite after every session_start() call?
haloexpertsexchange:
I had some issues awhile back with a hsosting setup where I had to explicitly register each session variable, and wrote this function for convenience.
/*************************
' Set the value of the session variable passed.
'
' function
' setSessionVariable
' (
' $SessionVariableName
' $SessionVariableValue
' )
'*************************
function
setSessionVariable($Sessio
{
global $HTTP_SESSION_VARS;
/*************************
'
' If the session variable not registered, then register it prior to
' setting its value.
'
'*************************
if (session_is_registered($Se
{
session_register($SessionV
}
$HTTP_SESSION_VARS[$Sessio
}
Your host probably uses the newer $_SESSION global in place of the older $HTTP_SESSION_VARS, or maybe it doesn't.
AielloJ
I had some issues awhile back with a hsosting setup where I had to explicitly register each session variable, and wrote this function for convenience.
/*************************
' Set the value of the session variable passed.
'
' function
' setSessionVariable
' (
' $SessionVariableName
' $SessionVariableValue
' )
'*************************
function
setSessionVariable($Sessio
{
global $HTTP_SESSION_VARS;
/*************************
'
' If the session variable not registered, then register it prior to
' setting its value.
'
'*************************
if (session_is_registered($Se
{
session_register($SessionV
}
$HTTP_SESSION_VARS[$Sessio
}
Your host probably uses the newer $_SESSION global in place of the older $HTTP_SESSION_VARS, or maybe it doesn't.
AielloJ
ASKER
AielloJ:
I have more or less complete control over the server settings and the php settings so I should be able to change any sort of settings which would control this. Any idea what exactly I should check into to see if my problem is like yours?
I have more or less complete control over the server settings and the php settings so I should be able to change any sort of settings which would control this. Any idea what exactly I should check into to see if my problem is like yours?
haloexpertsexchange:
Try the code I provided or similar in-line code to see if it resolves the issue. I had similar issues with PHP and session variables. That's why I wrote that function long ago and use it still today - it works for me. Like you, I was having a very similar issue and after some digging that function resolved it.
I don't have control of the PHP settings as my sites are hosted with an Internet company. I don't know what settings may be involved if it is related to the settings.
AielloJ
Try the code I provided or similar in-line code to see if it resolves the issue. I had similar issues with PHP and session variables. That's why I wrote that function long ago and use it still today - it works for me. Like you, I was having a very similar issue and after some digging that function resolved it.
I don't have control of the PHP settings as my sites are hosted with an Internet company. I don't know what settings may be involved if it is related to the settings.
AielloJ
ASKER
AielloJ:
I added this to my code
I added this to my code
function
setSessionVariable($SessionVariableName, $SessionVariableValue)
{
global $_SESSION;
/**********************************************************************
'
' If the session variable not registered, then register it prior to
' setting its value.
'
'*********************************************************************/
if (session_is_registered($SessionVariableName))
{
session_register($SessionVariableName);
}
$_SESSION[$SessionVariableName] = $SessionVariableValue;
}if(!empty($_GET["userId"]))
{
$decrypt =$_GET["userId"];
setSessionVariable('username', $decrypt);
echo session_id();
}
else
{
$decrypt=$_SESSION["username"];
}
haloexpertsexchange:
Let's go back to some basics 'cause somethings not right.
1) Are you certain the PHP interpreter is running?
2) Have you run php_info() and looked at the output it produces?
3) Is your interpreter using the $_SESSION variables or the older $HTTP_SESSION_VARS syntax?
4) Is the session_start() function at the top of EVERY page?
5) What is the register_globals set to in your php.ini file?
6) Is there a $GLOBALS[] supglobal array defined. Did you use print_r() or other function that displays the contents of associative arrays to list its contents?
Let's go back to some basics 'cause somethings not right.
1) Are you certain the PHP interpreter is running?
2) Have you run php_info() and looked at the output it produces?
3) Is your interpreter using the $_SESSION variables or the older $HTTP_SESSION_VARS syntax?
4) Is the session_start() function at the top of EVERY page?
5) What is the register_globals set to in your php.ini file?
6) Is there a $GLOBALS[] supglobal array defined. Did you use print_r() or other function that displays the contents of associative arrays to list its contents?
Are you running this on a Windows platform? I've seen cases where the php.ini file had to be in the php instalation directory as well as the Windows directory.
ASKER
AielloJ:
1) that would be a yes, everything else is working besides the session variable issue.
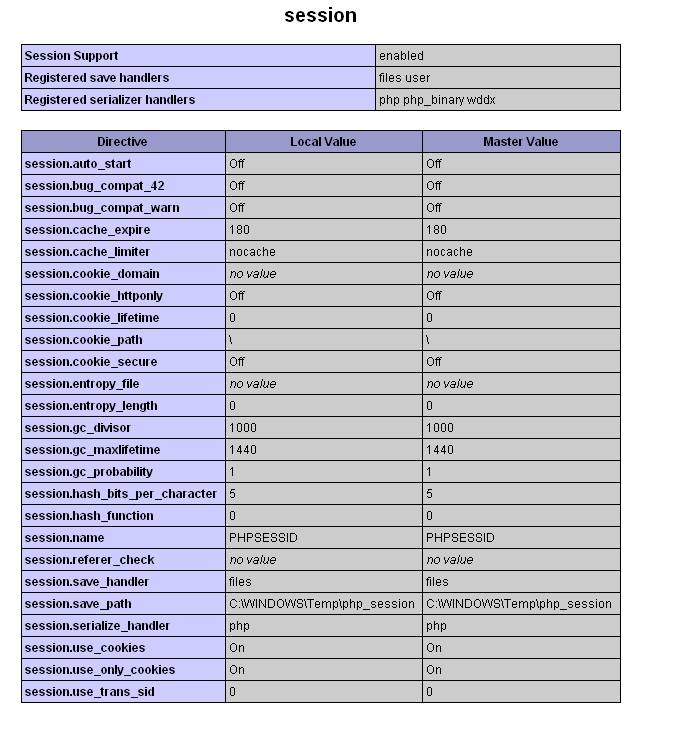
2)This is what php info shows about sessions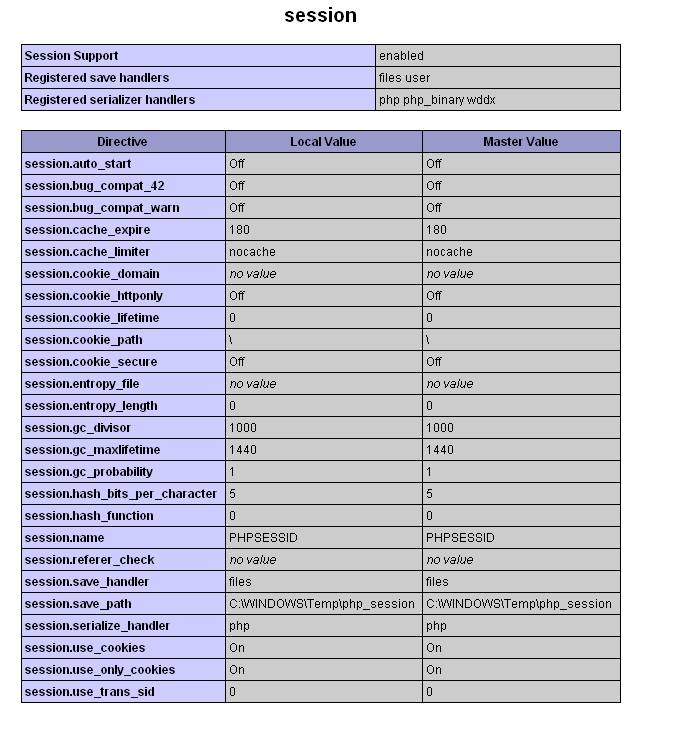 3)it uses $_SESSION, $HTTP_SESSION_VARS is a deprecated function and I am running 5.3.5
3)it uses $_SESSION, $HTTP_SESSION_VARS is a deprecated function and I am running 5.3.5
4)My current problem only is ever on one page which posts back information to itself and then somehow loses the session, but yes session_start is a the top of the page.
5)register_globals is off as is the default value for 5.3.5
6)I have not done anything with a $GLOBALS[] array. I have used print_r on my sessions which is why I knew that my session was getting lost and that it was not just a matter of me some how setting the session to a blank value.
I am running on a windows server off of apache. It says that the loaded ini file is the one in the php directory but it wouldn't hurt for me to put an ini file in the Windows directory as well.
1) that would be a yes, everything else is working besides the session variable issue.
2)This is what php info shows about sessions
 3)it uses $_SESSION, $HTTP_SESSION_VARS is a deprecated function and I am running 5.3.5
3)it uses $_SESSION, $HTTP_SESSION_VARS is a deprecated function and I am running 5.3.54)My current problem only is ever on one page which posts back information to itself and then somehow loses the session, but yes session_start is a the top of the page.
5)register_globals is off as is the default value for 5.3.5
6)I have not done anything with a $GLOBALS[] array. I have used print_r on my sessions which is why I knew that my session was getting lost and that it was not just a matter of me some how setting the session to a blank value.
I am running on a windows server off of apache. It says that the loaded ini file is the one in the php directory but it wouldn't hurt for me to put an ini file in the Windows directory as well.
haloexpertsexchange:
I've had to put my php.ini file in both. I don't remember the problem I was having, but I definitely had to put it in both folders. Maybe you could send me a very stripped down copy of the page for me to test.
I've had to put my php.ini file in both. I don't remember the problem I was having, but I definitely had to put it in both folders. Maybe you could send me a very stripped down copy of the page for me to test.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
haloexpertsexchange:
That would be it. Apache always uses Unix path conventions, even when runnng on Windows platforms.
AielloJ
That would be it. Apache always uses Unix path conventions, even when runnng on Windows platforms.
AielloJ
ASKER
I figured out my problem by comparing the ini file from a working php installation on apache with the ini file from the one that I was having problems with and figured out my problem that way.
Are you remembering to include the session_start() function at the top of your pages? It must be the first line in the script file.