Noduzz
asked on
Static Routing with VLANS
I am having an issue with a static route i am trying to add to my network. To give you a little background the network is like this:
It's pretty small. We have a firewall and router and the router has 5 vlans. The firewall interface that is on the lan is in the 10.0.1.x VLAN which is also where the IP that i am trying to route traffic from the other VLANs to. So, basically lets say the ip of the firewall LAN interface is 10.0.1.254 and the ip that i want to route traffic to is 10.0.1.253 and i am trying to send traffic from the 10.0.2.x, 10.0.3.x, 10.0.4.x, etc VLANs. The static route was added to the firewall and the 10.0.1.x network can send traffic to the new route but the other VLANs still cannot. Now when i try to add the static route (192.168.1.x 255.255.255.0 to 10.0.1.253) to the router it doesnt work. This is for MPLS traffic if that helps at all. Anyone have any advice on this?
It's pretty small. We have a firewall and router and the router has 5 vlans. The firewall interface that is on the lan is in the 10.0.1.x VLAN which is also where the IP that i am trying to route traffic from the other VLANs to. So, basically lets say the ip of the firewall LAN interface is 10.0.1.254 and the ip that i want to route traffic to is 10.0.1.253 and i am trying to send traffic from the 10.0.2.x, 10.0.3.x, 10.0.4.x, etc VLANs. The static route was added to the firewall and the 10.0.1.x network can send traffic to the new route but the other VLANs still cannot. Now when i try to add the static route (192.168.1.x 255.255.255.0 to 10.0.1.253) to the router it doesnt work. This is for MPLS traffic if that helps at all. Anyone have any advice on this?
Every router in the path, end to end will need to have routes added, this includes the ISP MPLS routers. Additionally, routes will need to be added on all routers in your control as both ends need to be aware of each other.
Billy
Billy
Just to add on to rfc's comment. This is the downside of static routing. To much administrative overhead.
ASKER
Looks like you have some assymetrical routing occuring and could be causing the issues you are seeing as you have 2 different paths going to the MPLS router; so please explain the 2 exit points 10.0.1.254 and 10.0.1.253, what is the purpose for this design? You have a very poor diagram that still needs to be explained as it does not make sense.
Billy
Billy
ASKER
The 2 different paths are: one for internet and the other for MPLS. That is what the ISP instructed we do. The path for the internet goes through our firewall and the path to MPLS comes straight from our network. As per the ISP's request. Sorry for the diagram being poor but i am bombarded with other things right now, we just moved offices, and are dealing with other issues as well.
ASKER
So i just noticed something, on the core switch there is another static route that is:
network 0.0.0.0 mask 0.0.0.0 10.0.1.254 which has the same metric and distance as the router i added. Do i need to change the metric on it?
network 0.0.0.0 mask 0.0.0.0 10.0.1.254 which has the same metric and distance as the router i added. Do i need to change the metric on it?
10.0.1.254 looks to be the gateway to your internet? if that is so and you remove that default route you will lose internet connection. I am still a little unclear about what you are trying to route. Are you trying to route the other networks over the MPLS?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
The ISP incorrectly configured their router. Therefore the answer was not answered by EE.
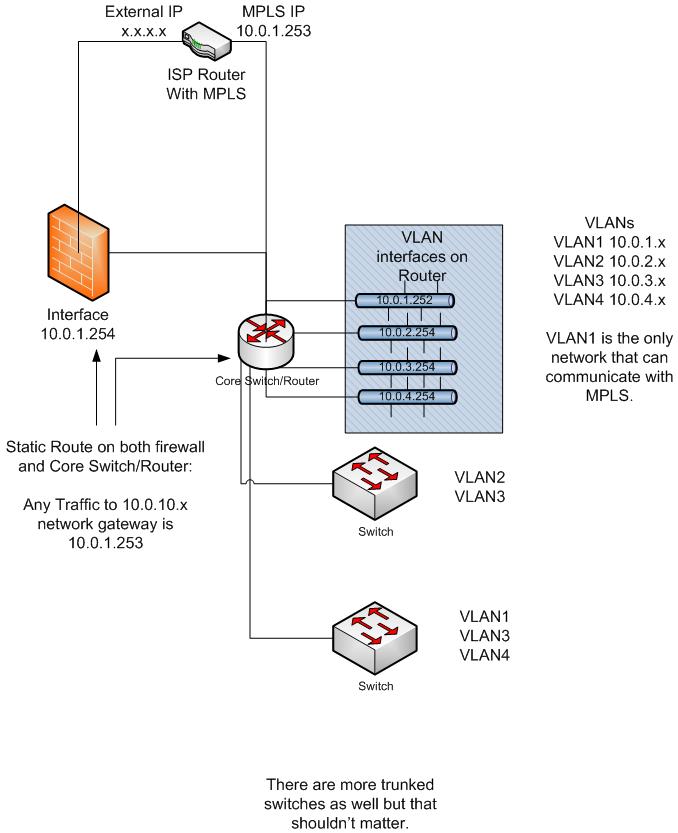
Could yo provide a network diagram indicating where the different networks are located and also provide the routing configuration you are trying to implement.