How do I import a CSV file into a specific Contact Group in Outlook 2010?
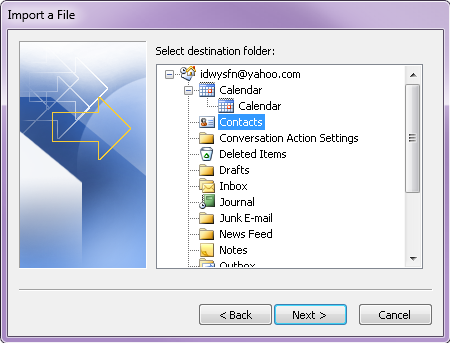
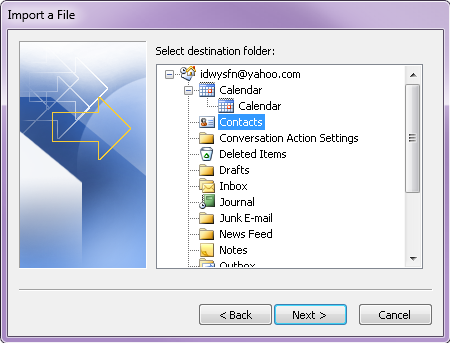
I am running Outlook 2010. I have created a contact group inside my main contacts folder. I want to import a csv file directly into that specific contact group. I go through the import process (File>Open>Import...) and when it asks me what the destination folder is, I can only choose the contacts folder, not a specific contact group within the contacts folder. Is there any way to import a csv file directly into the contact group? I don't want to import my list into the contacts folder and have to sort through them into the contact group afterwards. That would be quite time-consuming. Thank you!
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
Sorry about that... I should've read more carefully to get you the Outlook 2010 instructions. Thank you for accepting my resolution in light of my oversight.
ASKER
Thank you for the help! I had a client who was looking to me to provide a solution and I couldn't find anything on the web offering the solution like you did. You saved me tons of time and gave me a happy client!
ASKER