Maverickgoose
asked on
Unable to ping/telnet Remote Cisco ASA 5510
Hi,
I have a ASA 5510 at a remote site and ASA 5505 at our end. We were able to ping and monitor the remote location from our end and there were no problems initially. Recently, the ISP at the remote location was changed and we had updated the ASA rules, access list with the new public IP. The tunnel is up and working fine, but we are unable to ping or telnet the remote ASA. We are able to ping the servers, switches and all othert devices at the remote location. Except for the ASA 5510 at the remote location.
Please help as Im unable to monitor the ASA with my monitoring tool.
I have a ASA 5510 at a remote site and ASA 5505 at our end. We were able to ping and monitor the remote location from our end and there were no problems initially. Recently, the ISP at the remote location was changed and we had updated the ASA rules, access list with the new public IP. The tunnel is up and working fine, but we are unable to ping or telnet the remote ASA. We are able to ping the servers, switches and all othert devices at the remote location. Except for the ASA 5510 at the remote location.
Please help as Im unable to monitor the ASA with my monitoring tool.
Can you run a DIFF between the old and new configs just to be sure nothing has changed.
At the remote site, do you have access to the ASA logs? If the traffic is dropped, the syslogs should reflect that. (note, if you have access to internal hosts, you could ssh to one of those then ssh into ASA through it. ).
At the remote site, do you have access to the ASA logs? If the traffic is dropped, the syslogs should reflect that. (note, if you have access to internal hosts, you could ssh to one of those then ssh into ASA through it. ).
ASKER
Hi MikeKane,
The ASA logs shows that ICMP connection establishment and at the same time shows the Teardown as well. Im able to telnet the ASA from the LAN in the remote location.
Also in the logs, it shows that the ICMP packets have reached the ASA but there is no reply.
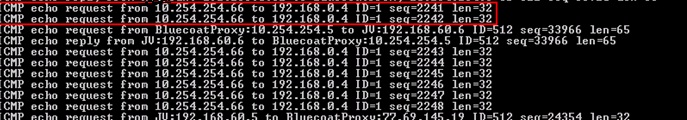
This log shows that packets from the monitoring server reaching the remote ASA but there is no reply.
Please let me know if you need more information.
The ASA logs shows that ICMP connection establishment and at the same time shows the Teardown as well. Im able to telnet the ASA from the LAN in the remote location.
Also in the logs, it shows that the ICMP packets have reached the ASA but there is no reply.
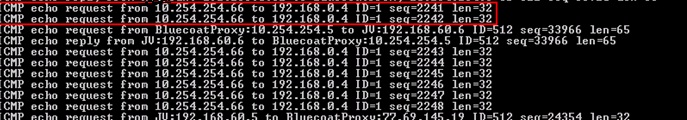
This log shows that packets from the monitoring server reaching the remote ASA but there is no reply.
Please let me know if you need more information.
Did you run the Diff between the 2 configs?
Also at the home office, perhaps you only allowed icmp from the original IP and not the new IP?
On the ASA at the remote site, on the CLI, do a SHOW LOGGING during the attempts and see if any packets are reported dropped.
Also at the home office, perhaps you only allowed icmp from the original IP and not the new IP?
On the ASA at the remote site, on the CLI, do a SHOW LOGGING during the attempts and see if any packets are reported dropped.
ASKER
Hi Mikekane,
The configurations on both sides were double checked and compared . It was found that the old configurations and the new one are the same , and nothing has changed .
At the Home ASA , IPs were changed to new ones and it was allowed to pass through the ASA
When logging was done at the remote ASA with a continuos ping from Home end , the following results were obtained which clearly shows the teardown of ICMP connections at the Remote ASA
May 04 2011 07:31:29 PRL-FW-INT-01 : %ASA-6-302020: Built inbound ICMP connection for faddr 10.254.254.72/512 gaddr192.168.0.4/0 laddr 192.168.0.4/0
May 04 2011 07:31:31 PRL-FW-INT-01 : %ASA-6-302021: Teardown ICMP connection for faddr 10.254.254.72/512
gaddr 192.168.0.4/0 laddr 192.168.0.4/0
What could be the possible problem , Mikekane ?
The configurations on both sides were double checked and compared . It was found that the old configurations and the new one are the same , and nothing has changed .
At the Home ASA , IPs were changed to new ones and it was allowed to pass through the ASA
When logging was done at the remote ASA with a continuos ping from Home end , the following results were obtained which clearly shows the teardown of ICMP connections at the Remote ASA
May 04 2011 07:31:29 PRL-FW-INT-01 : %ASA-6-302020: Built inbound ICMP connection for faddr 10.254.254.72/512 gaddr192.168.0.4/0 laddr 192.168.0.4/0
May 04 2011 07:31:31 PRL-FW-INT-01 : %ASA-6-302021: Teardown ICMP connection for faddr 10.254.254.72/512
gaddr 192.168.0.4/0 laddr 192.168.0.4/0
What could be the possible problem , Mikekane ?
Do you allow any any for icmp echo? Does the other ASA show any issues / dropped packets?
ASKER
Allowing any any ICMP echo that you are mentioning to , Is that for the outside interface or for the inside interface of the Remote ASA ? We were trying to ping the inside interface .
Yes , the packets are being dropped at the Remote ASA .
Yes , the packets are being dropped at the Remote ASA .
IF this is what you see in the syslog:
Then it doesn't look like packets are being dropped at this remote location. Did you look at the originating location to see if the return echos are being dropped by any chance.
if you have telnet active, try a telnet session to that internal IP. See what that syslog shows. What results here?
If neither of these yields any clues, you might want to run a packet capture through ASDM on each end to see if where the return packets are going....
May 04 2011 07:31:29 PRL-FW-INT-01 : %ASA-6-302020: Built inbound ICMP connection for faddr 10.254.254.72/512 gaddr192.168.0.4/0 laddr 192.168.0.4/0
May 04 2011 07:31:31 PRL-FW-INT-01 : %ASA-6-302021: Teardown ICMP connection for faddr 10.254.254.72/512
gaddr 192.168.0.4/0 laddr 192.168.0.4/0
May 04 2011 07:31:31 PRL-FW-INT-01 : %ASA-6-302021: Teardown ICMP connection for faddr 10.254.254.72/512
gaddr 192.168.0.4/0 laddr 192.168.0.4/0
Then it doesn't look like packets are being dropped at this remote location. Did you look at the originating location to see if the return echos are being dropped by any chance.
if you have telnet active, try a telnet session to that internal IP. See what that syslog shows. What results here?
If neither of these yields any clues, you might want to run a packet capture through ASDM on each end to see if where the return packets are going....
ASKER
Hi MikeKane,
Sorry for the delay in replying.
I'm unable to telnet to the internal IP as well. Please let me know whether you would require the configurations of the ASA for troubleshooting.
Sorry for the delay in replying.
I'm unable to telnet to the internal IP as well. Please let me know whether you would require the configurations of the ASA for troubleshooting.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Not provided with the right solution. We had to add the public ip in the monitoring tool for getting this resolved.
Thinking about the command management-access, ssh x.x.x.x inside, etc.