Archiving events using PHP + MySQL
I currently display a 'previous monthly events' dropdown of past events in on my website here..http://www.anjoman.co.uk/previous-monthly-meeting.php
The list is now way to long so I want to archive the list by year...Events 2009...Events 2010 and so on.
Any ideas howto go about this?
You can see I have used the date function in MySQL so hopefully this isn't too tricky!
Here's the script i'm currently using to display the results at the moment...
mysql_select_db($database_
$query_date = "SELECT * FROM monthly ORDER BY `date` DESC";
$date = mysql_query($query_date, $anjoman) or die(mysql_error());
$row_date = mysql_fetch_assoc($date);
$totalRows_date = mysql_num_rows($date);
<?php do { ?>
<a href="previous-monthly-mee
<?php } while ($row_date = mysql_fetch_assoc($date));
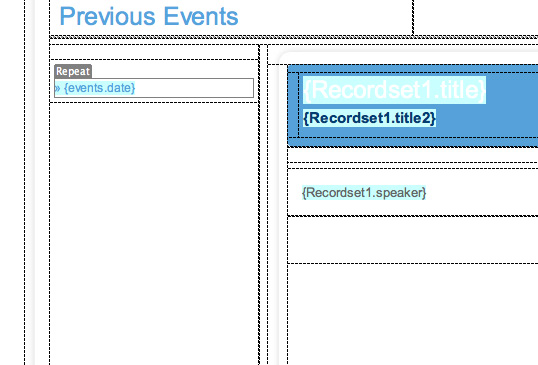
Screen-shot-2011-09-06-at-07.52..png
The list is now way to long so I want to archive the list by year...Events 2009...Events 2010 and so on.
Any ideas howto go about this?
You can see I have used the date function in MySQL so hopefully this isn't too tricky!
Here's the script i'm currently using to display the results at the moment...
mysql_select_db($database_
$query_date = "SELECT * FROM monthly ORDER BY `date` DESC";
$date = mysql_query($query_date, $anjoman) or die(mysql_error());
$row_date = mysql_fetch_assoc($date);
$totalRows_date = mysql_num_rows($date);
<?php do { ?>
<a href="previous-monthly-mee
<?php } while ($row_date = mysql_fetch_assoc($date));
Screen-shot-2011-09-06-at-07.52..png
ASKER
Yes, that's the idea, i'll try your code now.
With this method I guess I would need to add code each year?
With this method I guess I would need to add code each year?
You don't have to, you could pass a parameter for the year in the URL if you want:
// this should get all dates for 2009
// the next line should escape the url param and cast as an integer, this should keep you safe from SQL injection attacks
$year = (int) mysql_real_escape_string($_GET['year']);
mysql_select_db($database_anjoman, $anjoman);
$query_date = "SELECT * FROM monthly WHERE date >= '$year-0-0 00:00:00' AND date <= '$year-12-31 99:99:99' ORDER BY `date` DESC";
$date = mysql_query($query_date, $anjoman) or die(mysql_error());
$row_date = mysql_fetch_assoc($date);
$totalRows_date = mysql_num_rows($date);
Let me update that code to make sure it works:
// this should get all dates for 2009
// the next line should escape the url param and cast as an integer, this should keep you safe from SQL injection attacks
$year = mysql_real_escape_string($_GET['year']);
$year = (int)$year;
mysql_select_db($database_anjoman, $anjoman);
$query_date = "SELECT * FROM monthly WHERE date >= '".$year."-0-0 00:00:00' AND date <= '".$year."-12-31 99:99:99' ORDER BY `date` DESC";
$date = mysql_query($query_date, $anjoman) or die(mysql_error());
$row_date = mysql_fetch_assoc($date);
$totalRows_date = mysql_num_rows($date);
By the way, dates are kind of funny in sql, so if that method doesn't work, try this one:
Ref. http://www.roseindia.net/sql/sql-between-datetime.shtml
$query_date = "SELECT * FROM monthly WHERE date BETWEEN '".$year."-0-0 00:00:00' AND '".$year."-12-31 99:99:99' ORDER BY `date` DESC";Ref. http://www.roseindia.net/sql/sql-between-datetime.shtml
ASKER
Thanks for that EMB01,
I know have this query, I'm using events rather than date by the way from the table events which is the same as the table in the attachment above.
$year = mysql_real_escape_string($
$year = (int)$year;
mysql_select_db($database_
$query_events = "SELECT * FROM events WHERE date BETWEEN '".$year."-0-0 00:00:00' AND '".$year."-12-31 99:99:99' ORDER BY `date` DESC";
$events = mysql_query($query_events,
$row_events = mysql_fetch_assoc($events)
$totalRows_events = mysql_num_rows($events);
Nothing is showing on the page yet http://www.anjoman.co.uk/previous-events-archivetest.php
But this is probably down to the display code here...
<?php do { ?>
<a href="previous-events-arch
<?php } while ($row_events = mysql_fetch_assoc($events)
Does this need to change?
I know have this query, I'm using events rather than date by the way from the table events which is the same as the table in the attachment above.
$year = mysql_real_escape_string($
$year = (int)$year;
mysql_select_db($database_
$query_events = "SELECT * FROM events WHERE date BETWEEN '".$year."-0-0 00:00:00' AND '".$year."-12-31 99:99:99' ORDER BY `date` DESC";
$events = mysql_query($query_events,
$row_events = mysql_fetch_assoc($events)
$totalRows_events = mysql_num_rows($events);
Nothing is showing on the page yet http://www.anjoman.co.uk/previous-events-archivetest.php
But this is probably down to the display code here...
<?php do { ?>
<a href="previous-events-arch
<?php } while ($row_events = mysql_fetch_assoc($events)
Does this need to change?
Yes, please show me the output of this code:
$year = mysql_real_escape_string($_GET['year']);
$year = (int)$year;
die($year);
mysql_select_db($database_anjoman, $anjoman);
$query_events = "SELECT * FROM events WHERE date BETWEEN '".$year."-0-0 00:00:00' AND '".$year."-12-31 99:99:99' ORDER BY `date` DESC";
$events = mysql_query($query_events, $anjoman) or die(mysql_error());
$row_events = mysql_fetch_assoc($events);
$totalRows_events = mysql_num_rows($events);ASKER
Sure, how would I show that output?
(thanks for your patience!)
(thanks for your patience!)
ASKER
There does not seem to be any results showing.
I have attached a results test screenshot from Dreamweaver as well as the database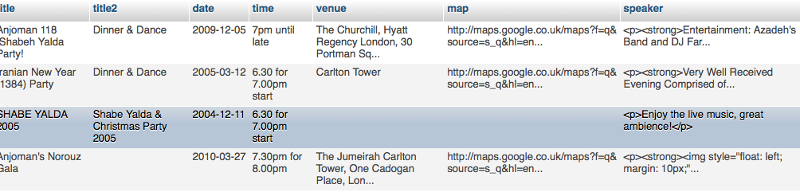
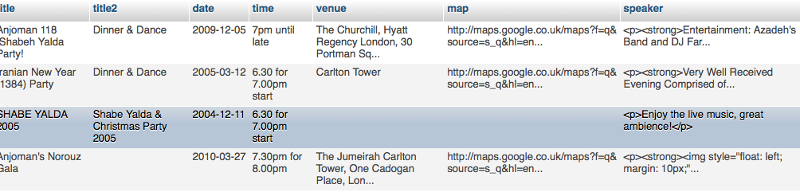 results.png
results.png
I have attached a results test screenshot from Dreamweaver as well as the database
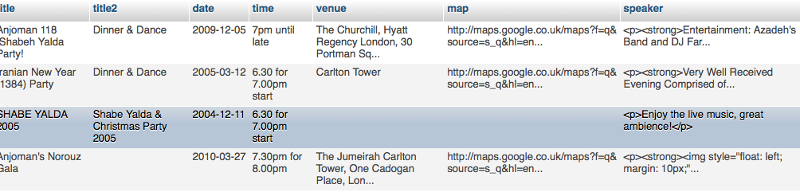
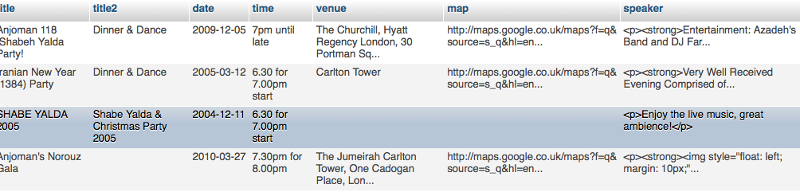 results.png
results.png
Thank you, but to send output, just go to the page where the parameter will be called; i.e.:
http://www.anjoman.co.uk/previous-events-archivetest.php?date=[whatever your date would be]
The die($date) line will end the script and display only the contents of the $date variable.
Please let me know if you need more help.
http://www.anjoman.co.uk/previous-events-archivetest.php?date=[whatever your date would be]
The die($date) line will end the script and display only the contents of the $date variable.
Please let me know if you need more help.
ASKER
Hi there,
There's no results showing on the page though so I can't click on anything to get to the results?
The page is actually shows blank http://www.anjoman.co.uk/previous-events-archivetest.php
I'm using...
$year = mysql_real_escape_string($
$year = (int)$year;
die($year);
mysql_select_db($database_
$query_events = "SELECT * FROM events WHERE date BETWEEN '".$year."-0-0 00:00:00' AND '".$year."-12-31 99:99:99' ORDER BY `date` DESC";
$events = mysql_query($query_events,
$row_events = mysql_fetch_assoc($events)
$totalRows_events = mysql_num_rows($events);
<?php do { ?>
<a href="previous-events-arch
<?php } while ($row_events = mysql_fetch_assoc($events)
There's no results showing on the page though so I can't click on anything to get to the results?
The page is actually shows blank http://www.anjoman.co.uk/previous-events-archivetest.php
I'm using...
$year = mysql_real_escape_string($
$year = (int)$year;
die($year);
mysql_select_db($database_
$query_events = "SELECT * FROM events WHERE date BETWEEN '".$year."-0-0 00:00:00' AND '".$year."-12-31 99:99:99' ORDER BY `date` DESC";
$events = mysql_query($query_events,
$row_events = mysql_fetch_assoc($events)
$totalRows_events = mysql_num_rows($events);
<?php do { ?>
<a href="previous-events-arch
<?php } while ($row_events = mysql_fetch_assoc($events)
K, just make your code like this then:
$year = mysql_real_escape_string($_GET['year']);
$year = (int)$year;
if (isset($_GET['year'])) { die($year); }
mysql_select_db($database_anjoman, $anjoman);
$query_events = "SELECT * FROM events WHERE date BETWEEN '".$year."-0-0 00:00:00' AND '".$year."-12-31 99:99:99' ORDER BY `date` DESC";
$events = mysql_query($query_events, $anjoman) or die(mysql_error());
$row_events = mysql_fetch_assoc($events);
$totalRows_events = mysql_num_rows($events);ASKER
Thanks again, still blank though...Results should show on the left where that small blue arrow is.
http://www.anjoman.co.uk/previous-events-archivetest.php
I'll attach the whole pages code too in case there's any clues there.
I'm using...
$year = mysql_real_escape_string($
$year = (int)$year;
if (isset($_GET['year'])) { die($year); }
mysql_select_db($database_
$query_events = "SELECT * FROM events WHERE date BETWEEN '".$year."-0-0 00:00:00' AND '".$year."-12-31 99:99:99' ORDER BY `date` DESC";
$events = mysql_query($query_events,
$row_events = mysql_fetch_assoc($events)
$totalRows_events = mysql_num_rows($events);
and...
<?php do { ?>
<a href="previous-events-arch
<?php } while ($row_events = mysql_fetch_assoc($events)
http://www.anjoman.co.uk/previous-events-archivetest.php
I'll attach the whole pages code too in case there's any clues there.
I'm using...
$year = mysql_real_escape_string($
$year = (int)$year;
if (isset($_GET['year'])) { die($year); }
mysql_select_db($database_
$query_events = "SELECT * FROM events WHERE date BETWEEN '".$year."-0-0 00:00:00' AND '".$year."-12-31 99:99:99' ORDER BY `date` DESC";
$events = mysql_query($query_events,
$row_events = mysql_fetch_assoc($events)
$totalRows_events = mysql_num_rows($events);
and...
<?php do { ?>
<a href="previous-events-arch
<?php } while ($row_events = mysql_fetch_assoc($events)
<?php
if (!function_exists("GetSQLValueString")) {
function GetSQLValueString($theValue, $theType, $theDefinedValue = "", $theNotDefinedValue = "")
{
if (PHP_VERSION < 6) {
$theValue = get_magic_quotes_gpc() ? stripslashes($theValue) : $theValue;
}
$theValue = function_exists("mysql_real_escape_string") ? mysql_real_escape_string($theValue) : mysql_escape_string($theValue);
switch ($theType) {
case "text":
$theValue = ($theValue != "") ? "'" . $theValue . "'" : "NULL";
break;
case "long":
case "int":
$theValue = ($theValue != "") ? intval($theValue) : "NULL";
break;
case "double":
$theValue = ($theValue != "") ? doubleval($theValue) : "NULL";
break;
case "date":
$theValue = ($theValue != "") ? "'" . $theValue . "'" : "NULL";
break;
case "defined":
$theValue = ($theValue != "") ? $theDefinedValue : $theNotDefinedValue;
break;
}
return $theValue;
}
}
$colname_Recordset1 = "-1";
if (isset($_GET['date'])) {
$colname_Recordset1 = (get_magic_quotes_gpc()) ? $_GET['date'] : addslashes($_GET['date']);
}
mysql_select_db($database_anjoman, $anjoman);
$query_Recordset1 = sprintf("SELECT id, title, title2, invitation, date_format(`date`,'%%D %%M %%Y') as `date`, `time`, venue, `map`, speaker, memberfee, guestfee, youngfee, youngmemberfee FROM events WHERE `date` = %s", GetSQLValueString($colname_Recordset1, "text"));
$Recordset1 = mysql_query($query_Recordset1, $anjoman) or die(mysql_error());
$row_Recordset1 = mysql_fetch_assoc($Recordset1);
$totalRows_Recordset1 = mysql_num_rows($Recordset1);
mysql_select_db($database_anjoman, $anjoman);
$query_date = "SELECT * FROM monthly ORDER BY `date` DESC";
$date = mysql_query($query_date, $anjoman) or die(mysql_error());
$row_date = mysql_fetch_assoc($date);
$totalRows_date = mysql_num_rows($date);
mysql_select_db($database_anjoman, $anjoman);
$query_gallery = "SELECT category_id, category_name, date, type FROM gallery_category WHERE type = 'event' ORDER BY date DESC";
$gallery = mysql_query($query_gallery, $anjoman) or die(mysql_error());
$row_gallery = mysql_fetch_assoc($gallery);
$totalRows_gallery = mysql_num_rows($gallery);
mysql_select_db($database_anjoman, $anjoman);
$query_gallerymonth = "SELECT category_id, category_name, `date`, type FROM gallery_category WHERE type = 'monthly' ORDER BY `date` DESC";
$gallerymonth = mysql_query($query_gallerymonth, $anjoman) or die(mysql_error());
$row_gallerymonth = mysql_fetch_assoc($gallerymonth);
$totalRows_gallerymonth = mysql_num_rows($gallerymonth);
$year = mysql_real_escape_string($_GET['year']);
$year = (int)$year;
if (isset($_GET['year'])) { die($year); }
mysql_select_db($database_anjoman, $anjoman);
$query_events = "SELECT * FROM events WHERE date BETWEEN '".$year."-0-0 00:00:00' AND '".$year."-12-31 99:99:99' ORDER BY `date` DESC";
$events = mysql_query($query_events, $anjoman) or die(mysql_error());
$row_events = mysql_fetch_assoc($events);
$totalRows_events = mysql_num_rows($events);
?>
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/1999/xhtml">
<head>
<meta http-equiv="Content-Type" content="text/html; charset=UTF-8" />
<title>Anjoman - Previous Events</title>
<script type="text/javascript" src="js/jquery-1.2.6.min.js"></script>
<script type="text/javascript" src="js/dropmenu.js"></script>
<script type="text/javascript">
function MM_preloadImages() { //v3.0
var d=document; if(d.images){ if(!d.MM_p) d.MM_p=new Array();
var i,j=d.MM_p.length,a=MM_preloadImages.arguments; for(i=0; i<a.length; i++)
if (a[i].indexOf("#")!=0){ d.MM_p[j]=new Image; d.MM_p[j++].src=a[i];}}
}
</script>
<link href="anjoman.css" rel="stylesheet" type="text/css" />
<script type="text/javascript" src="js/coolclock.js"></script>
<script src="js/menu-collapsed.js" type="text/javascript"></script>
<link rel="stylesheet" type="text/css" href="css/menu.css" />
<link href="css/style.css" rel="stylesheet" type="text/css" />
</head>
<body>
<!-- START of freefind onpage results html -->
<!-- position these div's right after your body tag -->
<!-- FreeFind on-page results divs -->
<div id="ffresult_win" style=" z-index:1; padding: 20px 0 16px 0; margin:0px; width:538px; height:728px; border:none; display:none; position:absolute; top:0px; left:0px;">
<div id="ffresult_bar" onmousedown="ffresults.drag(event,false)" style="cursor: move; z-index:5; position:absolute; top:0px; left:0px; background-color:maroon; padding:0; text-align: right; width:100%; height:20px; display:block; border:solid; border-width: 1px; border-bottom: 0px; border-color:maroon;">
<a id="ffrclose" style="z-index:6; font-family: arial, verdana, sans-serif; font-size:8pt; color:white; " href="javascript:ffresults.hide()">Close window [X]</a>
</div>
<div id="ffresult_2" style="z-index:7; position: relative; height: 100%; background-color:white; display:block;">
<div id="ffresult_cvr" style="z-index:0; position:absolute; top:0px; left:0px; display:block; width:100%; height:100%;">
</div>
<iframe id="ffresult_ifr" name="ffresult_frame" style="z-index:1; position:absolute; top:0px; left:0px; border:solid; border-width: 0px 1px 0px 1px; border-color:gray;" src="" width="100%" height="100%" scrolling="auto" frameborder="0">
</iframe>
</div>
<div id="ffresult_btm" style=" position:absolute; bottom:-1; left:0px; border:solid; border-color:gray; border-width: 1px; border-top: 0px; display: block; z-index:18; background-color:#d0d0d0; width:100%; height:16px; " >
<div id="ffresult_sbx" onmousedown="ffresults.drag(event,true);" style="cursor: se-resize; float:right; border:none; border-color:gray; border-width: 0px; width:16px; height:16px; "><img style="" id="ffresult_szimg" height=16 width=16 border=0 src="" alt=""></div>
</div>
</div>
<!-- FreeFind on-page results handler -->
<script type="text/javascript">
<!--
var ffresults = {
// copyright 2008 - 2010 FreeFind.com - authorized for use with the FreeFind service only
// Start of config settings
autoPos : true, // automatic initial window position / size.
// if autoPos if false, the following four numbers are used as initial window position and size
initialX : 78, // left position (pixels)
initialY : 66, // right position (pixels)
initialH : 395, // height of window
initialW : 622, // width of window
// choose a number for z-index that is high enough so the results window appears above other windows on your page
initialZ : 10000000, // initial z-index of the results window
// the following value controls the color of the window's drag bar (top area of window)
barColor : '#59A3D9',
// end of config settings
element : undefined,
cover : undefined,
mouseDownX : 0,
mouseDownY : 0,
objectX : 0,
objectY : 0,
objectH : 0,
objectW : 0,
ipos : false,
resize : false,
sizeImageUrl : 'http://search.freefind.com/img/rsize.gif',
selectFunc : undefined,
selectState : undefined,
mozSelect : undefined,
noSelect : function()
{
var obj = document.body;
ffresults.selectFunc = obj.onselectstart;
ffresults.selectState = obj.unselectable;
ffresults.mozSelect = obj.style.MozUserSelect;
obj.onselectstart = function(){ return false; };
obj.unselectable = 'on';
obj.style.MozUserSelect = 'none';
},
restoreSelect : function()
{
var obj = document.body;
obj.onselectstart = ffresults.selectFunc;
obj.unselectable = ffresults.selectState;
obj.style.MozUserSelect = ffresults.mozSelect;
},
drag : function (e,size)
{
if(!document.getElementById) return;
if(!e) e = window.event;
var targ = e.target || e.srcElement;
ffresults.resize = size;
if(targ.id != 'ffresult_bar' && targ.id != 'ffresult_szimg') return true;
ffresults.noSelect();
ffresults.element = document.getElementById('ffresult_win');
ffresults.objectX = parseInt(ffresults.element.style.left,10);
ffresults.objectY = parseInt(ffresults.element.style.top,10);
ffresults.objectH = parseInt(ffresults.element.style.height,10);
ffresults.objectW = parseInt(ffresults.element.style.width,10);
ffresults.cover = document.getElementById('ffresult_cvr');
ffresults.cover.style.zIndex = '40';
ffresults.mouseDownX = e.clientX;
ffresults.mouseDownY = e.clientY;
if(e.preventDefault) e.preventDefault();
e.returnValue = false;
e.cancelBubble = true;
ffresults.attach(document,"mouseup",ffresults.drop);
ffresults.attach(document,"mousemove",ffresults.move);
},
attach : function(to,eventname,func)
{
if(to.addEventListener)
to.addEventListener(eventname,func,false);
else
to.attachEvent("on" + eventname,func);
},
detach : function(to,eventname,func)
{
if(to.removeEventListener)
to.removeEventListener(eventname,func,false);
else
to.detachEvent("on" + eventname,func);
},
drop : function(e)
{
ffresults.detach(document,"mouseup",ffresults.drop);
ffresults.detach(document,"mousemove",ffresults.move);
ffresults.cover.style.zIndex = 0;
ffresults.element = null;
ffresults.restoreSelect();
},
move: function(e)
{
if(!e) e = window.event;
e.returnValue = false;
e.cancelBubble = true;
if(e.preventDefault) e.preventDefault();
var x = e.clientX;
var y = e.clientY;
if(ffresults.resize)
{
var winW = ffresults.objectW + x - ffresults.mouseDownX;
var winH = ffresults.objectH + y - ffresults.mouseDownY;
if(winH < 128) winH = 128;
if(winW < 128) winW = 128;
ffresults.element.style.width = winW + "px";
ffresults.element.style.height = winH + "px";
}
else
{
var left = ffresults.objectX + x - ffresults.mouseDownX;
var top = ffresults.objectY + y - ffresults.mouseDownY;
ffresults.element.style.left = left + "px";
ffresults.element.style.top = top + "px";
}
},
hide : function()
{
var rStyle = document.getElementById('ffresult_win').style;
rStyle.display = "none";
rStyle.zIndex = 0;
var ifr = document.getElementById('ffresult_ifr');
if(ifr) ifr.src="";
var szImg = document.getElementById('ffresult_szimg');
if(szImg) szImg.src = "";
},
show : function(num)
{
if(!document.getElementById) return;
var searchForm = document.getElementById('ffresult_sbox'+num);
var idxLink = document.getElementById('ffresult_idx'+num);
var smpLink = document.getElementById('ffresult_smp'+num);
var advLink = document.getElementById('ffresult_adv'+num);
if(searchForm) searchForm.target = 'ffresult_frame';
if(idxLink) idxLink.target = 'ffresult_frame';
if(smpLink) smpLink.target = 'ffresult_frame';
if(advLink) advLink.target = 'ffresult_frame';
var rDiv = document.getElementById('ffresult_win');
if(!ffresults.ipos)
{
if(ffresults.autoPos)
{
ffresults.computePos(rDiv);
}
else
{
rDiv.style.top = ffresults.initialY + 'px';
rDiv.style.left = ffresults.initialX + 'px';
rDiv.style.width = ffresults.initialW + 'px';
rDiv.style.height = (ffresults.initialH - 36) + 'px';
}
ffresults.ipos = true;
}
var szImg = document.getElementById('ffresult_szimg');
if(szImg) szImg.src = ffresults.sizeImageUrl;
var dragBar = document.getElementById('ffresult_bar');
if(dragBar)
{
dragBar.style.backgroundColor = ffresults.barColor;
dragBar.style.borderColor = ffresults.barColor;
}
rDiv.style.zIndex = ffresults.initialZ;
rDiv.style.display = "block";
},
computePos : function(rDiv)
{
var view = ffresults.viewSize();
var w = parseInt(view.width * 0.75,10);
var h = parseInt(view.height * 0.75,10);
if(w < 220) w = 220;
if(h < 220) h = 220;
var left = parseInt((view.width - w ) / 2,10);
var top = parseInt((view.height - (h + 36)) / 2,10);
if(left < 0) left = 0;
if(top < 0) top = 0;
rDiv.style.top = (top + view.scrollY) + 'px';
rDiv.style.left = (left + view.scrollX) + 'px';
rDiv.style.width = w + 'px';
rDiv.style.height = h + 'px';
},
viewSize : function()
{
var w = 0;
var h = 0;
var sx = 0;
var sy = 0;
if(window.innerWidth)
{ // non-ie
w = window.innerWidth;
h = window.innerHeight;
sx = window.pageXOffset;
sy = window.pageYOffset;
}
else
{
var elem;
if(document.documentElement && document.documentElement.clientWidth != 0)
{ // ie strict
elem = document.documentElement;
}
else
{ // ie quirks
elem = document.body;
}
w = elem.clientWidth;
h = elem.clientHeight;
sx = elem.scrollLeft;
sy = elem.scrollTop;
}
return {width: w,height: h, scrollX: sx, scrollY: sy};
}
};
//-->
</script>
<!-- END of freefind onpage results html -->
<table width="1008" height="305" border="0" align="center" cellpadding="0" cellspacing="0" class="monthlymtings">
<tr>
<td height="152" valign="top"><table width="1008" border="0" cellspacing="0" cellpadding="0">
<tr>
<td><table width="100%" border="0" cellpadding="0" cellspacing="0" class="mapbg">
<tr>
<td width="26%" valign="middle"><table width="100" border="0" cellspacing="0" cellpadding="5">
<tr>
<td><img src="img/anjoman.gif" width="255" height="74" alt="logo" /></td>
</tr>
</table></td>
<td width="74%" align="right" valign="top"><table width="100%" border="0" cellspacing="0" cellpadding="0">
<tr>
<td align="right"><div class="iframecontainer" style="height:30;width:100%;">
<iframe src="http://www.anjoman.co.uk/clock.php" width="325" height="100" frameborder="0" scrolling="No"></iframe>
</div></td>
</tr>
</table></td>
</tr>
</table></td>
</tr>
<tr>
<td><table width="100%" border="0" cellpadding="0" cellspacing="0" class="bottom3">
<tr>
<td width="78%" align="left"><ul id="nav-one" class="dropmenu">
<li> <a href="http://www.anjoman.co.uk/index.php">HOME</a></li>
<li> <a href="http://www.anjoman.co.uk/about.php">ABOUT ANJOMAN</a>
<ul>
<li><a href="http://www.anjoman.co.uk/previousboard.php">Board members</a></li>
<li><a href="http://www.anjoman.co.uk/speakers.php">Selected speakers</a></li>
</ul>
</li>
<li><a href="http://www.anjoman.co.uk/monthly-meeting.php">MONTHLY MEETING</a>
<ul>
<li><a href="http://www.anjoman.co.uk/monthly-meeting.php">Next Monthly Meeting</a></li>
<li><a href="http://www.anjoman.co.uk/previous-monthly-meeting.php">Previous Monthly Meetings</a></li>
<li><a href="http://www.anjoman.co.uk/galleries.php">Galleries</a></li>
</ul>
<li><a href="http://www.anjoman.co.uk/events.php">EVENTS</a>
<ul>
<li><a href="http://www.anjoman.co.uk/events.php">Next Event</a></li>
<li><a href="http://www.anjoman.co.uk/previous-events.php">Previous Events</a></li>
<li><a href="http://www.anjoman.co.uk/galleries.php">Galleries</a></li>
</ul>
<li><a href="http://www.anjoman.co.uk/joinanjoman.php">JOIN ANJOMAN</a></li>
<li> <a href="http://www.anjoman.co.uk/contact.php">CONTACT US</a></li>
<li> <a href="http://www.anjoman.co.uk/exchange.php">INFORMATION</a>
<ul>
<li><a href="http://www.anjoman.co.uk/exchange.php">Exchange Rates</a></li>
</ul>
</li>
<li> </li>
</ul></td>
<td width="22%" align="right"><table cellpadding="0" cellspacing="0" border="0" >
<tr>
<td colspan="2" align="right" style="font-family: Arial, Helvetica, sans-serif; font-size: 7.5pt;"><form id="ffresult_sbox0" style="margin:0px; margin-top:4px;" action="http://search.freefind.com/find.html" method="get" accept-charset="utf-8" onsubmit="ffresults.show(0);">
<input type="hidden" name="si" value="96214948" />
<input type="hidden" name="pid" value="r" />
<input type="hidden" name="n" value="0" />
<input type="hidden" name="_charset_" value="" />
<input type="hidden" name="bcd" value="÷" />
<input type="hidden" name="sbv" value="j1" />
<table width="100%" border="0" cellspacing="0" cellpadding="0">
<tr>
<td><input type="text" name="query" size="15" /></td>
<td><input type="image" name="imageField" id="imageField" src="img/search.png" /></td>
</tr>
</table>
</form></td>
</tr>
</table></td>
</tr>
</table></td>
</tr>
</table></td>
</tr>
<tr>
<td><table width="100%" border="0" cellspacing="0" cellpadding="0">
<tr>
<td width="697" valign="top"><img src="img/topcurve.jpg" width="1008" height="23" alt="topcurve" /></td>
</tr>
<tr>
<td align="center" valign="top" class="middlecurve"><table width="95%" border="0" cellpadding="0" cellspacing="0">
<tr>
<td><table width="100%" border="0" cellpadding="10" cellspacing="0" class="bottomgreydots">
<tr>
<td width="38%"><h1>Previous Events<br />
</h1></td>
<td width="62%" align="right"> </td>
</tr>
</table></td>
</tr>
<tr>
<td><table width="100%" border="0" cellpadding="0" cellspacing="0" class="top3">
<tr>
<td width="65%" valign="top"><table width="100%" border="0" cellspacing="0" cellpadding="0">
<tr>
<td width="22%" valign="top"><table width="100%" border="0" cellpadding="5" cellspacing="0" class="top15">
<tr>
<td><?php do { ?>
<a href="previous-events-archivetest.php?date=<?php echo $row_events['date']; ?>" class="eventsdrop">» <?php echo $row_events['title']; ?></a><br />
<?php } while ($row_events = mysql_fetch_assoc($events)); ?></td>
</tr>
</table></td>
<td width="78%" align="right" valign="top"><table width="100" border="0" cellspacing="0" cellpadding="0">
<tr>
<td width="697" valign="top"><img src="img/small-white-top.jpg" width="740" height="20" alt="topcurve" /></td>
</tr>
<tr>
<td align="center" valign="top" class="middlecurveCopy"><table width="90%" border="0" cellpadding="0" cellspacing="0" >
<tr>
<td><table width="98%" border="0" cellspacing="0" cellpadding="0">
<tr>
<td width="962"><img src="img/bluetop.jpg" width="700" height="8" alt="bluetop" /></td>
</tr>
<tr>
<td align="center" bgcolor="#5BA2D6"><table width="97%" border="0" cellspacing="0" cellpadding="5">
<tr>
<td align="left"><span class="monthlytitle"><?php echo $row_Recordset1['title']; ?></span><br />
<span class="subtitle"><?php echo $row_Recordset1['title2']; ?></span></td>
</tr>
</table></td>
</tr>
<tr>
<td><img src="img/bluebottom.jpg" width="700" height="9" alt="bluebottom" /></td>
</tr>
</table></td>
</tr>
<tr>
<td><table width="100" border="0" cellpadding="0" cellspacing="0" class="top15">
<tr>
<td width="70%" align="left" valign="top"><table width="430" border="0" cellpadding="15" cellspacing="0" class="top3">
<tr>
<td><?php echo $row_Recordset1['speaker']; ?></td>
</tr>
<tr>
<td> </td>
</tr>
</table></td>
<td width="30%" align="right" valign="top"><table width="240" border="0" cellpadding="0" cellspacing="0">
<tr>
<td><img src="img/gray-top.jpg" width="268" height="21" alt="greytop" /><br /></td>
</tr>
<tr>
<td align="center" class="greymiddle"><table width="95%" border="0" cellspacing="0" cellpadding="15">
<tr>
<td align="left" valign="top"><span class="infoboxblue">Date<br />
</span><?php echo $row_Recordset1['date']; ?><span class="infoboxblue"><br />
<br />
Time <br />
</span><?php echo $row_Recordset1['time']; ?><span class="infoboxblue"><br />
<br />
Venue<br />
</span><?php echo $row_Recordset1['venue']; ?><span class="infoboxblue"><br />
<br />
</span><span class="darkbluelink"><a href="<?php echo $row_Recordset1['map']; ?>" target="_new" class="darkbluelink"><strong>Click here for a map</strong></a></span><span class="infoboxblue"><br />
<br />
Fees</span><span class="whitetext"><br />
</span><strong>Members</strong> £<?php echo $row_Recordset1['memberfee']; ?><br />
<strong>Guests</strong> £<?php echo $row_Recordset1['guestfee']; ?><br />
<strong>Young Members</strong> £<?php echo $row_Recordset1['youngmemberfee']; ?><br />
(Age 25 and under) <br />
<strong>Young Guests</strong> £<?php echo $row_Recordset1['youngfee']; ?><br />
(Age 25 and under) <span class="whitetext"><br />
<br />
<br />
</span><span class="whitetext"> <a href="mailto:events@anjoman.co.uk" class="darkbluelink">RSVP to events@anjoman.co.uk</a></span></td>
</tr>
</table></td>
</tr>
<tr>
<td><img src="img/gray-bottom.jpg" width="268" height="22" alt="greybottom" /></td>
</tr>
</table></td>
</tr>
</table></td>
</tr>
</table></td>
</tr>
<tr>
<td valign="top"><img src="img/small-bottom.jpg" width="740" height="29" alt="bottomcurve" /></td>
</tr>
</table></td>
</tr>
</table></td>
</tr>
</table></td>
</tr>
</table></td>
</tr>
<tr>
<td valign="top"><img src="img/bottomcurve.jpg" width="1008" height="25" alt="bottomcurve" /></td>
</tr>
</table></td>
</tr>
<tr>
<td><table width="100%" border="0" align="right" cellpadding="15" cellspacing="0" class="bottom-border">
<tr>
<td align="right" valign="top"><span class="bottomcopy">© Anjoman 2011</span></td>
</tr>
</table></td>
</tr>
</table>
<p class="events"> </p>
<p> </p>
</body>
</html>
<?php
mysql_free_result($Recordset1);
mysql_free_result($date);
mysql_free_result($speakers);
mysql_free_result($gallery);
mysql_free_result($events);
?>
Ok, I hope this works... Just run this in place of the old one and tell me what it says. Be sure to point your browser to:
http://www.anjoman.co.uk/previous-events-archivetest.php?year=2010
http://www.anjoman.co.uk/previous-events-archivetest.php?year=2010
$year = mysql_real_escape_string($_GET['year']);
// IF THE NEXT LINE WORKS, DELETE IT AND CONTINUE
echo 'year is '.$year; die;
$date1 = $year;
$date1 = $date1 . " 00:00:00";
$date2 = $date1+1 . " 23:59:59";
// IF THE NEXT LINE WORKS, DELETE IT AND CONTINUE
echo 'date1 is '.$date1; die;
// IF THE NEXT LINE WORKS, DELETE IT AND CONTINUE
echo 'date2 is '.$date2; die;
mysql_select_db($database_anjoman, $anjoman);
$query_events = "SELECT * FROM events WHERE date BETWEEN '".$year."-0-0 00:00:00' AND '".$year."-12-31 99:99:99' ORDER BY `date` DESC";
// IF THE NEXT LINE WORKS, DELETE IT AND CONTINUE
echo 'query is '.$query_events; die;
$events = mysql_query($query_events, $anjoman) or die(mysql_error());
while ($row_events = mysql_fetch_assoc($events)) {
echo var_dump($row_events);
}
$totalRows_events = mysql_num_rows($events);
// IF THE NEXT LINE WORKS, DELETE IT AND CONTINUE
echo 'total rows '.$totalRows_events; die;
Use this one actually, I've updated the query:
$year = mysql_real_escape_string($_GET['year']);
// IF THE NEXT LINE WORKS, DELETE IT AND CONTINUE
echo 'year is '.$year; die;
$date1 = $year;
$date1 = $date1 . " 00:00:00";
$date2 = $date1+1 . " 23:59:59";
// IF THE NEXT LINE WORKS, DELETE IT AND CONTINUE
echo 'date1 is '.$date1; die;
// IF THE NEXT LINE WORKS, DELETE IT AND CONTINUE
echo 'date2 is '.$date2; die;
mysql_select_db($database_anjoman, $anjoman);
$query_events = "SELECT * FROM events WHERE date BETWEEN '$date1' AND '$date2' ORDER BY `date` DESC";
// IF THE NEXT LINE WORKS, DELETE IT AND CONTINUE
echo 'query is '.$query_events; die;
$events = mysql_query($query_events, $anjoman) or die(mysql_error());
while ($row_events = mysql_fetch_assoc($events)) {
echo var_dump($row_events);
}
$totalRows_events = mysql_num_rows($events);
// IF THE NEXT LINE WORKS, DELETE IT AND CONTINUE
echo 'total rows '.$totalRows_events; die;ASKER
Thanks for that,
Here's what you get with that...
http://www.anjoman.co.uk/previous-events-archivetest.php
And this is the code to create the archive list...
<?php do { ?>
<a href="previous-events-arch
<?php } while ($row_events = mysql_fetch_assoc($events)
Here's what you get with that...
http://www.anjoman.co.uk/previous-events-archivetest.php
And this is the code to create the archive list...
<?php do { ?>
<a href="previous-events-arch
<?php } while ($row_events = mysql_fetch_assoc($events)
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
ASKER
Ok,i'll try that..
ASKER
I'm sure this works but I feel I may not of described what I need properly so i'm going to ask again as a separate question in more detail.
Well this is only the first part; we want to make sure our variables get values, our queries return resources, then we'll handle formatting issues.

Events 2009...Events 2010 and so on.
Then, a dropdown would display the specific year they've selected?
If so, you can try this:
Open in new window