Creating a Static Route in Sonicwall NSA 240 between 2 Class C Networks
I'm currently trying to tie together 2 networks using a route in Sonicwall OS Enhanced
Network 1
IP: 192.168.17.x
Subnet: 255.255.255.0
Interface X0 on sonicwall
Network 2
IP: 192.168.11.x
Subnet: 255.255.255.0
Interface X3 on sonicwall
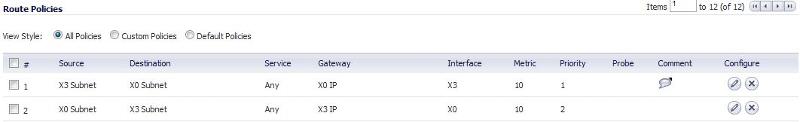
The route I try to put in is the following:
What am I missing to make the 2 networks talk to each other. I know I can tie them together by changing the subnet to 255.255.0.0 or changing IPs to Class A 10.x.x.x, but don't want to do that because of the labor involved. If I could just setup a static route and accomplish this without having to change the Static IPs on all my servers and such it would save a ton of time.
Thank you,
Network 1
IP: 192.168.17.x
Subnet: 255.255.255.0
Interface X0 on sonicwall
Network 2
IP: 192.168.11.x
Subnet: 255.255.255.0
Interface X3 on sonicwall
The route I try to put in is the following:
What am I missing to make the 2 networks talk to each other. I know I can tie them together by changing the subnet to 255.255.0.0 or changing IPs to Class A 10.x.x.x, but don't want to do that because of the labor involved. If I could just setup a static route and accomplish this without having to change the Static IPs on all my servers and such it would save a ton of time.
Thank you,
Being in the same zone should fix any firewall issues. Looking at your routes, I think they Interface is reversed. The interface should match the Destination subnet. So, route 1 has the X0 subnet as the destination so the Interface needs to be X0. Vice versa for route 2.
ASKER
Ok tried reversing the interfaces on my Routes. No go
Using only Route #1 as defined in my first screenshot on the question.I deleted Route #2 and then I am able to ping my gateway on the other network 192.168.17.1 from any 192.168.11.x computer. However, anything else on the 192.168.17.x network is unavailable from the other network. Progress, but not quite there yet.
Using only Route #1 as defined in my first screenshot on the question.I deleted Route #2 and then I am able to ping my gateway on the other network 192.168.17.1 from any 192.168.11.x computer. However, anything else on the 192.168.17.x network is unavailable from the other network. Progress, but not quite there yet.
ASKER
Disregard last response, deleted all my custom routes and im still able to get access to 192.168.17.1 from the 11 address. Back to square one.
So, without any custom routes and 192.168.17.0/24 on X1 and 192.168.11.0/24 on X3, you can ping anything on 192.168.11.0/24 from 192.168.17.0/24, but not 192.168.17.0/24 to 192.168.11.0/24, correct?
ASKER
Correct, although I can't access file shares going from 192.168.17.0/24 to 192.168.11.0/24. Ping does work in that direction though.
When you connect, are you trying to use DNS name or IP? I'm thinking that, as it stands, the sonicwall should know how to route the traffic. When you setup the interfaces, it automatically creates the routes. Something else is going on. If ping works both directions, but you can't get to file shares, then it's possible it's simply DNS needs to be setup.
ASKER
I'm using IP. The sonicwall grabs the DNS setting from the DNS server on 192.168.17.3 and DHCP for 192.168.17.x is handled by the same server as well.
so, UNC to a server on .17 from .11 doesn't show you shares? Please confirm that firewall access rules X0 <> X3 just to be certain we cover all our bases.
Also, what's handling DHCP on the .11?
Also, what's handling DHCP on the .11?
ASKER
I can confirm that Access rules don't conflict with this. You can see in my Access rules screenshot that I have a Any Any Any rule for LAN to LAN, but went ahead and added a X0 <> X3 rule just incase. DHCP is handled by Sonicwall on the .11 range.
Sorry, you did provide that information already. Not being able to see things for myself, I suppose the next thing I'd do is create a zone and assign it to the X3 interface. Your sonicwall should be routing properly based on what I know of the hardware. Creating the zone will help us visually see things as separate within the access rules and routing tables.
ASKER
I've requested that this question be deleted for the following reason:
I don't think this is possible given my current configuration. I will have to reconfigure the network to allow a more standard solution, such as changing subnet to 255.255.0.0.
I don't think this is possible given my current configuration. I will have to reconfigure the network to allow a more standard solution, such as changing subnet to 255.255.0.0.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
The routing issue is deeper than changing the subnet according to digitap, further troubleshooting required.
ASKER
Thank you for the help, but I think the routing issue is much deeper and complex than I first believed the question to be. I now believe that the issues lie in the servers that are issuing DHCP / DNS.
@modguy :: I know. Not much to say.
@homergfunk :: I had one of those moments after clicking the submit button that I should have waited a little bit longer. Having a bad day I guess. Sorry to muck up your question with my drama.
@homergfunk :: I had one of those moments after clicking the submit button that I should have waited a little bit longer. Having a bad day I guess. Sorry to muck up your question with my drama.
ASKER
No worries, my current situation is complicated from phasing out an existing network. I have a Essential Business Server 2008 installation and am working on phasing it out, since Microsoft DID phase it out. So I'm stuck with a bunch of proprietary Server 2008 installations and my business is expanding past the EBS model. I am currently side-stepping the Forefront TMG server due to a variety of issues I've run into with VOIP incompatibilities. I need to decommission it completely and convert all the server installations to Server 2008 standard. No worries on the response, we all have days like that, again, I appreciate the help.
Sure. I appreciate your forgiveness. Good luck on the conversion. Sounds like a big job!
The issue you may be experiencing quite possibly be the firewall access rules. When you created the zone you assigned the X3 interface, what kind of zone did you make it? Is it Trusted? Consider going to Firewall > Access Rules and review the rules between X3 <> X0.