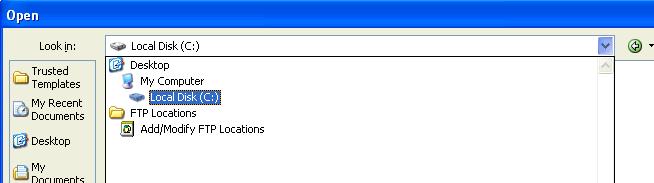
Office 2010 how modify view in open/look in
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
My Computer should be listed on the left right below My Documents.
ASKER
I know, but I would like to avoid a click... to go directly on my computer... any registry trick??
None that I can find and it appears that Microsoft is not inclined to change it from reading the KB article.
ASKER
Ok, then no other solution =)
Thanks for help.
Thanks for help.
ASKER