pravink22
asked on
Auto filling
I am trying to write a perl script to auto fill on a forum using WWW::Mechanize;
__________________________
use WWW::Mechanize;
$mech = WWW::Mechanize->new();
$input1 = "TITLE";
$input2 = "BODY";
$mech->get("URL");
$mech->form_with_fields(("
$mech->field("subject",$in
$mech->field("XXXX",$input
$mech->submit_form();
__________________________
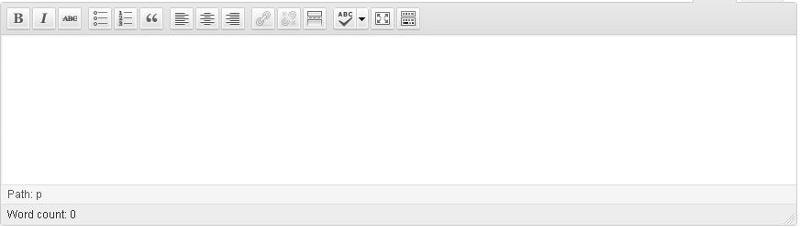
From the source code of the webpage I came to know that TITLE "name=subject", but I am unable to find the name of the "BODY", for your reference I am attaching a screenshot of the BODY.
Can someone help me in finding the name of BODY?
__________________________
use WWW::Mechanize;
$mech = WWW::Mechanize->new();
$input1 = "TITLE";
$input2 = "BODY";
$mech->get("URL");
$mech->form_with_fields(("
$mech->field("subject",$in
$mech->field("XXXX",$input
$mech->submit_form();
__________________________
From the source code of the webpage I came to know that TITLE "name=subject", but I am unable to find the name of the "BODY", for your reference I am attaching a screenshot of the BODY.
Can someone help me in finding the name of BODY?
I think maybe you need to look for a TEXTAREA form element instead.
Can you post the HTML Code of the entire FORM (from <FORM...> to </FORM>)?
ASKER
its a wordpress, admin posting page
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Its works Gr8... Thanks for sharing... :)
ASKER
<body id="tinymce" class="mceContentBody wp-editor" dir="ltr"><p><br data-mce-bogus="1"></p></b