elmtechExpert
asked on
Set up a simple html or picture to be the only page in my web
Hello experts,
I am completly new to web programming.
I boaght a new domain and it is stored in web hosting comapny.
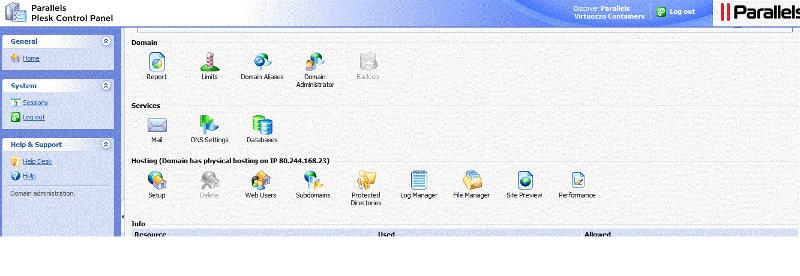
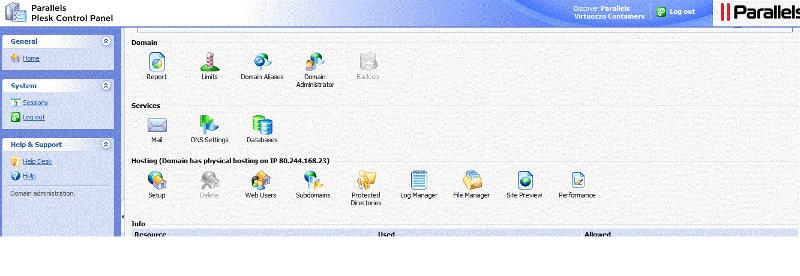
I know how to read mails and I have access to the web management called "plesk control panel".
I only need few step to set up a one page in to my web site.
How to do it ?
I have attached the screen I see when I go into my site as owner of the site.
Regards,
elm
I am completly new to web programming.
I boaght a new domain and it is stored in web hosting comapny.
I know how to read mails and I have access to the web management called "plesk control panel".
I only need few step to set up a one page in to my web site.
How to do it ?
I have attached the screen I see when I go into my site as owner of the site.
Regards,
elm
ASKER
Thanks dkellner,
All sound good and familiar,i will follow all your instructions,
My main problem is how to put file in the root with the web hosting managment?
Thanks,
Elm
All sound good and familiar,i will follow all your instructions,
My main problem is how to put file in the root with the web hosting managment?
Thanks,
Elm
Hi Elm,
You can use the File Manager feature of the web hosting management to transfer files from your pc to web hosting and vice versa.
Hope that helps!
Cheers! =)
You can use the File Manager feature of the web hosting management to transfer files from your pc to web hosting and vice versa.
Hope that helps!
Cheers! =)
kwingherrero is right.
If you're lost, give us some screenshot after clicking the "File Manager" icon of the last icon row and we'll find out what's next.
If you're lost, give us some screenshot after clicking the "File Manager" icon of the last icon row and we'll find out what's next.
ASKER
where in file mager I should copy the index.html file.
What is the root directory ?
Thanks,
Elm
What is the root directory ?
Thanks,
Elm
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
This is the solution
Create a file named "index.html".
First, write a simple "HELLO WORLD" in it (just this text, nothing else), put it on the document root on the server, and check what happens. You should see HELLO WORLD in Times New Roman (or whatever the browser default font is) when you visit your page from the web.
STEP 2
If this works, try something more complex:
Open in new window
Now when you visit your site, you should see "My First Page" as a browser title, and the word "WORLD" should get bold.
STEP 3
Follow some HTML tutorial to learn the basics - w3schools for example. You can find everything there even as a beginner but it will be your friend all along the way. We experienced guys also use it a lot. Check "Learn HTML" first.
If you want to show an image on your site, look for the IMG tag (HTML is all about so-called "tags"), w3s will also teach you that. It's easy - you upload a file like mypicture.jpg, then say <img src="mypicture.jpg"> somewhere between <body> and </body> - and there you go, your image smiles back at you.
If this is not the answer, let's discuss the question again :)