How to change IP address on VM within Citrix XenCenter
Hi Guys,
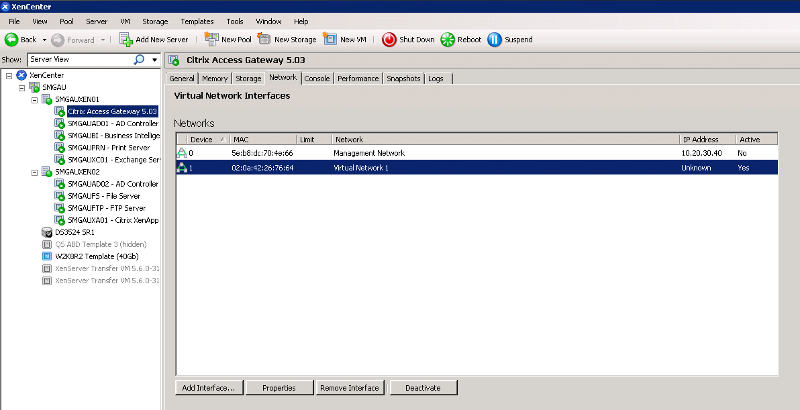
I just upgraded our Citrix CAG to V5.03 and took a snapshot before and after.
What I realised though is that after updating to V5.03 the IP of the CAG is now 10.20.30.40.
I cannot find where I can modify this to my desired IP. Can someone please point me in the right direction.
I have added a Virtual Network interface as per the other VM's in this environment but can't seem to change the IP so that it is correct.
I have attached a screenshot as well for reference.
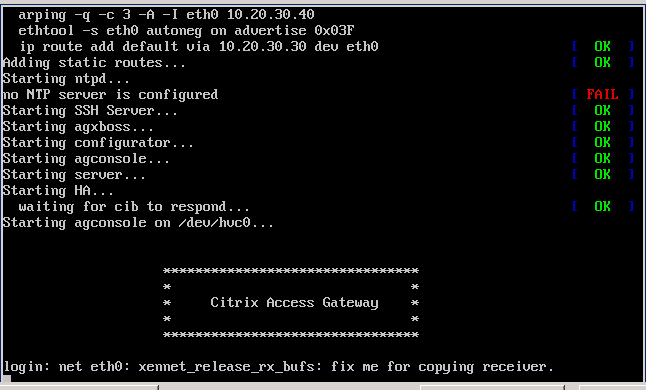
This other screenshot is what I saw on the console that has me stumped, the bit just after login: .... net eth0....
All help is much appreciated.
I just upgraded our Citrix CAG to V5.03 and took a snapshot before and after.
What I realised though is that after updating to V5.03 the IP of the CAG is now 10.20.30.40.
I cannot find where I can modify this to my desired IP. Can someone please point me in the right direction.
I have added a Virtual Network interface as per the other VM's in this environment but can't seem to change the IP so that it is correct.
I have attached a screenshot as well for reference.
This other screenshot is what I saw on the console that has me stumped, the bit just after login: .... net eth0....
All help is much appreciated.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.