LeTay
asked on
nbtstat command access denied on Windows 7
Is it normal to get access denied when issuing the command "nbtstat -R" as a "simple" user on a Windows 7 machine ?
How to fix that ?
How to fix that ?
It looks normal on my Win 7 Pro machine. If you open a command prompt as an Administrator, it works fine.
ASKER
So the questions are : how can a user do it ?
It looks completely ridiculous to create that kind of stupid "security" levels
Windows, as far as security is concerned is really becoming a nightmare !
It looks completely ridiculous to create that kind of stupid "security" levels
Windows, as far as security is concerned is really becoming a nightmare !
You could make them a desktop shortcut to c:\windows\system32\cmd.ex
Either on the above shortcut or location, using the right mouse button & selecting "Properties" also allows a local administrator to modify security settings, etc.
I hope that helps.
Cheers
Ian
P.S. there's also a cmdl32.exe in system32. It's entireley different so please ignore it :-)
Either on the above shortcut or location, using the right mouse button & selecting "Properties" also allows a local administrator to modify security settings, etc.
I hope that helps.
Cheers
Ian
P.S. there's also a cmdl32.exe in system32. It's entireley different so please ignore it :-)
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
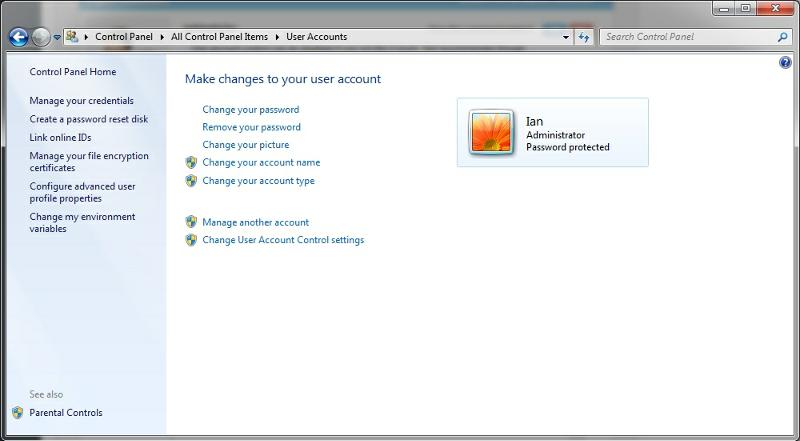
Account control ?
Where can it be disabled please ?
Where can it be disabled please ?
ASKER
What does that exactly mean to "disable user account control" ?
Can you explain in a few word ?
Thanks
Can you explain in a few word ?
Thanks
It basically takes windows 7 back to the same as Windows XP.
That means any changes to your computer don;t ask for permission to execute first & just proceed immediately.
Some items still require administrator action to run.
That means any changes to your computer don;t ask for permission to execute first & just proceed immediately.
Some items still require administrator action to run.
Disabling User Account Control (UAC) is not recommended.
It also won't solve your question about allowing a standard user to run the "nbtstat -R" command. That command and many others that affect the all users on that system will require elevated privileges. You'll have to open the Command Prompt as an Administrator.
It also won't solve your question about allowing a standard user to run the "nbtstat -R" command. That command and many others that affect the all users on that system will require elevated privileges. You'll have to open the Command Prompt as an Administrator.
ASKER
Well, if the user IS NOT administrator, I hope that disabling that stuff does not allow him to do anything on his PC ?
PS : that bl... Windows is becoming, year after year, more and more complex, difficult and, on a security point of view, still like a swiss cheese, full of holes
PS : that bl... Windows is becoming, year after year, more and more complex, difficult and, on a security point of view, still like a swiss cheese, full of holes
Windows has really adopted the idea of user account control from Mac & Linux. They require a password to install new software. At least windows doesn't put us through that.
One day, a malware will try to install on the Win7 pc & the user account control will ask for confirmation. It's 50/50 as to whether that's a benefit as if the malware keeps asking, eventually users get impatient & say yes anyway.
However, I leave user account control on across the board. At least you can advise the users that they chose yes & then they learn for next time.
I'd agree with RootsMan that UAC should stay on unless you have a "really good" reason to disable it.
One day, a malware will try to install on the Win7 pc & the user account control will ask for confirmation. It's 50/50 as to whether that's a benefit as if the malware keeps asking, eventually users get impatient & say yes anyway.
However, I leave user account control on across the board. At least you can advise the users that they chose yes & then they learn for next time.
I'd agree with RootsMan that UAC should stay on unless you have a "really good" reason to disable it.
Considering that Windows tries to have backward comparability to almost windows 98 days because of their huge installed userbase and back then your computer was not connected to the world ever.. just the odd bulletin board now and then and the sysops did their best to ensure that every file that they passed on to their users was virus free (I know because I ran a large one at one time (large being 50 lines and 200G of online storage of which 4G was 4 x 1G SCSI hard drives (cost $1,200 each) and the remainder in cdroms (the readers were $700 each)
Now the world has changed. 24/7 connections to the world is common place in most of the developed world. So instead of turning on your computer and finding it is 'stoned' the bot masters are putting stuff on your pc to make it a spam bot or quietly stealing your personal information and there is huge amounts of money at stake here.. before it was just the amusement of the author with no financial reward.. A typical users information is traded on the black market in lots of hundreds or thousands..
Apple doesn't support their operating systems for that long a period.. Try and get a current O/S for your powerpc mac these days.. it must be an intel mac. the NT platform is only 18 years old and is newer in architecture than BSD Unix which OSX and Linux variants are based upon and they came from a security first, users last environment.
Microsoft has launched their security initiative and is pretty much hardened compared to the past.. it is not a swiss cheese of holes anymore. Considering the amount of money being funnelled in to attack the most used operating system in the world (millions of dollars are at stake) Microsoft is doing a very good job.. Malware authors are attacking other things lately, i.e. 3rd party software i.e. java, pdf readers, flash, and then trying to get users to install their software by using social motivation.
Note: there are still companies that have hardware/software that requires windows 98 or windows NT in order to run and there are requests for help here on Experts-Exchange on a weekly basis on how to integrate these products into the new infastructure.
Just this week we've had requests on how to defeat bitlocker or how to defeat the autorun disable (responsible for conficker) and other how to defeat the security measures put in place. There are constant requests on how to run older software that violates the new order of rules without turning off UAC or asking for elevation of priviledges.
Now that Microsoft has demanded that to get Windows 8 Hardware Logo that computers must use UEFI Secure boot and now the Linux Community is up in arms since this security feature has the capability of locking out computers from using a non-secure boot process. For every level of security there are trade off's the most secure computer is one that is never turned on or sits in isolation from the rest of the world. Practical, not very likely. So it will always be a trade off between useability and security.
Now the world has changed. 24/7 connections to the world is common place in most of the developed world. So instead of turning on your computer and finding it is 'stoned' the bot masters are putting stuff on your pc to make it a spam bot or quietly stealing your personal information and there is huge amounts of money at stake here.. before it was just the amusement of the author with no financial reward.. A typical users information is traded on the black market in lots of hundreds or thousands..
Apple doesn't support their operating systems for that long a period.. Try and get a current O/S for your powerpc mac these days.. it must be an intel mac. the NT platform is only 18 years old and is newer in architecture than BSD Unix which OSX and Linux variants are based upon and they came from a security first, users last environment.
Microsoft has launched their security initiative and is pretty much hardened compared to the past.. it is not a swiss cheese of holes anymore. Considering the amount of money being funnelled in to attack the most used operating system in the world (millions of dollars are at stake) Microsoft is doing a very good job.. Malware authors are attacking other things lately, i.e. 3rd party software i.e. java, pdf readers, flash, and then trying to get users to install their software by using social motivation.
Note: there are still companies that have hardware/software that requires windows 98 or windows NT in order to run and there are requests for help here on Experts-Exchange on a weekly basis on how to integrate these products into the new infastructure.
Just this week we've had requests on how to defeat bitlocker or how to defeat the autorun disable (responsible for conficker) and other how to defeat the security measures put in place. There are constant requests on how to run older software that violates the new order of rules without turning off UAC or asking for elevation of priviledges.
Now that Microsoft has demanded that to get Windows 8 Hardware Logo that computers must use UEFI Secure boot and now the Linux Community is up in arms since this security feature has the capability of locking out computers from using a non-secure boot process. For every level of security there are trade off's the most secure computer is one that is never turned on or sits in isolation from the rest of the world. Practical, not very likely. So it will always be a trade off between useability and security.
ASKER
Well, all that Windows stuff just for execution a trivial command that does not damage anything, nbtstat -R, ping and others ... Unbelievable
Ping & cmd works usually, unless you choose "run as administrator" & then have to click the extra time. You don't have a network administrator applying restrictions do you?