Windows SBS 2008: Windows Backup fails
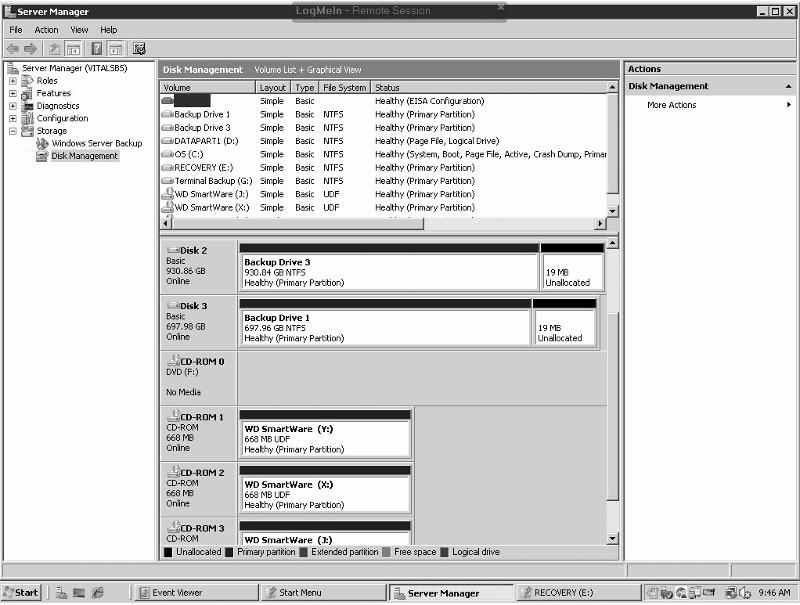
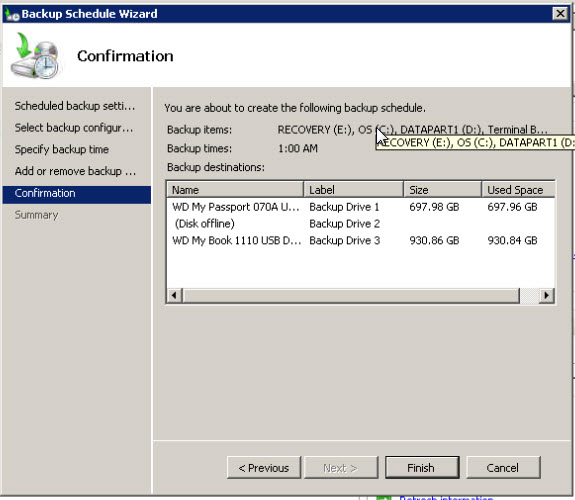
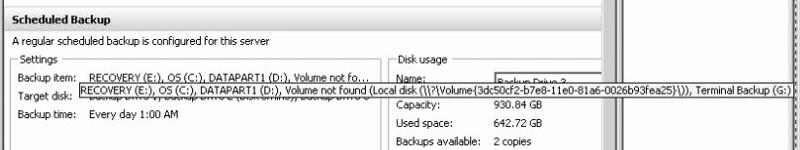
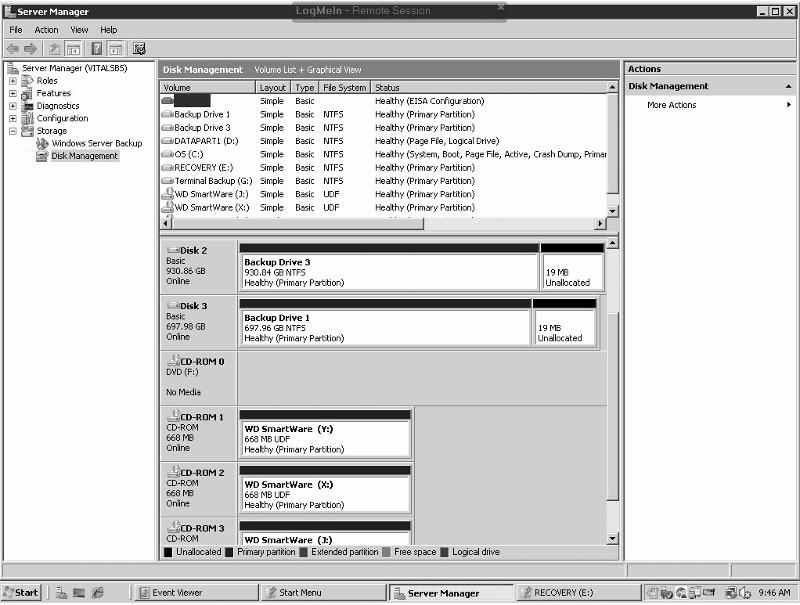
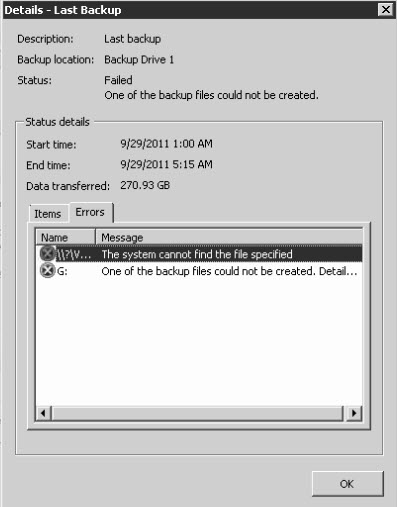
Windows SBS 2008 backup is failing. The server currently uses three different external drives for a backup rotation. All three are WD. Two are USB powered and the other is AC powered. The backup was working at one point.
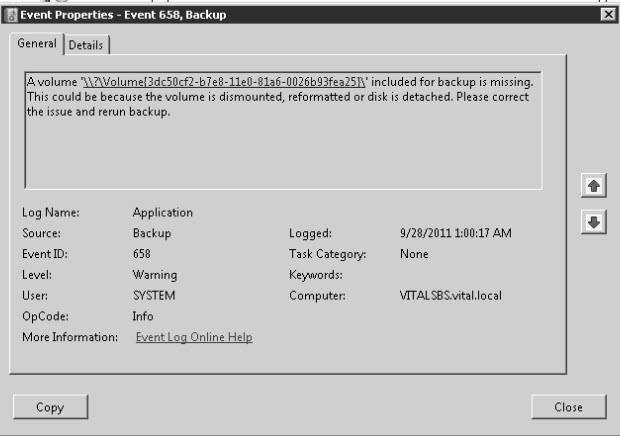
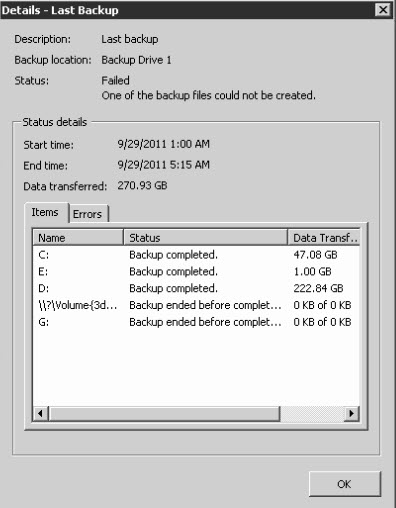
I have different error messages and its difficult to figure out which one is the issue. It looks like the backup maybe starting but not finishing. One of the data points that we backup is our G:\ drive. It is an external drive on the SBS server. We had to replace it and when we mounted a new drive letter to it. It used to be H:\, We reconfigured the backup schedule ot point to G:\. But it looks like it still wants to try and find the old drive letter. It shows a registry key as its path. When I search the registry it has a key that reference H:\.
I have attached a variety of screenshots and logs for your review. I'm not sure what to do.
Thanks
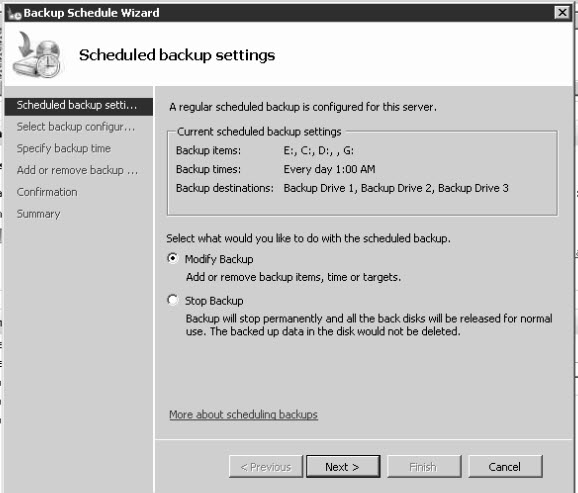
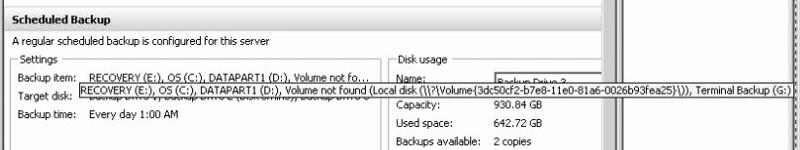
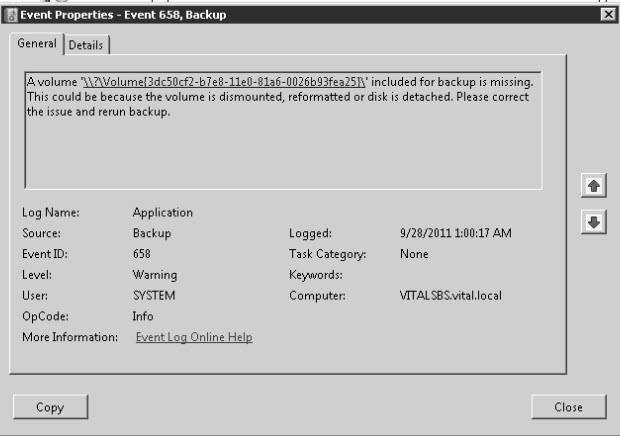
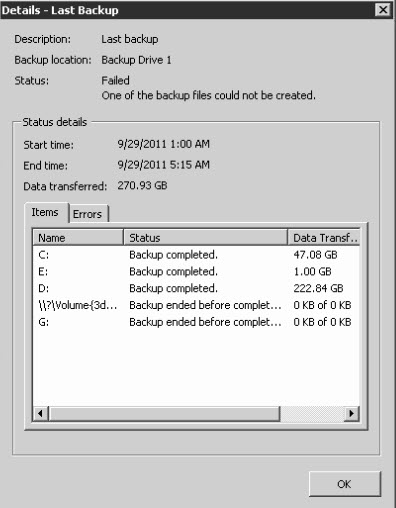
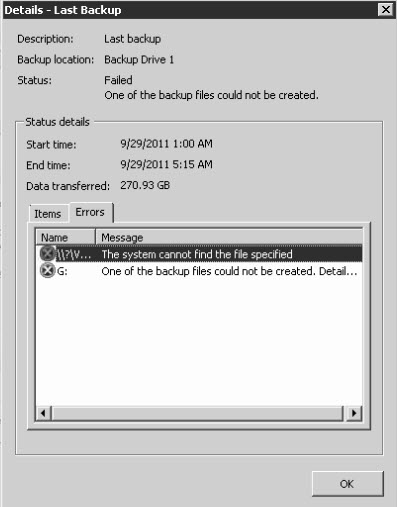
I have different error messages and its difficult to figure out which one is the issue. It looks like the backup maybe starting but not finishing. One of the data points that we backup is our G:\ drive. It is an external drive on the SBS server. We had to replace it and when we mounted a new drive letter to it. It used to be H:\, We reconfigured the backup schedule ot point to G:\. But it looks like it still wants to try and find the old drive letter. It shows a registry key as its path. When I search the registry it has a key that reference H:\.
I have attached a variety of screenshots and logs for your review. I'm not sure what to do.
Thanks
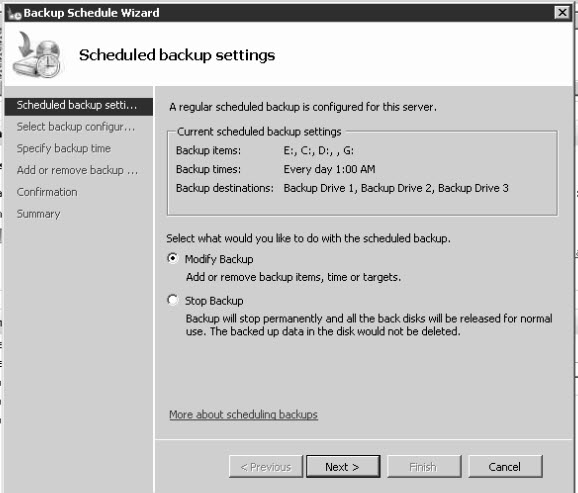
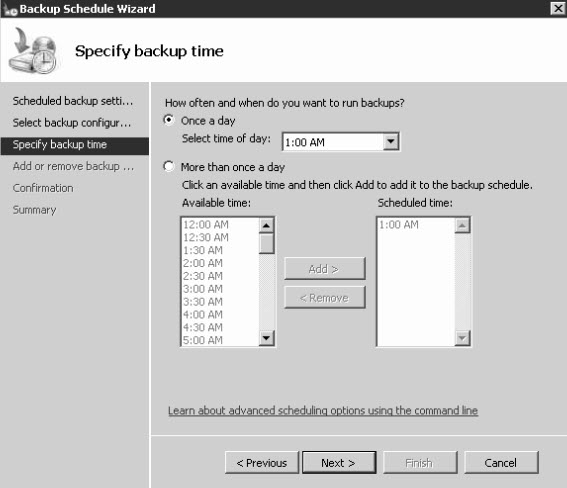
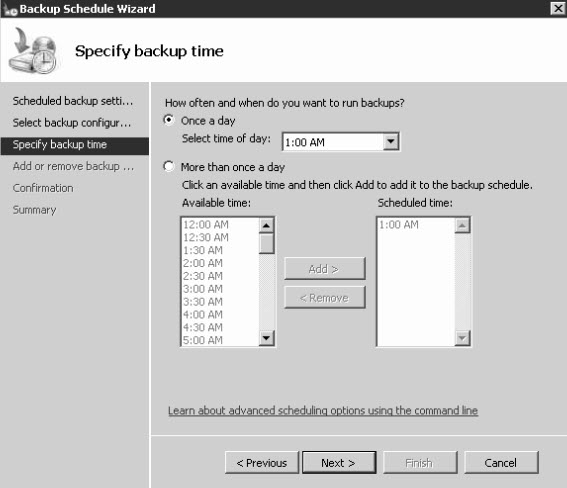
Have you tried deleting the backup config entirely (by clicking the "Disable Backup" link in Small Business Server Console) and re-creating the backup task/schedule from scratch? This will potentially purge any corrupted registry config settings.
ASKER
I have not tried that. I thought disabling would do just that and not delete it. I will try this.
ASKER
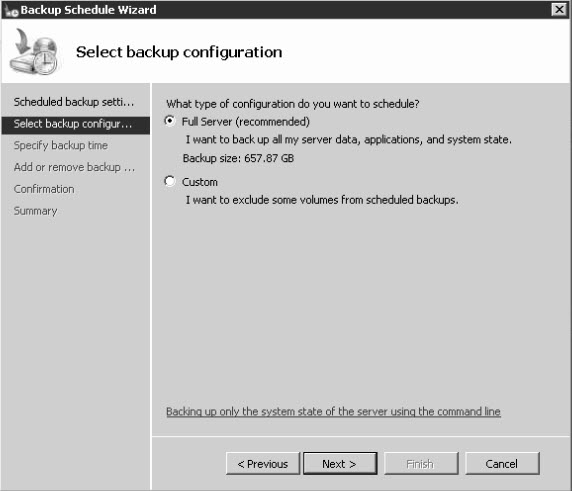
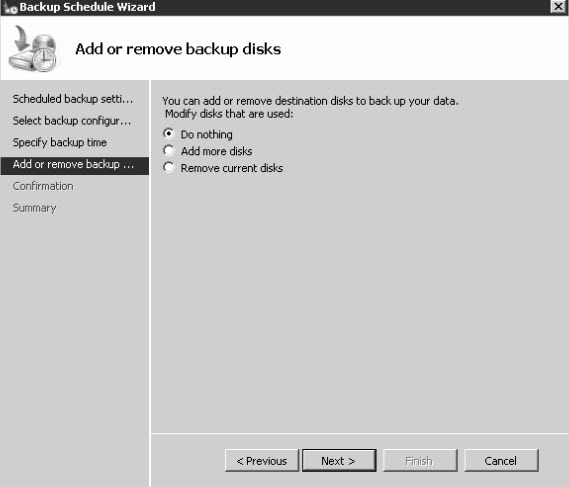
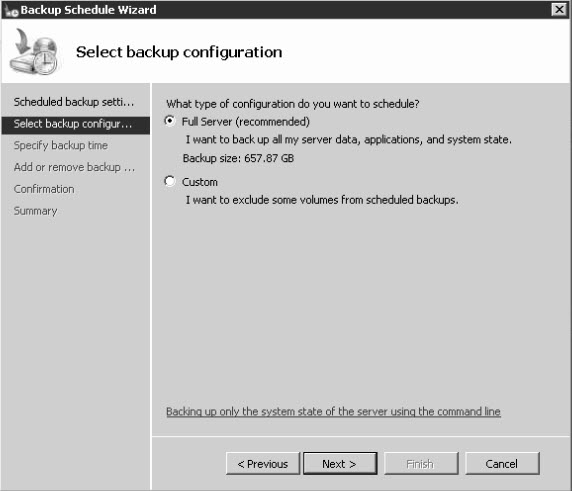
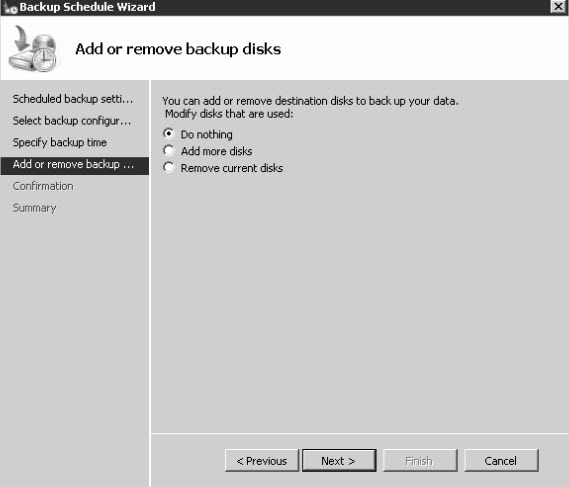
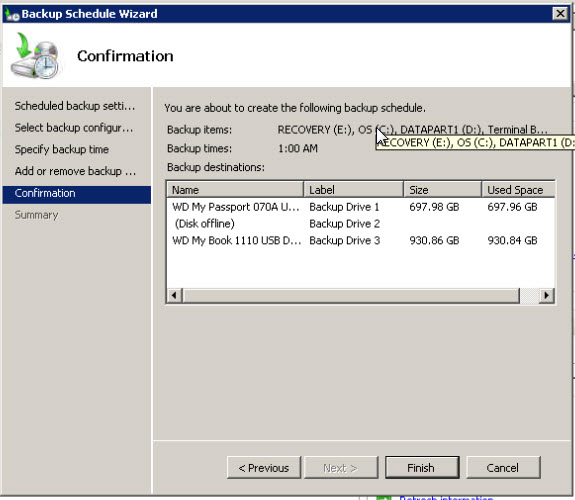
marcus - I went through to configure the backup again and I have a couple of questions. It says that it will format all of my (3) external drives. that will leave me without a backup. Is there a way around that? I was able to select an external drive as part of the backup but now it is not listed. That external data drive was always part of the backup in the past. It is connected and is mounted (G:\). And last, do i have to have all three backup drives that I plan to use connected to the server when I configure the backup?
Thanks
Thanks
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
Hang on, I'm being slow here. If your current backup is still configured and is failing because it can't find \\?\Volume-{3dc50cf2-b7e8-
Otherwise you can try my previous suggestions, however the command there is wrong, you would need:
wbadmin enable backup -exclude:\\?\Volume-{3dc50cf2-b7e8-11e0-81a6-0026b93fea25}\Otherwise you can try my previous suggestions, however the command there is wrong, you would need:
wbadmin enable backup -include:c:,d:,e:,g:ASKER
I'm sorry but I'm a little confused. Which should I run?
wbadmin enable backup -include:c:,d:,e:,g:
or
wbadmin enable backup -exclude:\\?\Volume-{3dc50
or
wbadmin enable backup -include:g:
Thanks
wbadmin enable backup -include:c:,d:,e:,g:
or
wbadmin enable backup -exclude:\\?\Volume-{3dc50
or
wbadmin enable backup -include:g:
Thanks
Sorry, that's my fault for prevaricating.
Run the 'exclude' command, then attempt to run a backup using the 'backup now' button on the SBS console. Let me know how it goes.
Run the 'exclude' command, then attempt to run a backup using the 'backup now' button on the SBS console. Let me know how it goes.
Let me know how it goes.