cc-main
asked on
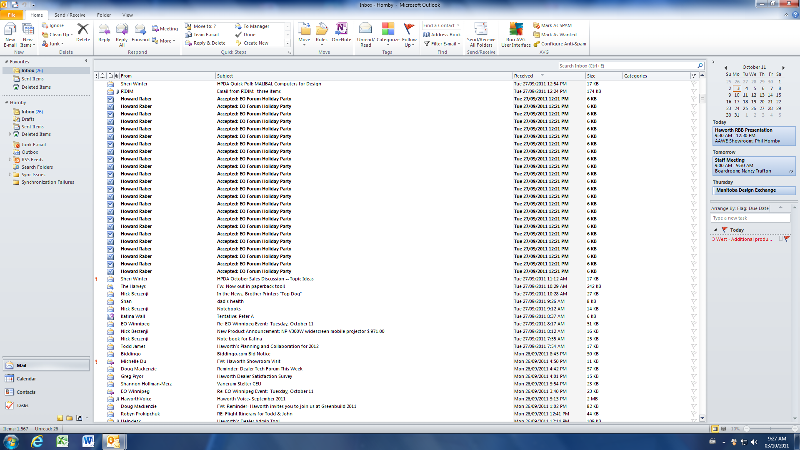
a meeting request and notification of acceptance
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
One more thought here that may help, if the message is actually sent by recipients mobile, should not my clients notebook also receive (and his blackberry) this message. Why just on his desktop? I have even created his same account on my notebook, and I get his normal mail, but that “rogue” message does not come to me, but it does appears as new unread message on his desktop Outlook, dated September 27th12:21PM. Since I send in my question to Exchange, I have about 150 more of them.
ASKER
It was a "sync" issue with ISP provider. They did not provide the deatails but it is fixed.
Thank you for your help.
Nick
Thank you for your help.
Nick
ASKER
Thank you....
ASKER
Thank you for your reply....
Nick