enigmasolutions
asked on
How to browse via router when DNS running on SBS Server is off-line
I have a Windows 2008 small business server running DNS, DHCP, Exchange 2007.
My workstations are set to obtain IP and DNS settigns automatically.
(ie from DNS running on my SBS server - since it provides DHCP and DNS).
If I shut down the SBS server my workstations can't browse the internet.
Is there any way to set up DNS on my SBS server so that when it is off-line then DNS is looked up via the router?
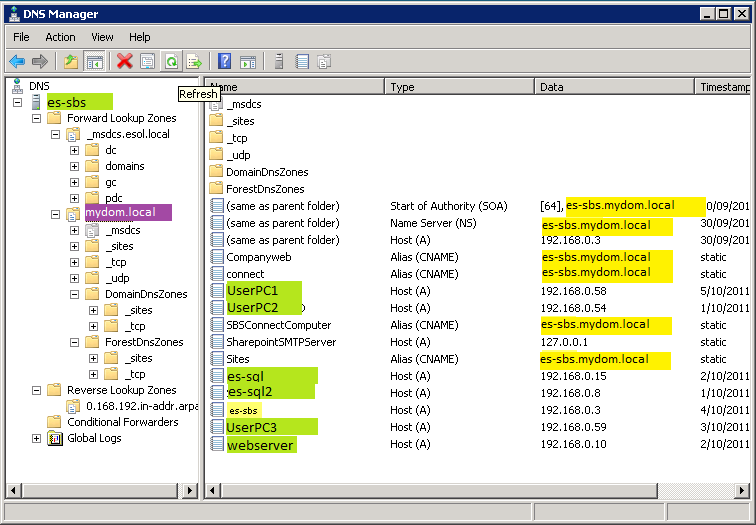
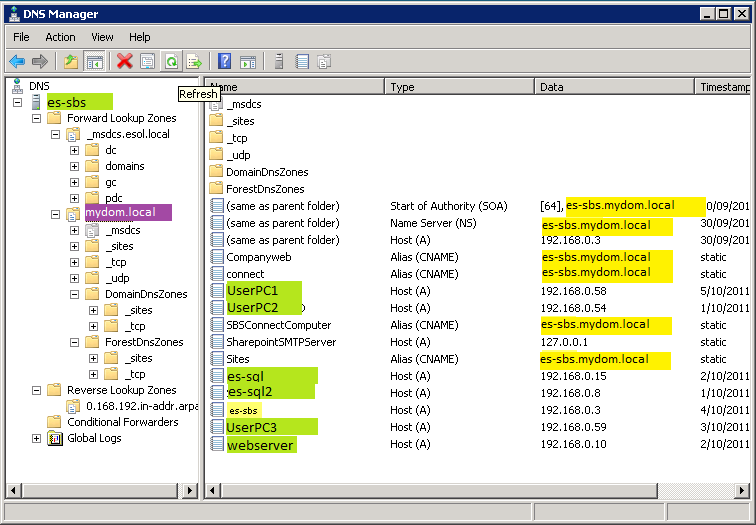
Here is my DNS setup
My workstations are set to obtain IP and DNS settigns automatically.
(ie from DNS running on my SBS server - since it provides DHCP and DNS).
If I shut down the SBS server my workstations can't browse the internet.
Is there any way to set up DNS on my SBS server so that when it is off-line then DNS is looked up via the router?
Here is my DNS setup
In your dhcp settings where you push down the DNS servers, include your ISP dns server as a secondary or tertiary dns server (same as where your server is obtaining its DNS from)
What you could do is change your DHCP Server to hand out two IP addresses for DNS - the first it should hand it is the SBS Server itself, and the second DNS Server IP it should hand out is the Router's. You will have to use DHCP Server on the SBS Server to get this kind of functionality.
ASKER
Yep I thought that would be the answer. Where / how do I set this?
Not knowing which one of us has provided the right answer, I'll show you from my perspective :)
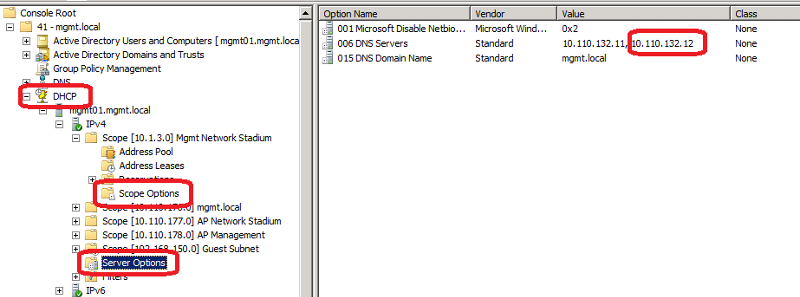
Open up DHCP Manager, add the server if it's not already there, expand IPv4 (if applicable), and then go into Server Options to access the DNS servers, or if you want to affect single scopes, change it in the Scope Options. See Screenshot.
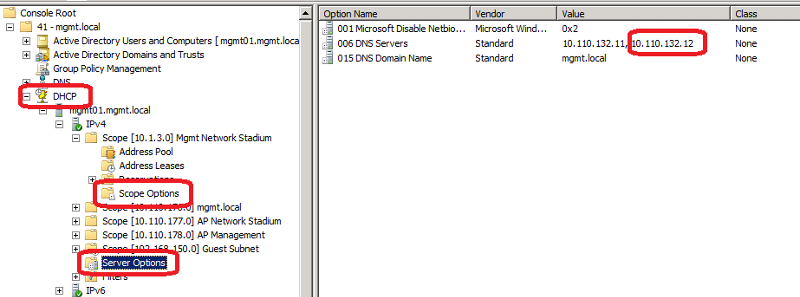
Open up DHCP Manager, add the server if it's not already there, expand IPv4 (if applicable), and then go into Server Options to access the DNS servers, or if you want to affect single scopes, change it in the Scope Options. See Screenshot.
ASKER
Ha I see - I missed seeing the plural... Scope Option(s).
Under Scope options I just had one IP address.
Now I think I will add the Router IP as the second DNS (instead of the ISP DNS) just in case one day I change ISPs and forget to fix this.
Thanks to both of you.
Under Scope options I just had one IP address.
Now I think I will add the Router IP as the second DNS (instead of the ISP DNS) just in case one day I change ISPs and forget to fix this.
Thanks to both of you.
ASKER
Is there any reason why adding the ISP would be prefereable? I can't think of one.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Rob,
You have saved my skin yet again!
I was in agreement with the other guys - and thought they had good answers.
Sorry fellas - but Rob gets the points for providing the correct answer.
But thank you all for your input.
You have saved my skin yet again!
I was in agreement with the other guys - and thought they had good answers.
Sorry fellas - but Rob gets the points for providing the correct answer.
But thank you all for your input.