CA ArcServe r15 Deduplication Purge Problem
Hi There,
We have been running 2 deduplication jobs for about 3 months now on our backup server running Arcserve r15. The jobs were set to purge data after 4 weeks for full backups and 2 weeks for incrementals. The Arcserve DB seems to show that the sessions have in fact been purged, but the storage appliance is running out of room because the session data files have not been deleted. Has anyone had this happen before and does anyone know how to solve it? I need the software to automatically delete the files associated with the purged sessions, as I would imagine it should.
We have been running 2 deduplication jobs for about 3 months now on our backup server running Arcserve r15. The jobs were set to purge data after 4 weeks for full backups and 2 weeks for incrementals. The Arcserve DB seems to show that the sessions have in fact been purged, but the storage appliance is running out of room because the session data files have not been deleted. Has anyone had this happen before and does anyone know how to solve it? I need the software to automatically delete the files associated with the purged sessions, as I would imagine it should.
ASKER
Thanks for the reply. It was set to expedited reclaimation, but the files weren't deleting. Yesterday I tried to see what would happen when I changed that to Delayed, still no result. At some point I need to delete those files. Does the index contain references to files that were created before the purge of sessions occurred? Because I am thinking to just delete some of the older files that are prior to any sessions currently showing in the restoration panel since I have no other choice.
After purging suppose that the files with dates before the last purged session should be deleted, yeah?
After purging suppose that the files with dates before the last purged session should be deleted, yeah?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
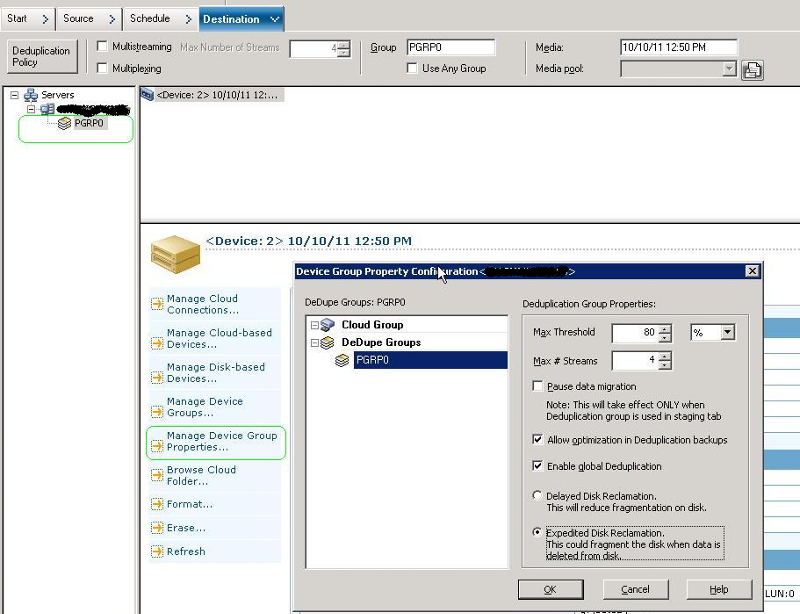
Expedited reclaiming will free up disk space as soon as available. Delayed reclaiming will only free up in idle times or re-use the white spaces for subsequent jobs.
But be aware that expedited reclamation may lead to heavy fragmentation of your volume and eventually impact your IO throughput.