elmtechExpert
asked on
Vmwareplayer-how to Work in Full window size
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
If you are just running the iso, you must first install it to a Virtual Disk inside the player, then install the VMware Tools. Once the tools are installed you should be able to change the resolution of your VM.
ASKER
Hi thanks,
I have done it before with nosuccess.
How can i verify? Is there another way?
I have done it before with nosuccess.
How can i verify? Is there another way?
here you have VM player and you cant install os with it, you need full program to do that, but its not free. Other way is to use virtual box, it free and easy to use. Also you even dont need to set some display settings virtual box will do everything own.
mini tutorial how to use it:
http://onsoftware.en.softonic.com/how-to-install-a-new-operating-system-on-virtualbox
mini tutorial how to use it:
http://onsoftware.en.softonic.com/how-to-install-a-new-operating-system-on-virtualbox
Of course you can install VM's into VMware Player. It is a fully functional virtualization solution.
What have you done before with no success? What exactly didn't you have success with? what were the error messages you got?
What have you done before with no success? What exactly didn't you have success with? what were the error messages you got?
yes you can install, but you cannot create virtual hard drive in VM player.
You can create virtual drives. As I said, it is a fully functional virtualizer with similar features that VBox has. Some of them are better than those of VBox, for example the video 3d support for the graphic card is better than that of VBox, where it is still experimental, so you can run Linux guests with display enhancements on, or Windows 7 with Aero features on, without issues.
oh about that i doesnt knowed.
is there some performance diferencies between VM and virtualbox?
is there some performance diferencies between VM and virtualbox?
there are two ways for you to view in full screen.
1. you can change it to your desired resolution.(mostly equal to the resolution of your physical monitor)
2. then after that, you can press Ctrl + Alt + Enter
--Hope it helps
1. you can change it to your desired resolution.(mostly equal to the resolution of your physical monitor)
2. then after that, you can press Ctrl + Alt + Enter
--Hope it helps
I'm using both, VBox and VMware Player, and haven't really seen any difference in performance, but I haven't done any serious tests. I've just seen that some distro's are easier to install on VBox, while others are easier on VMware. Also, if you are running a Linux Host VBox usually is easier to install on linux and better supported by the distro's repositories.
@asterix,
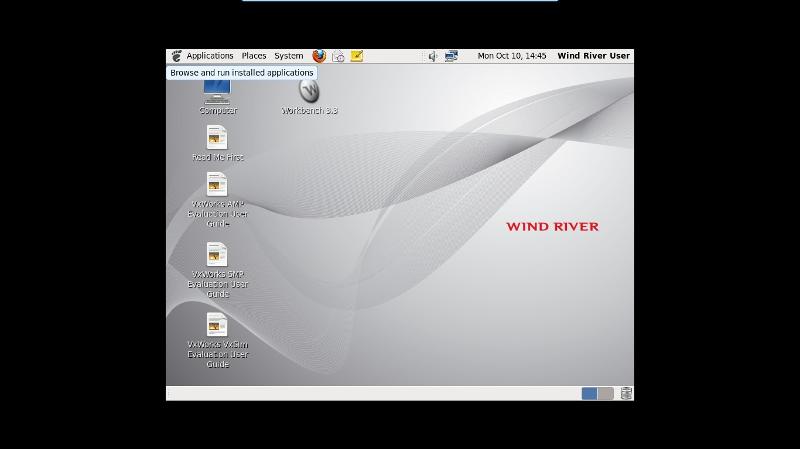
I think he has used ctrl+alt+enter. If I look at the screen shot it looks like the full screen is used, but the VM itself doesn't properly fill it out. That normally means the Video drivers haven't been installed in the VM, and so you can't adjust that resolution away from the defaults.
@asterix,
I think he has used ctrl+alt+enter. If I look at the screen shot it looks like the full screen is used, but the VM itself doesn't properly fill it out. That normally means the Video drivers haven't been installed in the VM, and so you can't adjust that resolution away from the defaults.
ASKER
Hi saimazz,
I have vbox and you said that it will do eberything for me and do not need to chsnge display settings,
This fedora still as same as the screen shot of vmware
Do not apear in full screen.
Please Experts what to do? I can not work in this small window.
Thanks,
Elmtech
I have vbox and you said that it will do eberything for me and do not need to chsnge display settings,
This fedora still as same as the screen shot of vmware
Do not apear in full screen.
Please Experts what to do? I can not work in this small window.
Thanks,
Elmtech
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
I have created virtual machine with no OS:
Create --> other---other .
I have updated the VmWare diffrently and not from guest VmTools....
From File->player prefrences-> "download all componenet"
Thank you,
elmtech
Create --> other---other .
I have updated the VmWare diffrently and not from guest VmTools....
From File->player prefrences-> "download all componenet"
Thank you,
elmtech
ASKER
How to do it?
On Virtual Machine-VM setting ,I can not set\change the resolution.
10x