ISA 2006 to Cisco ASA 5505 IPSEC VPN
Hi all,
recently a remote site of ours moved location and had to have a new VPN router intstalled so I thought to go for Cisco ASA because it was an upgrade over the existing cisco router at the office and was very inexpensive. However I now cannot get IPSEC to bring up a tunel between the remote site and head office.
HO Details:
Local Networks - 192.168.0.0/24, 10.21.21.0/24
ISA 2006 IP - X.X.X.X
Remote Site Details:
Local Networks - 192.168.20.0/24
CISCO ASA [version 8.2(5)] IP - Y.Y.Y.Y
DG at that site: Z.Z.Z.Z
After setting things up at both sides when I pinged from the inside interface of the ASA to the HO inside network. I got the following in the logs:
Routing failed to locate next hop for icmp from NP Identity Ifc:192.168.20.254/0 to inside:192.168.0.1/0
After a reboot of the router I saw the following appear in the logs:
IP = X.X.X.X, IKE Initiator: New Phase 1, Intf inside, IKE Peer X.X.X.X local Proxy Address 192.168.20.0, remote Proxy Address 10.21.21.0, Crypto map (outside_map)
IP = X.X.X.X, Queuing KEY-ACQUIRE messages to be processed when P1 SA is complete.
Then it seems to repeat these log entries after a while.
The ISA server is showing that the remote office is initiating the IPSEC tunnel but after around 5 minutes it shows a status of failed and the tunnel trying to re-initialise.
Both sites are running on the same ISP and initially I thought this could be a block at the ASA end (the ISA currently performs IPSEC tunneling with 4 other remote sites) but I did an NMAP of the remote sites public IP and got the following:
Starting Nmap 5.51 ( http://nmap.org ) at 2011-10-18 18:16 E. Australia Standard Time
Initiating Parallel DNS resolution of 1 host. at 18:16
Completed Parallel DNS resolution of 1 host. at 18:16, 0.04s elapsed
Initiating IPProto Scan at 18:16
Scanning hidden.lnk.telstra.net (Y.Y.Y.Y) [2 ports]
Completed IPProto Scan at 18:16, 3.17s elapsed (2 total ports)
Nmap scan report for hidden.lnk.telstra.net (Y.Y.Y.Y)
Host is up.
PROTOCOL STATE SERVICE
50 open|filtered esp
51 open|filtered ah
Read data files from: C:\Program Files (x86)\Nmap
Nmap done: 1 IP address (1 host up) scanned in 3.25 seconds
Raw packets sent: 4 (80B) | Rcvd: 7 (602B)
I tested this against one of our remote office routers and it matches the results so I am assuming that there is no blocking from the ISP. I also contacted an engineer from Telstra who logged into their router before the ASA and confirmed that there was no block and could see the packets passing through.
I've been through multiple examples online (including some from EE) and just cannot seem to make it work.
--------------------------
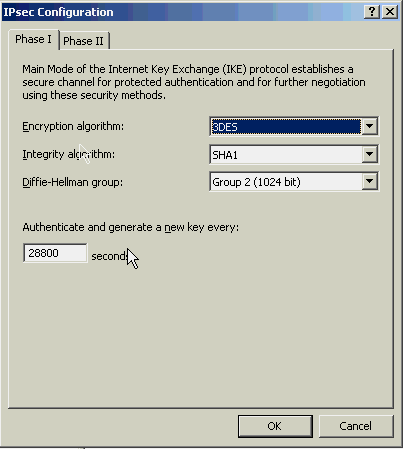
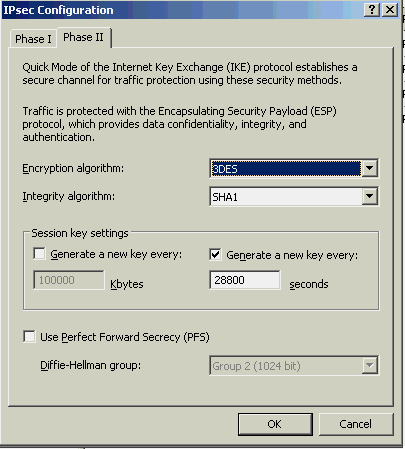
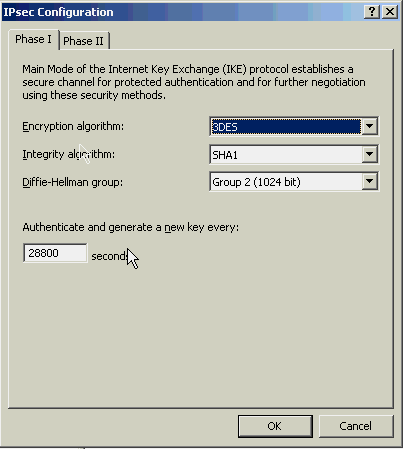
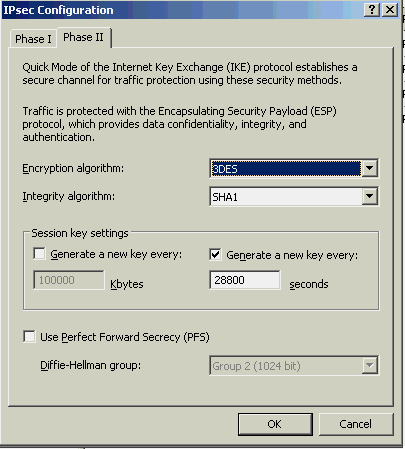
ISA Config:
ASA Config:
--------------------------
(pause for breath)
I am certain that it should be much simpler than this, but unfortunately I just am not seeming to get it.
Can anyone see where I am going wrong or offer advise on how to diagnose this issue further?
recently a remote site of ours moved location and had to have a new VPN router intstalled so I thought to go for Cisco ASA because it was an upgrade over the existing cisco router at the office and was very inexpensive. However I now cannot get IPSEC to bring up a tunel between the remote site and head office.
HO Details:
Local Networks - 192.168.0.0/24, 10.21.21.0/24
ISA 2006 IP - X.X.X.X
Remote Site Details:
Local Networks - 192.168.20.0/24
CISCO ASA [version 8.2(5)] IP - Y.Y.Y.Y
DG at that site: Z.Z.Z.Z
After setting things up at both sides when I pinged from the inside interface of the ASA to the HO inside network. I got the following in the logs:
Routing failed to locate next hop for icmp from NP Identity Ifc:192.168.20.254/0 to inside:192.168.0.1/0
After a reboot of the router I saw the following appear in the logs:
IP = X.X.X.X, IKE Initiator: New Phase 1, Intf inside, IKE Peer X.X.X.X local Proxy Address 192.168.20.0, remote Proxy Address 10.21.21.0, Crypto map (outside_map)
IP = X.X.X.X, Queuing KEY-ACQUIRE messages to be processed when P1 SA is complete.
Then it seems to repeat these log entries after a while.
The ISA server is showing that the remote office is initiating the IPSEC tunnel but after around 5 minutes it shows a status of failed and the tunnel trying to re-initialise.
Both sites are running on the same ISP and initially I thought this could be a block at the ASA end (the ISA currently performs IPSEC tunneling with 4 other remote sites) but I did an NMAP of the remote sites public IP and got the following:
Starting Nmap 5.51 ( http://nmap.org ) at 2011-10-18 18:16 E. Australia Standard Time
Initiating Parallel DNS resolution of 1 host. at 18:16
Completed Parallel DNS resolution of 1 host. at 18:16, 0.04s elapsed
Initiating IPProto Scan at 18:16
Scanning hidden.lnk.telstra.net (Y.Y.Y.Y) [2 ports]
Completed IPProto Scan at 18:16, 3.17s elapsed (2 total ports)
Nmap scan report for hidden.lnk.telstra.net (Y.Y.Y.Y)
Host is up.
PROTOCOL STATE SERVICE
50 open|filtered esp
51 open|filtered ah
Read data files from: C:\Program Files (x86)\Nmap
Nmap done: 1 IP address (1 host up) scanned in 3.25 seconds
Raw packets sent: 4 (80B) | Rcvd: 7 (602B)
I tested this against one of our remote office routers and it matches the results so I am assuming that there is no blocking from the ISP. I also contacted an engineer from Telstra who logged into their router before the ASA and confirmed that there was no block and could see the packets passing through.
I've been through multiple examples online (including some from EE) and just cannot seem to make it work.
--------------------------
ISA Config:
ASA Config:
: Saved
:
ASA Version 8.2(5)
!
hostname ROUTER
domain-name hidden.com.au
enable password .dH9K/LPE1233vSF encrypted
passwd 2KFQ423IdI.2KYOU encrypted
names
!
interface Ethernet0/0
switchport access vlan 2
!
interface Ethernet0/1
!
interface Ethernet0/2
!
interface Ethernet0/3
!
interface Ethernet0/4
!
interface Ethernet0/5
!
interface Ethernet0/6
!
interface Ethernet0/7
!
interface Vlan1
nameif inside
security-level 100
ip address 192.168.20.254 255.255.255.0
!
interface Vlan2
nameif outside
security-level 0
ip address Y.Y.Y.Y 255.255.255.252
!
ftp mode passive
clock timezone EST 10
clock summer-time EDT recurring last Sun Oct 2:00 last Sun Mar 3:00
dns server-group DefaultDNS
domain-name hidden.com.au
object-group network DM_INLINE_NETWORK_1
network-object 10.21.21.0 255.255.255.0
network-object 192.168.0.0 255.255.255.0
access-list outside_1_cryptomap extended permit ip 192.168.20.0 255.255.255.0 object-group DM_INLINE_NETWORK_1
access-list inside_nat0_outbound extended permit ip 192.168.20.0 255.255.255.0 object-group DM_INLINE_NETWORK_1
pager lines 24
logging enable
logging asdm informational
mtu inside 1500
mtu outside 1500
icmp unreachable rate-limit 1 burst-size 1
no asdm history enable
arp timeout 14400
global (outside) 1 interface
nat (inside) 0 access-list inside_nat0_outbound
nat (inside) 1 0.0.0.0 0.0.0.0
route outside 0.0.0.0 0.0.0.0 Z.Z.Z.Z 1
timeout xlate 3:00:00
timeout conn 1:00:00 half-closed 0:10:00 udp 0:02:00 icmp 0:00:02
timeout sunrpc 0:10:00 h323 0:05:00 h225 1:00:00 mgcp 0:05:00 mgcp-pat 0:05:00
timeout sip 0:30:00 sip_media 0:02:00 sip-invite 0:03:00 sip-disconnect 0:02:00
timeout sip-provisional-media 0:02:00 uauth 0:05:00 absolute
timeout tcp-proxy-reassembly 0:01:00
timeout floating-conn 0:00:00
dynamic-access-policy-record DfltAccessPolicy
aaa authentication http console LOCAL
aaa authentication ssh console LOCAL
http server enable
http 0.0.0.0 0.0.0.0 outside
no snmp-server location
no snmp-server contact
snmp-server enable traps snmp authentication linkup linkdown coldstart
crypto ipsec transform-set ESP-AES-128-SHA esp-aes esp-sha-hmac
crypto ipsec transform-set ESP-AES-128-MD5 esp-aes esp-md5-hmac
crypto ipsec transform-set ESP-AES-192-SHA esp-aes-192 esp-sha-hmac
crypto ipsec transform-set ESP-AES-192-MD5 esp-aes-192 esp-md5-hmac
crypto ipsec transform-set ESP-AES-256-SHA esp-aes-256 esp-sha-hmac
crypto ipsec transform-set ESP-AES-256-MD5 esp-aes-256 esp-md5-hmac
crypto ipsec transform-set ESP-DES-SHA esp-des esp-sha-hmac
crypto ipsec transform-set ESP-DES-MD5 esp-des esp-md5-hmac
crypto ipsec transform-set ESP-3DES-MD5 esp-3des esp-md5-hmac
crypto ipsec transform-set ESP-3DES-SHA esp-3des esp-sha-hmac
crypto ipsec security-association lifetime seconds 28800
crypto ipsec security-association lifetime kilobytes 100000
crypto map outside_map 1 match address outside_1_cryptomap
crypto map outside_map 1 set peer X.X.X.X
crypto map outside_map 1 set transform-set ESP-3DES-SHA
crypto map outside_map interface outside
crypto isakmp enable outside
crypto isakmp policy 10
authentication pre-share
encryption 3des
hash sha
group 2
lifetime 28800
telnet timeout 5
ssh 0.0.0.0 0.0.0.0 outside
ssh timeout 60
console timeout 0
dhcpd auto_config outside
!
threat-detection basic-threat
threat-detection statistics access-list
no threat-detection statistics tcp-intercept
webvpn
username root password h9xxnQJB3dM38B7F encrypted privilege 15
tunnel-group X.X.X.X type ipsec-l2l
tunnel-group X.X.X.X ipsec-attributes
pre-shared-key *****
!
!
prompt hostname context
no call-home reporting anonymous
Cryptochecksum:2a9501c2273d9b9d50664439677ccc0f
: end--------------------------
(pause for breath)
I am certain that it should be much simpler than this, but unfortunately I just am not seeming to get it.
Can anyone see where I am going wrong or offer advise on how to diagnose this issue further?
I seen mismatches in VPN tunnels phases. One thing to do is set AES for both sides. I have seen AES tunnel work while a DES or 3DES not.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
resolved ourselves.
ASKER
Could it be possible that ISA2006 and CISCO ASA [version 8.2(5)] have an incompatability when using IPSEC?