tips54
asked on
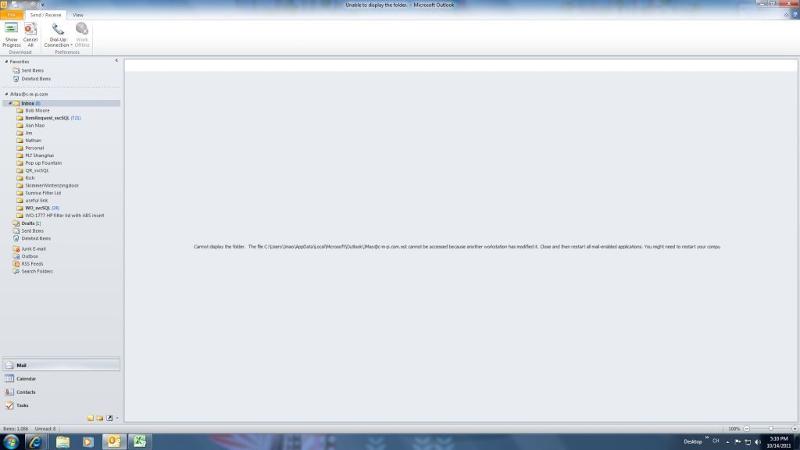
Error in Outlook 2010
The message is not clear, but I think it is referring to the OST file? Close outlook and try deleting that file. Its just where Outlook caches the mailbox, so it will rebuild when you start Outlook again.
Hi,
Have you tried a scan ost or scan pst?
You can find the procedure from MS here:
http://support.microsoft.com/kb/287497
Regards.
Have you tried a scan ost or scan pst?
You can find the procedure from MS here:
http://support.microsoft.com/kb/287497
Regards.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
Close Outlook
start > run > outlook /rpcdiag
Post back a screenshot of rpcdiag
thanks
start > run > outlook /rpcdiag
Post back a screenshot of rpcdiag
thanks
ASKER
I'll try the suggested
ASKER
that did it thanks.