Kelvin Leung
asked on
No datastore available in Vmware Data Recovery?
Hi, I am a bit new to vmware so please bear with me.
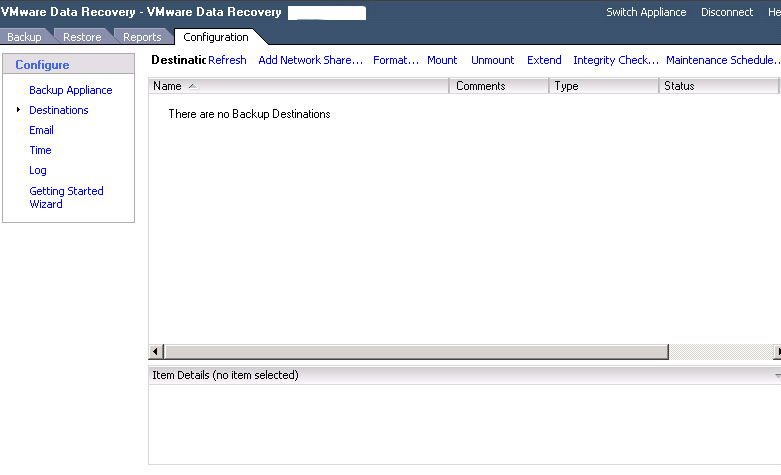
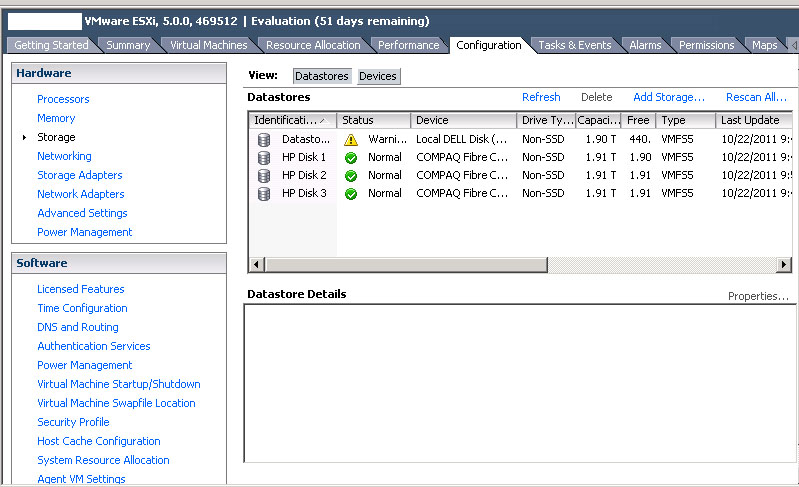
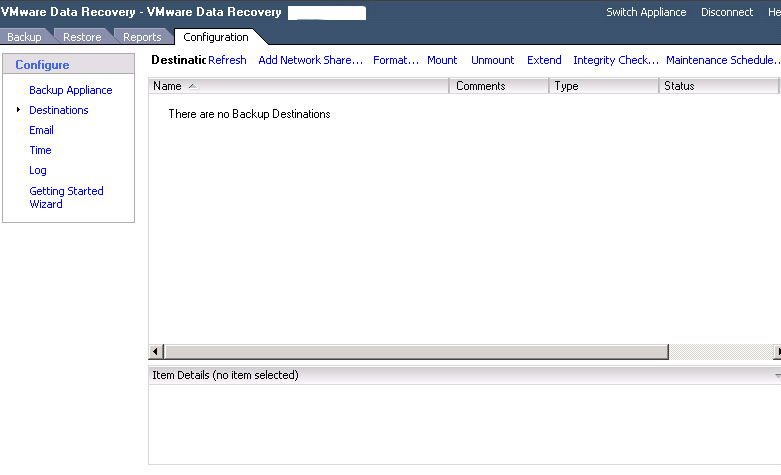
I am trying to setup VMWare Data Recovery 2.0 on my VCenter 5 server to backup my vm's on ESX5 server but for some reason there is no datastore available in backup destinations. But I can see all my datastores available when I try to browse datastore on my ESX5. (both local datastore and 3 datastores we have in our HP MSA1000 SAN (Fiber Channel). (See screenshots)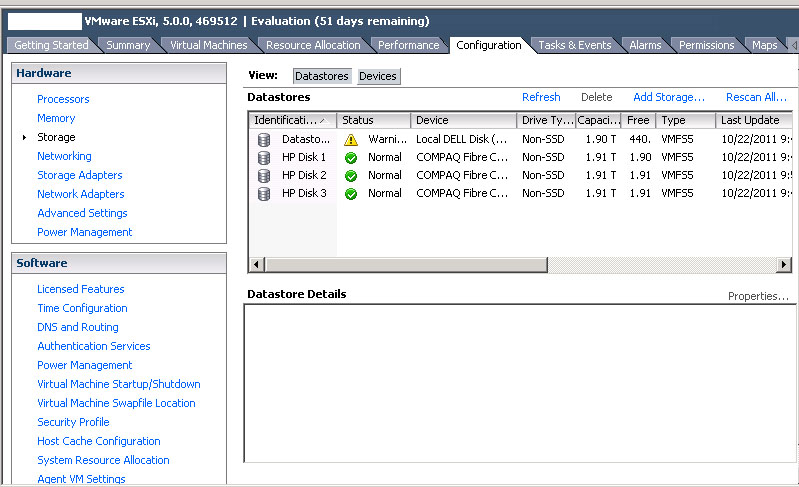
Hardware in our enviroment:
HP MSA1000 SAN (Fiber Channel) directly attached to ESX5
3x Virtual Disks on the SAN. 1.91TB each formatted as VMFS5. (They are all unused)
1x Local Datastore on ESX5 (This is pretty full, still have approx 400GB left)
Software version:
VCenter 5
ESX5
VmWare Data Recovery 2.0
I would be really appreciated if someone can help me to troubleshoot this problem.
Thank you.
I am trying to setup VMWare Data Recovery 2.0 on my VCenter 5 server to backup my vm's on ESX5 server but for some reason there is no datastore available in backup destinations. But I can see all my datastores available when I try to browse datastore on my ESX5. (both local datastore and 3 datastores we have in our HP MSA1000 SAN (Fiber Channel). (See screenshots)
Hardware in our enviroment:
HP MSA1000 SAN (Fiber Channel) directly attached to ESX5
3x Virtual Disks on the SAN. 1.91TB each formatted as VMFS5. (They are all unused)
1x Local Datastore on ESX5 (This is pretty full, still have approx 400GB left)
Software version:
VCenter 5
ESX5
VmWare Data Recovery 2.0
I would be really appreciated if someone can help me to troubleshoot this problem.
Thank you.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Dear hanccocka, Thank you so much for your help. This was extremely helpful and exactly what we needed.
http://pubs.vmware.com/vsphere-50/topic/com.vmware.ICbase/PDF/vmware-data-recovery-administrators-guide-20.pdf
(please also note that your MSA1000 is not on the Hardware Compatability List for ESXi 5.0)