StarfishTech
asked on
Restoring Exchange Mailbox in Backup Exec 11d
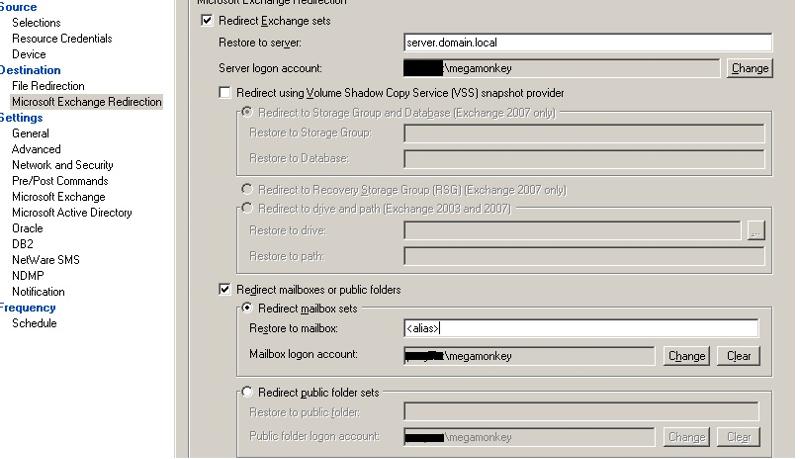
Hello, we are trying to restore an exchange 2003 mailbox that was accidentally deleted. We were running granular backups of each mailbox so we are able to choose the exact mailbox that we want to restore. Backup exec stages the entire store no problem but in then eventually fails saying "0xe000848c - unable to attach to a resource". I've looked at the server and the mailbox isn't there obviously but the user account is still intact. I also tested the credentials before I ran the restore and they succeeded. Please let me know what we need to do to get this restore to work. Thank you.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Unfortunately the retention expired long ago.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Thank you. Do you know what the mailbox name should be? Would it be how it shows up under the Mailbox column in ESM, could it be the alias, etc?
No, must be a mailbox. Delete them and recreate again from console if your Exchange is 2007/2010 or from Active directory if Exchange is 2003
ASKER
What I mean is BEX asks for the mailbox name in "restore to mailbox". Does it actually want the mailbox name as it shows up in the mailbox column of ESM (Lastname, Firstname) or is it looking for something else here like the Alias name of the mailbox?
Try using the alias of mailbox
ASKER
This is quite strange.
I has restored emails using this way on past. The logon account has administrative privileges?
I has restored emails using this way on past. The logon account has administrative privileges?
How long ago was the mailbox deleted? What time limit do you have setup for deleted mailbox recovery?
JJ