intear
asked on
Can't Migrate Local Users on Server 2003 to Server 2008 Server
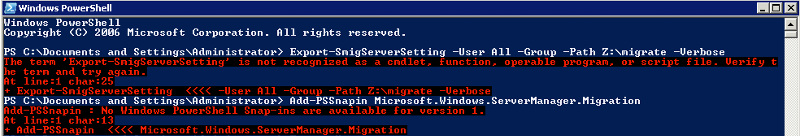
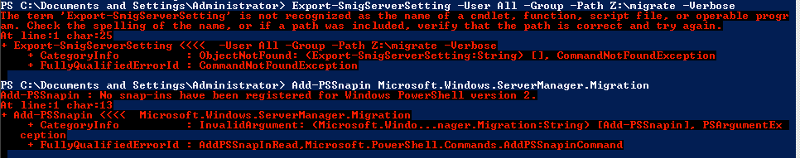
I am trying to migrate local users from a Windows Server 2003 SP2 32bit server to a Windows Server 2008 Enterprise R2 server.
I have installed powershell on the source server and am getting an error message when running the Export-SmigServerSetting cmdlet per the following article:
http://technet.microsoft.com/en-us/library/dd379531(WS.10).aspx#BKMK_unsuppatt
Attached is a screenshot of the error I am receiving.
Any ideas?
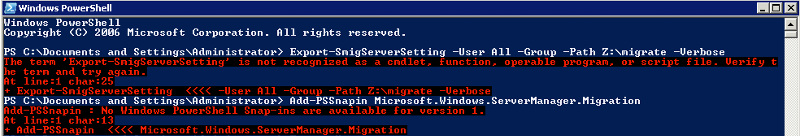
I have installed powershell on the source server and am getting an error message when running the Export-SmigServerSetting cmdlet per the following article:
http://technet.microsoft.com/en-us/library/dd379531(WS.10).aspx#BKMK_unsuppatt
Attached is a screenshot of the error I am receiving.
Any ideas?
ASKER
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
I was able to create a deployment package from the source server and it worked great. Thanks for your help.
Thanks.
mug