How to setup secure FTP site on IIS7
Hi everyone,
I have a secure website setup on a Server 2008 running IIS7. I also have an SSL certificate already purchased and installed on the webserver for the secure website. Now, I am trying to setup an FTP site on the same server, is it possible to use the same SSL certificate that I have purchased for the website for FTP site as well?
- Could you please give me some steps or provide me with some directions for setting up a secure FTP site on IIS7?
Thanks for your help in advance!
I have a secure website setup on a Server 2008 running IIS7. I also have an SSL certificate already purchased and installed on the webserver for the secure website. Now, I am trying to setup an FTP site on the same server, is it possible to use the same SSL certificate that I have purchased for the website for FTP site as well?
- Could you please give me some steps or provide me with some directions for setting up a secure FTP site on IIS7?
Thanks for your help in advance!
The web page linked does not include SSL, so I will provide some additional screenshots.
Start off by setting up a standard FTP site, as per the guide linked, and then go into FTP SSL Settings to choose your Certificate and other SSL settings.
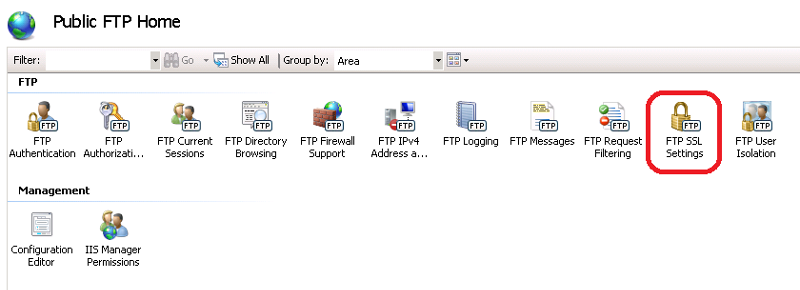 First off, select FTP SSL from the Home page of your FTP Site
First off, select FTP SSL from the Home page of your FTP Site
 Secondly, use the drop down to select your SSL Certificate already installed for your web site, and then choose your SSL Security Setting - explained as follows:
Secondly, use the drop down to select your SSL Certificate already installed for your web site, and then choose your SSL Security Setting - explained as follows:
If it interests you, I have also written an article entitled "Make your FTP Server support Active and Passive" available on Experts Exchange at https://www.experts-exchange.com/A_7833.html
Start off by setting up a standard FTP site, as per the guide linked, and then go into FTP SSL Settings to choose your Certificate and other SSL settings.
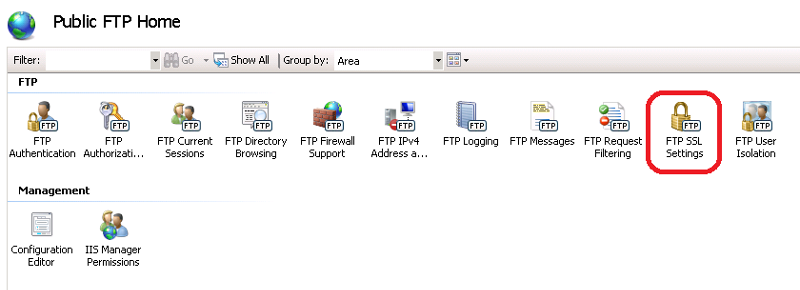 First off, select FTP SSL from the Home page of your FTP Site
First off, select FTP SSL from the Home page of your FTP Site Secondly, use the drop down to select your SSL Certificate already installed for your web site, and then choose your SSL Security Setting - explained as follows:
Secondly, use the drop down to select your SSL Certificate already installed for your web site, and then choose your SSL Security Setting - explained as follows:
Allow SSL connections - will allow clean or encrypted connections
Require SSL connecitons - will require Encryption on both the control channel and data channel
Custom - allows you to choose which channels to force encrypt
Use 128-bit encryption for SSL connections - if you are exporting encryption, use this. This means, if people outside of your country are connecting, and there are encryption export laws limiting you to 128 bit encryption, you should use this. Nobody does though.
If it interests you, I have also written an article entitled "Make your FTP Server support Active and Passive" available on Experts Exchange at https://www.experts-exchange.com/A_7833.html
"The web page linked does not include SSL..."
I beg to differ.
I beg to differ.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Thank you both Paulmacd and LesterClayton for your posts! I will review them and get back to you. Do you off the top if internet explorer, firefox, google chrome, safari support secure ftp or simple ftp protocol?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Thanks Paulmacd. I will check the other ones.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Thanks everyone for your feedback on this post.
http://learn.iis.net/page.aspx/310/what-is-new-for-microsoft-and-ftp-in-iis-7/