Need help resolving aggregate function error in totals query in Access.
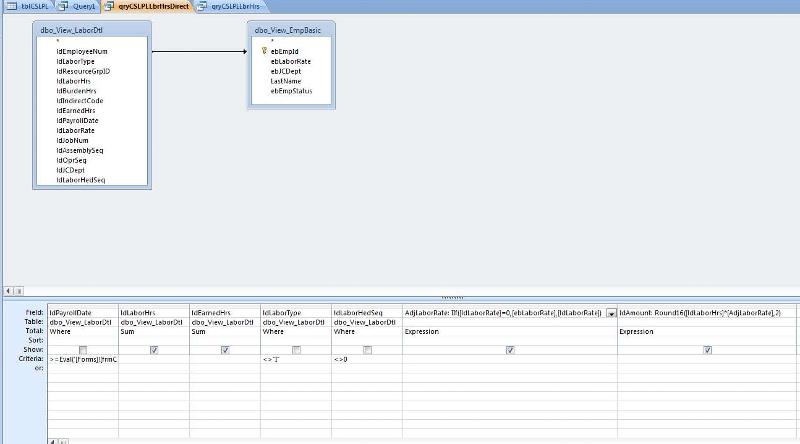
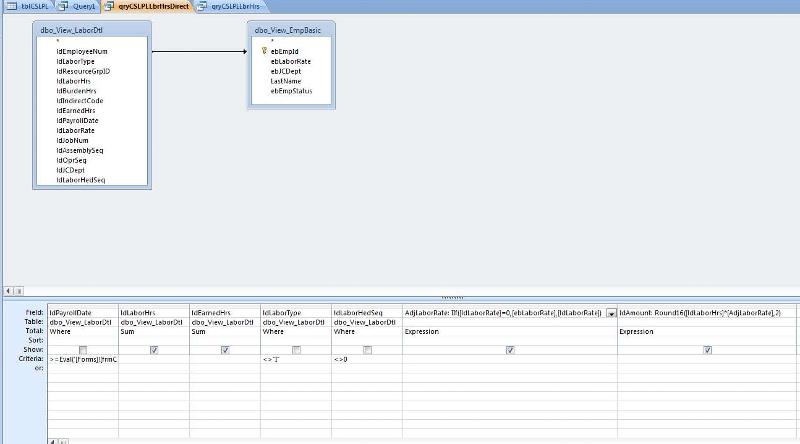
Here is the query I'm trying to run;
Here is the sql;
SELECT Sum(dbo_View_LaborDtl.ldLa
Sum(dbo_View_LaborDtl.ldEa
IIf([ldLaborRate]=0,[ebLab
Round16([ldLaborHrs]*[AdjL
FROM dbo_View_LaborDtl
LEFT JOIN dbo_View_EmpBasic
ON dbo_View_LaborDtl.ldEmploy
WHERE (((dbo_View_LaborDtl.ldPay
And (dbo_View_LaborDtl.ldPayro
AND ((dbo_View_LaborDtl.ldLabo
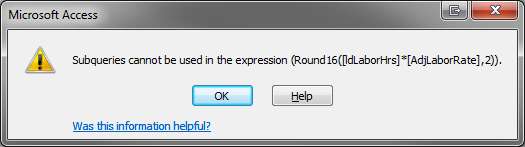
And here is the error I'm getting;

Thanks in advance for the help!
Here is the sql;
SELECT Sum(dbo_View_LaborDtl.ldLa
Sum(dbo_View_LaborDtl.ldEa
IIf([ldLaborRate]=0,[ebLab
Round16([ldLaborHrs]*[AdjL
FROM dbo_View_LaborDtl
LEFT JOIN dbo_View_EmpBasic
ON dbo_View_LaborDtl.ldEmploy
WHERE (((dbo_View_LaborDtl.ldPay
And (dbo_View_LaborDtl.ldPayro
AND ((dbo_View_LaborDtl.ldLabo
And here is the error I'm getting;

Thanks in advance for the help!
try replacing "Expression" with "Last" or "First"
ASKER
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
That works! Thanks for the help!
a pleasure, and thanks for the points
ASKER
No problem!
SELECT Sum(dbo_View_LaborDtl.ldLa
Sum(dbo_View_LaborDtl.ldEa
Sum(IIf([ldLaborRate]=0,[e
Sum(Round16([ldLaborHrs]*[
FROM dbo_View_LaborDtl
LEFT JOIN dbo_View_EmpBasic
ON dbo_View_LaborDtl.ldEmploy
WHERE (((dbo_View_LaborDtl.ldPay
And (dbo_View_LaborDtl.ldPayro
AND ((dbo_View_LaborDtl.ldLabo