How can I create an IIS provider for SQL Server?
I have a backup (failover) server that is missing a provider in IIS. I have all the provider parameters except the type. I know the type for the Provider should be MS SQL server, but there must be some specific systax I should use for this to work. See attached images.
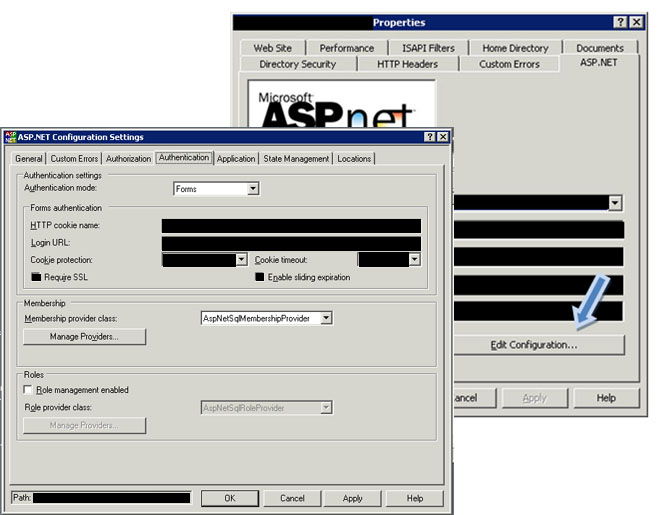 This image is of the Properties of my web site in IIS. On the APS.NET tab I click 'Edit Coonfiguration..' which open the ASP.NET Configuration Settings. Within this window I click 'Authentication' tab. About the middle of the window is a button 'Manage Providers'.
This image is of the Properties of my web site in IIS. On the APS.NET tab I click 'Edit Coonfiguration..' which open the ASP.NET Configuration Settings. Within this window I click 'Authentication' tab. About the middle of the window is a button 'Manage Providers'.
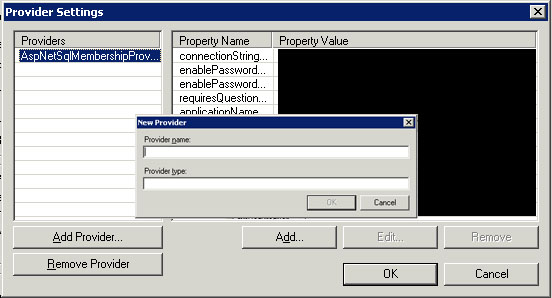 When I click 'Manage Providers' a new window opens for 'Provider Settings'. I need to create a new Provider so I click 'Add Provider' and I am prompted for the 'Provider name' and 'Provider Type' The problem I have is that I don't know the correct systax to refer to the SQL Server for the Provider Type field. What is the correct syntax for valid values for the Provider Type?
When I click 'Manage Providers' a new window opens for 'Provider Settings'. I need to create a new Provider so I click 'Add Provider' and I am prompted for the 'Provider name' and 'Provider Type' The problem I have is that I don't know the correct systax to refer to the SQL Server for the Provider Type field. What is the correct syntax for valid values for the Provider Type?
Any help is appreciated.
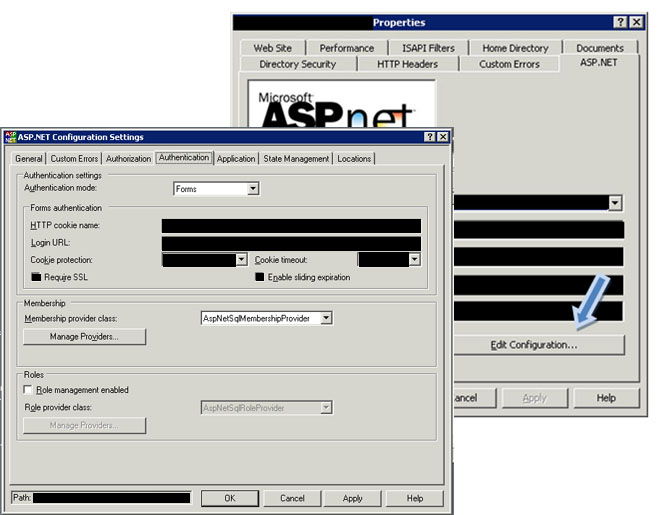 This image is of the Properties of my web site in IIS. On the APS.NET tab I click 'Edit Coonfiguration..' which open the ASP.NET Configuration Settings. Within this window I click 'Authentication' tab. About the middle of the window is a button 'Manage Providers'.
This image is of the Properties of my web site in IIS. On the APS.NET tab I click 'Edit Coonfiguration..' which open the ASP.NET Configuration Settings. Within this window I click 'Authentication' tab. About the middle of the window is a button 'Manage Providers'.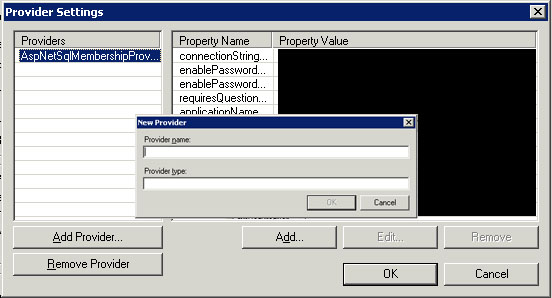 When I click 'Manage Providers' a new window opens for 'Provider Settings'. I need to create a new Provider so I click 'Add Provider' and I am prompted for the 'Provider name' and 'Provider Type' The problem I have is that I don't know the correct systax to refer to the SQL Server for the Provider Type field. What is the correct syntax for valid values for the Provider Type?
When I click 'Manage Providers' a new window opens for 'Provider Settings'. I need to create a new Provider so I click 'Add Provider' and I am prompted for the 'Provider name' and 'Provider Type' The problem I have is that I don't know the correct systax to refer to the SQL Server for the Provider Type field. What is the correct syntax for valid values for the Provider Type?Any help is appreciated.
SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Thank You for your help!