sglee
asked on
Screenshot Software
Hi,
I used to have Screenshot software working on my XP computer.
I just try to install it on my NEW Windows 7 64bit PC, but it fails due to incompatibility.
The software is made by Parsons Technology, but apparently they no longer exist in the market.
Is there a software that I can either download for FREE or PAID where I can press one key on the keyboard to have everything on the monitor to print immediately?
Thanks.
I used to have Screenshot software working on my XP computer.
I just try to install it on my NEW Windows 7 64bit PC, but it fails due to incompatibility.
The software is made by Parsons Technology, but apparently they no longer exist in the market.
Is there a software that I can either download for FREE or PAID where I can press one key on the keyboard to have everything on the monitor to print immediately?
Thanks.
Use the Snipping tool included with Windows7. Start > All Programs > Accessories > Snipping Tool.
Check this out, it may be all you need.
http://windows.microsoft.com/en-US/windows7/products/features/snipping-tool
http://windows.microsoft.com/en-US/windows7/products/features/snipping-tool
Like people saying Snipping tool does a great job for most people.
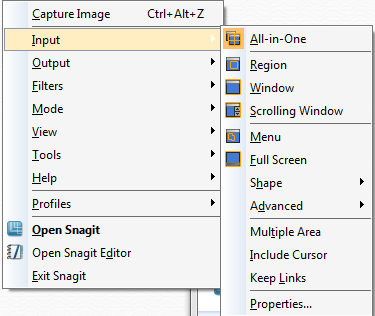
But I use Snagit, its the best program I have found for this.
But I use Snagit, its the best program I have found for this.
ASKER
Thanks for the suggestions.
All of them have everything that I am looking for except ONE THING:
With Screenshot by Parsons Technology, I Just press [Print] key on the keyboard in order to print what is on the screen period. There is no need to capture/save or go to File/Print.
All of them have everything that I am looking for except ONE THING:
With Screenshot by Parsons Technology, I Just press [Print] key on the keyboard in order to print what is on the screen period. There is no need to capture/save or go to File/Print.
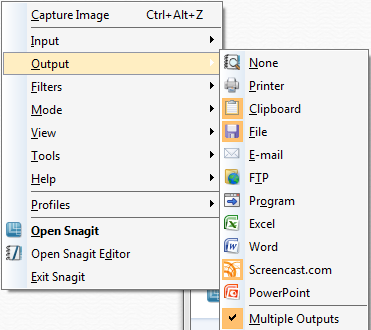
With snagit you can automatically send straight to a printer if you wish.
You can also setup what every hotkey you want to invoke the software, i use ctrl+alt+z as its a nice 3 finger combo.
You can also setup what every hotkey you want to invoke the software, i use ctrl+alt+z as its a nice 3 finger combo.
ASKER
With snagit you can automatically send straight to a printer if you wish. --->
so, no need to select the area to print or save the image in JPG format and print?
Just one button on the keyboard and it will print what is on the screen?
so, no need to select the area to print or save the image in JPG format and print?
Just one button on the keyboard and it will print what is on the screen?
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
Thanks you for suggesting GadWin Print Screen. It is truly simply. Just press [Print Scrn] key on the keyboard and click on [Continue Output ]. Thanks it!
I also appreciate all other suggestions. They were functional, but requires too many extra steps to print the entire image of the screen.
I also appreciate all other suggestions. They were functional, but requires too many extra steps to print the entire image of the screen.
I believe they also have a free version, but I have the paid version. it does all kinds of thig well.
http://www.ntwind.com/software/winsnap.html