Windows 8 / IE 10 - do not track - EE does not work well but everything else is GREAT
EE display is messy and BACK does not work
However I will accept the compromise.
IE10 is BLAZINGLY fast.
Windows 8 is super clean - no clutter - no eye candy - no need to get a new graphic card, probably you can get the one you used for XP out!
Pro has the desktop, you will take 10 minutes to adapt.
EE might take longer
However I will accept the compromise.
IE10 is BLAZINGLY fast.
Windows 8 is super clean - no clutter - no eye candy - no need to get a new graphic card, probably you can get the one you used for XP out!
Pro has the desktop, you will take 10 minutes to adapt.
EE might take longer
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
well EE is not fixed yet, but it is useable if not beautiful so we can let this go.
ASKER
I'm using dual 23" monitors. It's not a quality problem.
I don't really want to keep having to put things in compatibility mode. IE10 has been in beta for ages now.
I don't really want to keep having to put things in compatibility mode. IE10 has been in beta for ages now.
@carolchi - Thanks. Maybe Microsoft will improved Windows 8 and IE10 before final release.
... Thinkpads_User
... Thinkpads_User
ASKER
As far as I know the version I am using (MSDN RTM) is the final version.
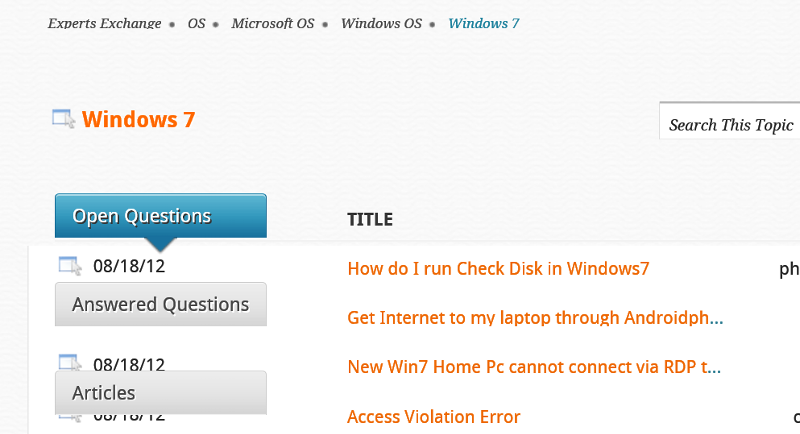
I run Windows 8 in a Virtual Machine. The VM is windowed (not full-screen) and the display is 1024x768. E-E has some display overlap errors in that resolution, at least for IE 10.
... Thinkpads_User