Trying to install Windows Storage server 2008 from img file using GPT file system on a Dell NX3000 NAS Box
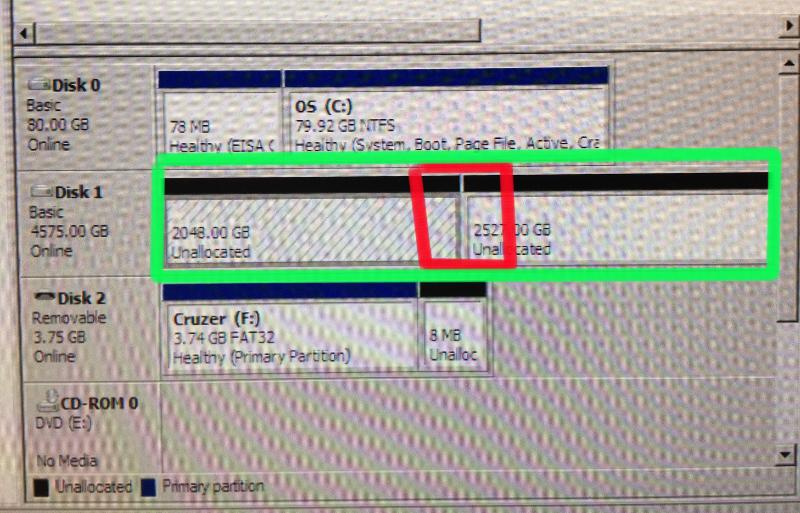
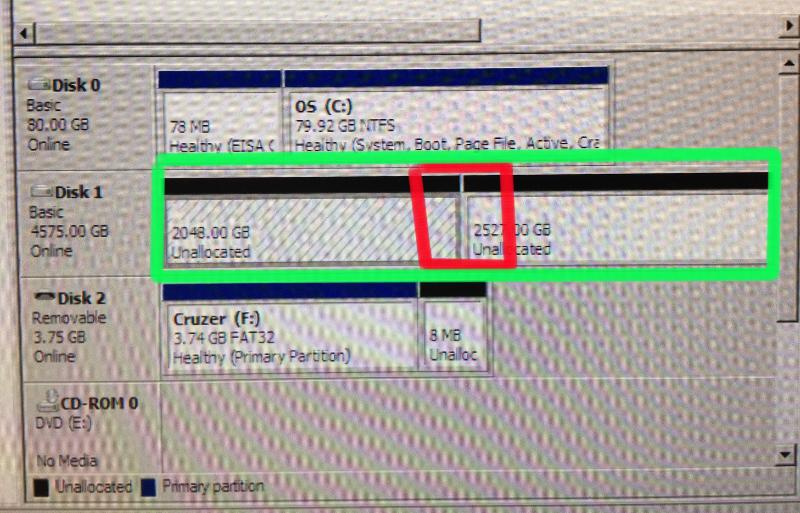
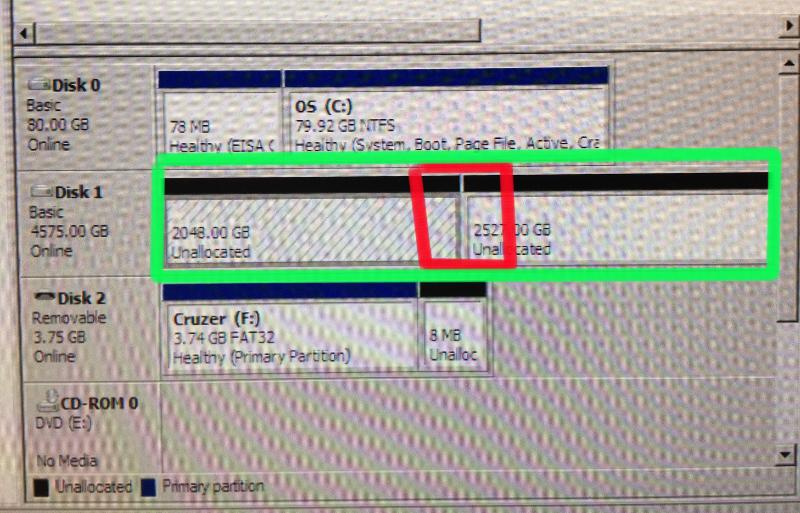
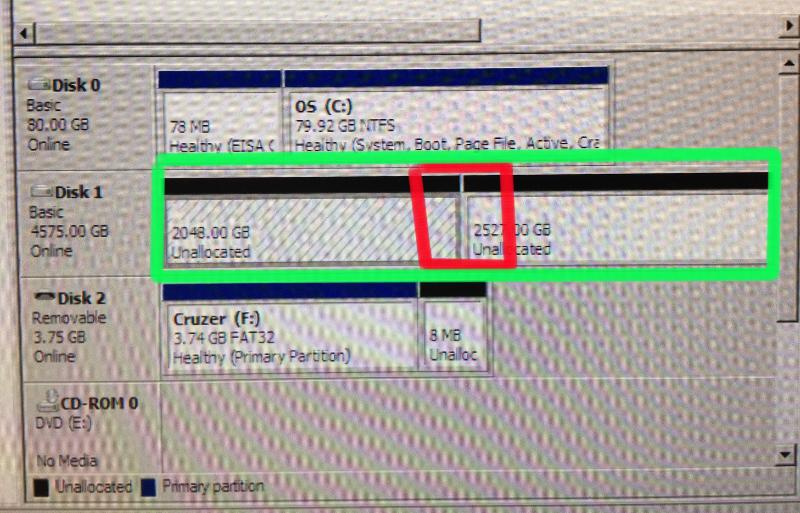
I’m Trying to install Windows Storage server 2008 from img file using GPT file system on a Dell NX3000 NAS Box. The installer from Dell will only do it as NTFS. It gives me no choice between NTFS and GPT. It is all one 6TB RAID 5 partitioned with a 80GB OS and the data partition has been divided up into two partitions because it is NTFS as well.
I think that need the RAID needs to be setup in The BIOS or other utility during POST.
Please help as this is a mission critical machine that has been down for a week.
See attached jpg
As usual Thanks in advance EE community!!
jpertchik
I think that need the RAID needs to be setup in The BIOS or other utility during POST.
Please help as this is a mission critical machine that has been down for a week.
See attached jpg
As usual Thanks in advance EE community!!
jpertchik
ASKER CERTIFIED SOLUTION
membership
This solution is only available to members.
To access this solution, you must be a member of Experts Exchange.
ASKER
This guy got back to me QUICKLY!
Thanks EE community!
jperthik
Thanks EE community!
jperthik
ASKER
I'll let you know what happens after I work with them. Your information might be something that they have overlooked in the past. I've had the same problem for a week now and have worked with several technicians.
As always when I consult the EE community, thank you so much for your insight!
You rule,
jpertchik